Managed Security Monitoring
Monitor. Detect. Investigate. Respond.
With the evolving cyber threat landscape, it is important that organizations not only maintain their security controls but also continue to evolve their ability to detect and respond to threats faster and better. However, building a SOC with the right balance of people and security controls can prove to be challenging.
Rewterz SOC as a Service (SOCaaS) provide you with 24/7/365 security monitoring coupled with our security automation and threat intelligence services tailored for your organization, which helps you prioritize and respond to critical incidents like never before.
A Security Operations Center that is tailor-made for your organization
Based on your organization specific needs and goals, we help you design a security monitoring program that suits your business needs.

Managed Security Services
Security leaders are increasingly outsourcing their security initiatives to managed security services providers to improve level of expertise, demonstrate impact, and reduce the complexity. With managed security, organization's are able to focus on strategic initiatives, as the provider manages the day-to-day operations.
Threats are evolving.
Your SOC should too!
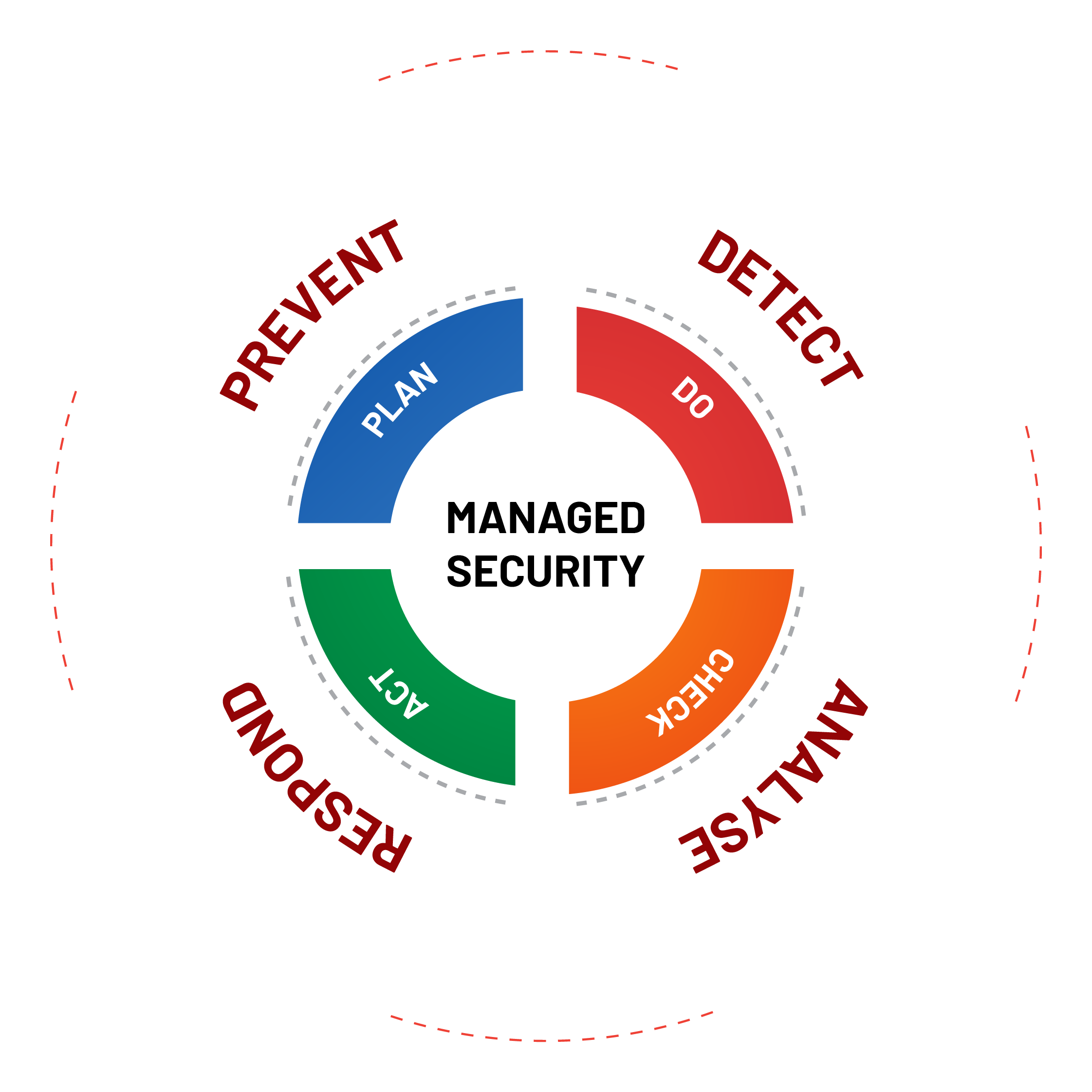
Rewterz acts as your cyber security advisor and helps you continuously evolve your SOC by helping you define better policies and processes to keep up with the changing threat landscape.

Reimagine Your Security Operations
We use cutting edge risk-based SOAR platform SIRP, which helps us manage our SOC operations through a single integrated platform. SIRP enables our teams to track, measure and optimize SOC performance as well as let them automate the repeatable security processes through customized playbooks.

Features
Monitor
Around the clock monitoring which give you real time visibility into what's happening in your infrastructure
Detect
Detect any malicious activities happening in your infrastructure in real time.
Respond
Respond to any malicious activity happening in your infrastructure in real time.
Analyse
Concise and detailed security breach analysis
Contact Rewterz
Speak with our Security Experts and Protect Your Business Now!