Severity
High
Analysis Summary
CVE-2021-4034
A memory corruption vulnerability in a SUID-root Program (polkit’s pkexec) was recently discovered by the Qualys Research Team. It is an easily exploitable vulnerability that allows any unprivileged user to gain full root privileges on a vulnerable host by exploiting this vulnerability in its default configuration. Polkit or PolicyKit controls the system-wide privileges in all Unix-like OS. This component enables organized communication between privileged and non-privileged processes. Successful exploitation of this vulnerability allows any unprivileged user to gain root privileges on the vulnerable host.This is a decade-old flaw that affects all versions of pkexec.
Rewterz also tested the exploit, which gave us root privileges upon running the PoC.
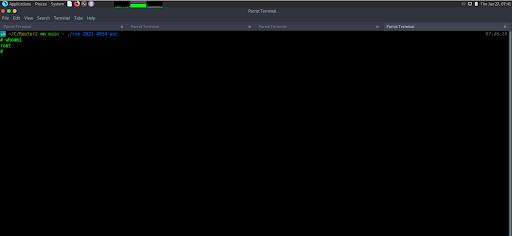
Root Privileges Upon running the cve-2021-4034 PoC
Impact
- Privilege Escalation
Affected Vendors
Linux
Affected Products
- Ubuntu
- Debian
- Fedora
- CentOS
Remediation
Apply patches for this vulnerability from https://blog.qualys.com/vulnerabilities-threat-research/2022/01/25/pwnkit-local-privilege-escalation-vulnerability-discovered-in-polkits-pkexec-cve-2021-4034

