

Rewterz Threat Advisory – CVE-2019-4591 – IBM Maximo Asset Management security bypass
July 14, 2020
Rewterz Threat Alert – M00nD3V Logger
July 14, 2020
Rewterz Threat Advisory – CVE-2019-4591 – IBM Maximo Asset Management security bypass
July 14, 2020
Rewterz Threat Alert – M00nD3V Logger
July 14, 2020Severity
High
Analysis Summary
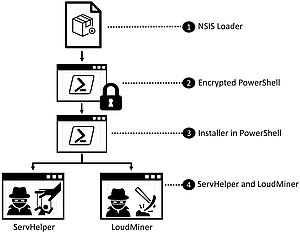
ServHelper that is associated with the hacking group TA505 has been seen targeting financial and retail sectors. With the help of this backdoor, it enabled them to install and deploy other malware like Information Stealers (Predator Stealer), and Remote Access Trojans (RAT) (FlawedAmmy, NetSupport). It is delivered via NSIS installer, which,typically arrives as an attachment to a lure-based email. The loader checks to see if it is running in a virtualized environment to evade analysis techniques. It does this by checking for the presence of a Windows Defender file known to be present in virtualized environments. If this file is present, installation will stop. If the file is not present, the installation proceeds. A PowerShell script contained within the NSIS installer’s directory is then executed. This script decrypts and invokes the main installer of ServHelper. Encryption is done with a combination of Base64 encoding and Triple DES Algorithm. This prevents commands from appearing in plain text. A further set of verification checks are done. The installer checks to ascertain if the instance has administrator privileges. If not, the installer will attempt to escalate privilege using DLL hacking with the assistance of Fubuki from UACME. This readily available collection of tools is typically used by penetration testers for research and privilege escalation. The installer also checks to see if the ROM size is greater than 2MB. If there is no ROM file, the installation stops as this is an indicator of virtualization. Once all components are decrypted, dropped, and installed, the ServHelper DLL is loaded. This specific variant only targets 64-bit Windows Operating Systems. Once the installation is complete, threat actors have backdoor access and are able to send and receive information.
Impact
- Cryptomining
- File encryption
- Information theft
- Exposure of sensitive data
Indicators of Compromise
SHA-256
- C0F5375DD4530C7554212E7C8D85EBE41370BE49E1AA40D381F2E34CBF319134
URL
- hxxp[:]//romashka[.]cn/guga[.]txt
- hxxp[:]//safuuf7774[.]pw/iplog/vmt[.]php?hst=vmt_installed_$env[:]computername
- hxxp[:]//almagel[.]icu/cp[.]exe
- hxxp[:]//almagel[.]icu/ssh[.]zip
- hxxp[:]//asggh554tgahhr[.]pw
- hxxp[:]//nsggh554tgahhr[.]pw
- hxxp[:]//sggh554tgahhr[.]pw
- hxxp[:]//dfsgu747hugr[.]pw
- hxxp[:]//esggh554tgahhr[.]pw
- hxxp[:]//hsggh554tgahhr[.]pw
- hxxp[:]//kuarela[.]xyz/1[.]txt
- hxxps[:]//sgahugu4ijgji[.]xyz/list/b[.]php
- hxxp[:]//asggh554tgahhr[.]pw/list/b[.]php
- hxxp[:]//gabardina[.]xyz/log[.]txt
Remediation
- Block all threat indicators at your respective controls.
- Search for IOCs in your environment.








