

Rewterz Threat Alert – Pxj Ransomware – IoCs
March 2, 2020
Rewterz Threat Alert – Hidden Cobra Latest Activity
March 2, 2020
Rewterz Threat Alert – Pxj Ransomware – IoCs
March 2, 2020
Rewterz Threat Alert – Hidden Cobra Latest Activity
March 2, 2020Severity
High
Analysis Summary
A couple dozen documents have been found in the past few weeks, that execute the OSTAP javascript downloader. The documents make use of the latest version of the remote desktop activeX control class that was introduced for Windows 10. The attackers utilize the activeX control for automatic execution of the malicious Macro following an enable of the Document content. While tracing this group abusing the remote activeX control, other groups were found misusing the same and earlier controls although with a slightly different technique, as each document usually contained an image to convince targets to enable the content. This leads to the execution of the malicious macro, only this time the image also hid an ActiveX control slightly below it. The malicious OSTAP JavaScript downloader is then hidden in white colored letters in between the content, so it’s not visible to people but can be seen by machines.
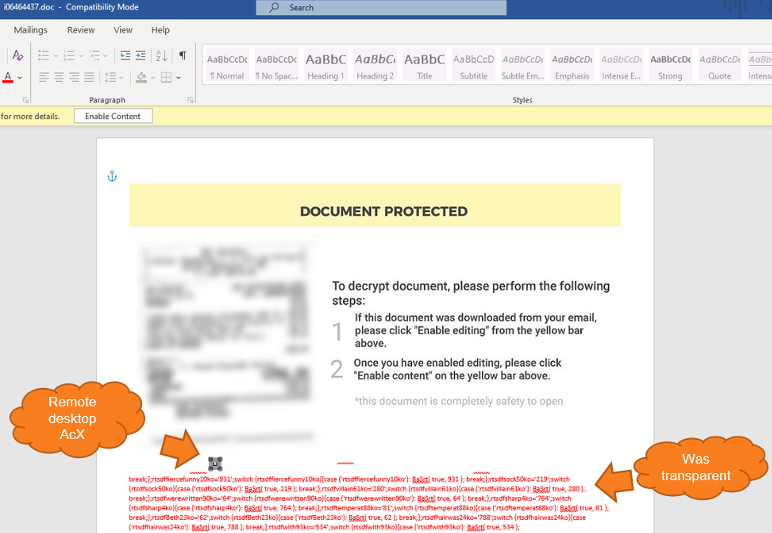
Examining the activeX control revealed the use of the MsRdpClient10NotSafeForScripting class (which is used for remote control). The Server field is empty in the script, which will later cause an error that the attackers will actually abuse to properly execute their own code.
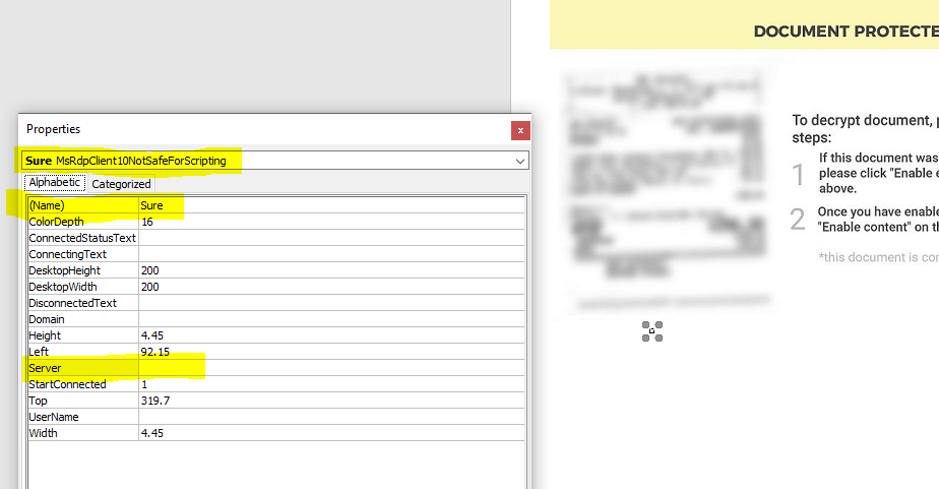
There are hundreds more objects that have been introduced in the latest Windows 10 and even dozens more methods in the described object that sophisticated attackers can abuse.
Impact
- ActiveX Abuse
- Unauthorized Remote Access
- Credential Theft
- Security Bypass
Indicators of Compromise
Hostname
insiderppe[.]cloudapp[.]net
MD5
- 8fbf3c9d1db33d33030373068ac71edd
- 5394e0699b97dd28b30f610363425afa
- c79a7bb456de1b604e88eea335756e60
- 7302609a2c9dd6d0c8b90a2cc4736928
- a6b00c8d9204cbf3c547d72e86722bdc
- bb35d1bd6612311fb658ef81fe41e6b8
- dfcdb189eafa87b66861d3d110e17f7a
- 933ecdba3b8587ef95d03d3960b2467d
- d193e97633d60bd452b6d96ae1200b72
- ebff5a6f95eddd1adba23636e710f6f7
- 56fb46a98dfd89e39aa0807ec509ebbe
- b7ab8626aaf0365d373a180bde43ccab
- e8a226de309963891c7b7b141ef73418
SHA-256
- 200a0cc130113fedd2e3baa0e5988ca18102a652909b2530785242fd800dd4f5
- 6226065b170ad402b35ff8307eab843f46b54cc7a93a3717af0fa9cf2eb433df
- 005a1e42bb3e5092124dfa40b9a765339c7ab9ea00c276ba2f2af32ce2ed81ce
- 891c716d059459d97a726a9bb262bc20f369b6c810097ff312fd710a4d4da577
- 74422ee3e1274bad11f5ac44712b1d10fce3a1e7fd9acc0a82fe88d9e9b7b78e
- 683a9df3e291669e6a1ee35aa08222e228bd553f76ba049c4b8873f6d9eb8880
- 3d0c3f3d464a8229480b6d4a024d2982c72d67942d8ee245dd91da1a26ddd22a
- bb7a43ea1a305228e6ff36abef475e046e549e309fddf334d97707bfbc47aef4
- 8b975bcdc73d28d299b60b7c1ab81c0a5b3a30153725dc41e836659a4ea78831
- ff7334237ad5a76d682c32267ffbada9ef091eb87f3683981b71e1d84c3990a9
- c1374ddd0b06eb942a7d5224ebf3c6a10802902dd8eee03fe9603292714f8bf1
- 0d25947452fbd14301f660f357845760693eabf61e99bd55c7ab47a44a88ccd5
- 414744acddc03bb095a31708c66f33ae456af58ae85ab2887e9781b528034064
Remediation
- Block the threat indicators at their respective controls.
- Strictly avoid downloading untrusted documents from any source.








