

Rewterz Threat Alert – APT-28 FancyBear – Active IOCs
September 30, 2022
Rewterz Threat Alert – Threat Actors From Brazil’s Prilex Group Resurfaced With Sophisticated Point-of-Sale (PoS) Malware
September 30, 2022
Rewterz Threat Alert – APT-28 FancyBear – Active IOCs
September 30, 2022
Rewterz Threat Alert – Threat Actors From Brazil’s Prilex Group Resurfaced With Sophisticated Point-of-Sale (PoS) Malware
September 30, 2022Severity
High
Analysis Summary
Sidewinder is a suspected Indian threat actor group that has been active since 2012. They have been observed attacking political, military, and corporate organizations throughout Asia, with Pakistan, China, Nepal, and Afghanistan being the most common targets. RAZOR TIGER, Rattlesnake, APT-C-17, and T-APT-04 are the aliases for Sidewinder APT. This APT has been targeting Pakistani government officials with a decoy file related to FOCUSED TALK ON RUSSIAN UKRAINE CONFLICT IMPACT ON PAKISTAN. They employ custom implementations to attack existing vulnerabilities and then deploy a Powershell payload in the final stages to distribute the malware. Sidewinder was also detected employing credential phishing sites that were copied from their victims’ webmail login pages.
In June, 2022, researchers discovered a new malicious infrastructure and a custom tool of the APT group SideWinder (aka Rattlesnake, Hardcore Nationalist, RAZOR TIGER, T-APT-04, and APT-C-17), a threat actor originating from India and particularly targeting Pakistan. SideWinder.AntiBot.Script, a newly found bespoke tool, was utilized in a phishing attack against Pakistani targets.
In July, cyberattacks by Sidewinder APT targeted Pakistani military targets. According to researchers, the Pakistan Air Force Headquarters was the target of the latest Sidewinder strike. While malware file analysis on Virus Total frequently exposes the identification of the attack campaign’s targets, it is unusual to find proof that the attack was successful.
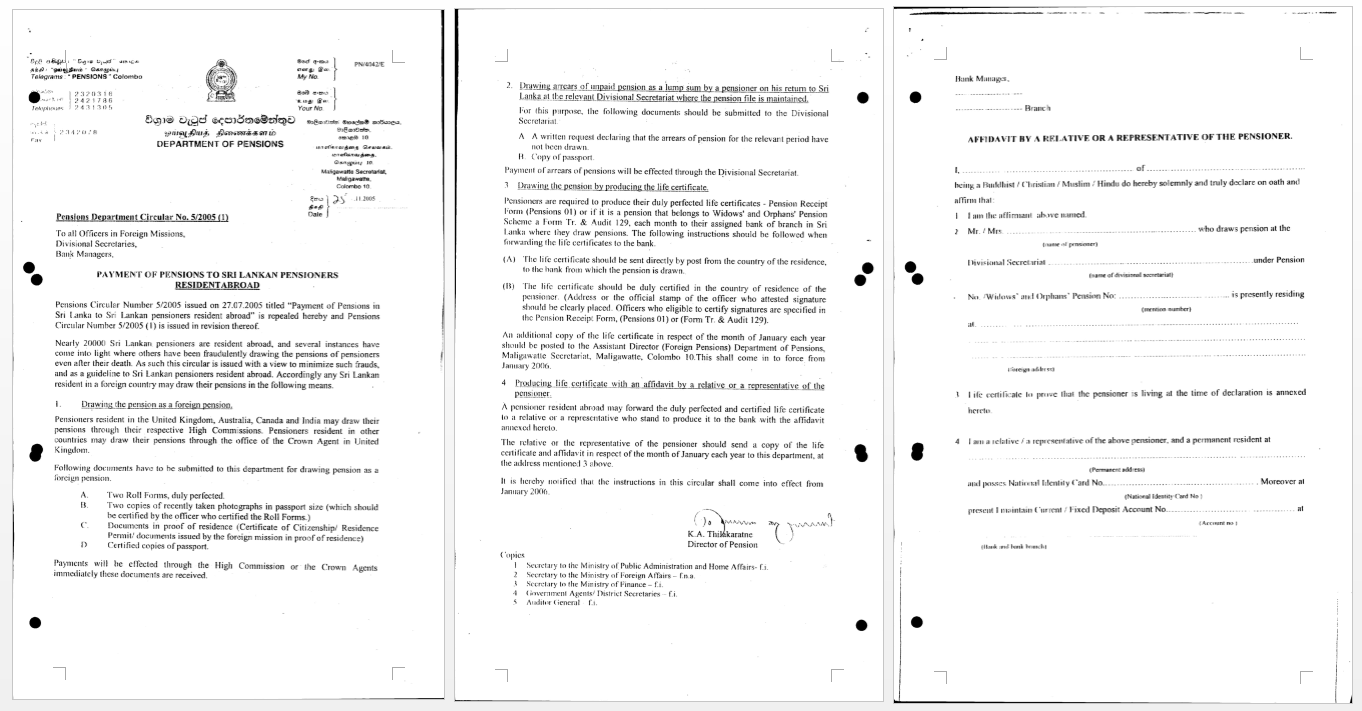
In the mid of September, this group was observed targeting the Pakistani telecom sector with a malicious doc named: Circular 31082022.docx –
Their most recent activity involves the doc named PensionersForm.docx & LIST OF APPROVED MEDICAL PRACTITIONERS.docx
Impact
Information Theft and Espionage
Indicators of Compromise
MD5
- c8e7993906c147b7918e9612c111aeea
- d4886b1da3e30f84562101ce8d1d235d
- 7fbc7c88762b81d9d09fc1a5b1fe3e88
SHA-256
- 37eca58386fbf9c1e381f88776435565623e3d2d1e2b01218f7717b963449735
- 5eec9df0c62b8a0d8c922d366e38ac91907d2a7f5cd13a717d7714015ae362c1
- e6a6066594160a053fe7d68d688b95920936d5880a37a2c91872fb2fc128adf6
SHA1
- 09b5a73e62b803724dd54381f1d98b4b67d64451
- 2220a28ac10b78845535bdc1fdadf35605d1802d
- 1e7f2f5ca24b5f40174c2d950189fca084f8a187
URL
- https[:]//srilanka-navy[.]lforvk[.]com/135/1/334/2/0/0/0/m/files-4fdaf6c7/file[.]rtf
- https[:]//moma[.]comsats-net[.]com/5753/1/4371/2/0/0/0/m/files-b62d382f/file[.]rtf
- https[:]//promotionlist[.]comsats-net[.]com/5756/1/8887/2/0/0/0/m/files-3d1dff0f/file[.]rtf
Remediation
- Block all threat indicators at your respective controls.
- Search for IOCs in your environment.








