

Rewterz Threat Alert – APT27 Emissary Panda Aka LuckyMouse – Active IOCs
November 22, 2022
Rewterz Threat Alert – Orcus RAT – Active IOCs
November 22, 2022
Rewterz Threat Alert – APT27 Emissary Panda Aka LuckyMouse – Active IOCs
November 22, 2022
Rewterz Threat Alert – Orcus RAT – Active IOCs
November 22, 2022Severity
High
Analysis Summary
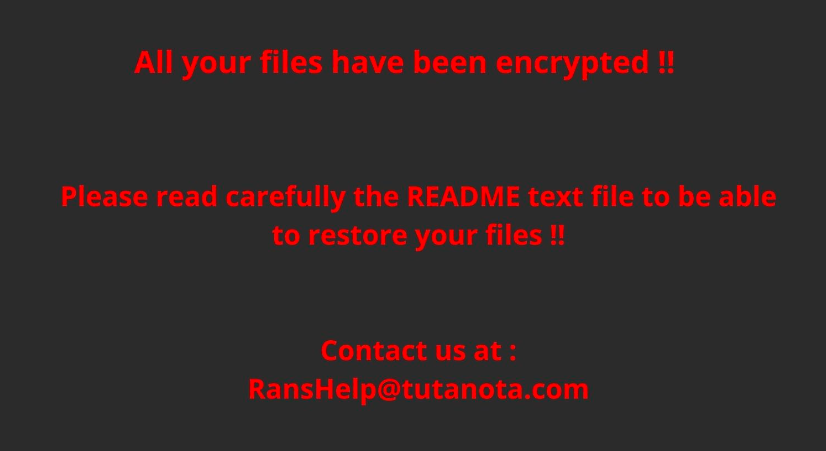
Chaos is a customizable ransomware builder that emerged on June 9 2021 (in underground forums) by falsely marketing itself as the .NET version of Ryuk despite sharing no such overlaps with the notorious counterpart. Since then, it has undergone active development and quick advancements, which have persuaded several attacker groups to adopt it. The most recent version, known as Yashma, was observed in the wild in May 2022. Yashma allows attackers to configure the ransomware so that it does not execute dependent on the language chosen on the victim’s device. It can also disable antivirus software, backup services, storage services, remote desktop services, and credential vault services on victims’ machines. Malware developers frequently employ this strategy to avoid infecting computers in their own region, which would draw the attention of local law authorities. The Chaos ransomware generator is said to still lack some of the capabilities that are seen in many existing ransomware families.
Impact
- File Encryption
Indicators of Compromise
MD5
8aaa59a2dec987b55aa93ea93b9edf5d
f6e9a9c91ab4cb5dcc9e1c6e9aa2e3a5
SHA-256
b2728759d7bf483f7d39f0333a52ae3b74e031ab6be8dc97516384341a80b705
7b1875a61d0f3d097b05c22893250f05a821596181780d2d9ad56bcc9fab5cd1
SHA-1
483fdb4e52358fb89a343ba187f9ec9ea4574459
76831eb24a45cf1b27464879e9fe8806fa856084
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Maintain cyber hygiene by updating your anti-virus software and implementing a patch management lifecycle.
- Maintain Offline Backups – In a ransomware attack, the adversary will often delete or encrypt backups if they have access to them. That’s why it’s important to keep offline (preferably off-site), encrypted backups of data and test them regularly.
- Emails from unknown senders should always be treated with caution.
- Never trust or open ” links and attachments received from unknown sources/senders








