

Rewterz Threat Alert – Malspam NanoCore RAT Malware – Indicators of Compromise
June 24, 2019
Rewterz Threat Advisory – Critical RCE affects older Diebold Nixdorf ATMs
June 25, 2019
Rewterz Threat Alert – Malspam NanoCore RAT Malware – Indicators of Compromise
June 24, 2019
Rewterz Threat Advisory – Critical RCE affects older Diebold Nixdorf ATMs
June 25, 2019Severity
Medium
Analysis Summary
ServHelper is a new malware family — best classified as a backdoor first observed in the wild in November 2018. Its name is based on a filename (ServHelper.dll).
There are two distinct variants of ServHelper: a “tunnel” variant and a “downloader” variant. The “tunnel” variant has more features and focuses on setting up reverse SSH tunnels to allow the threat actor to access the infected host via Remote Desktop Protocol (RDP). Once ServHelper establishes remote desktop access, the malware contains functionality for the threat actor to “hijack” legitimate user accounts or their web browser profiles and use them as they see fit. The “downloader” variant is stripped of the tunneling and hijacking functionality and is used as a basic downloader.
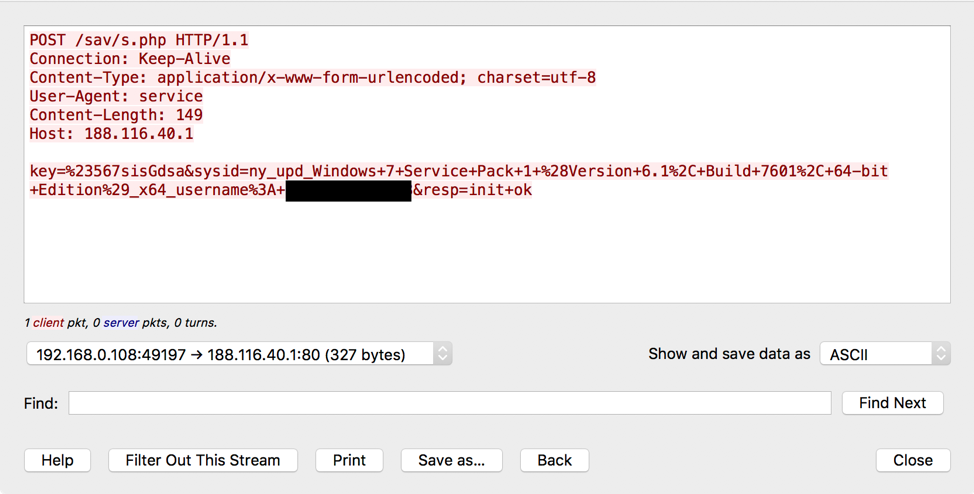
Both variants of ServHelper use the same HTTP C&C protocol on port 443 (HTTPS) and, less frequently, port 80 (HTTP). An example of the initial phone home to the C&C server.
Impact
Exposure of sensitive information
Indicators of Compromise
URLs
- hxxp[:]//bascif[.]com/tt1
- hxxp[:]//shortag[.]icu/docs/s[.]php
Email Address
- officeus[@]imobileinfo[.]org
- esecs192[@]earthlink[.]net
- emails[@]executive-officemail-portal[.]net
- personal[@]c-level-office-expense-suite[.]net
- huppdyke[@]stny.rr[.]com
- thaiqt08[@]gmail[.]com
- ceooffice778[@]cox[.]net
- cvs[@]onlineupdatee[.]com
- lpad[@]covatt[.]net
- ceo_backupmail[@]lycos[.]com
- do4128574[@]gmail[.]com
- cmd2[@]wincmd[.]net
- sinaceo321[@]naver[.]com
- win[@]mavett[.]net
- private1[@]myprioffices[.]com
- cmg[@]movap[.]net
- jkrjr[@]cox[.]net
- carr_je[@]inleeo[.]com
- p.resid.nt019[@]gmail[.]com
- admin[@]fveg[.]net
- mds[@]movap[.]net
- 0000986456788132[@]myipad-app[.]com
- tosinbanjo54[@]gmail[.]com
- butterworthamy3030[@]gmail[.]com
- iexnc[@]carolina.rr[.]com
- kaarenyth[@]neo.rr[.]com
- andw[@]bwttmn[.]com
- rherman[@]woh.rr[.]com
- mdbyrne5[@]gtsce[.]net
- idxc[@]neo.rr[.]com
- isdrx[@]nycap.rr[.]com
- manuel.db[@]nextstep[.]mx
Malware Hash (MD5/SHA1/SH256)
- 05a092bd622b566c09a21410de66cc0d03996f92
- e3724a970d0b5b45c014390694ec8a583f0c8504
- 05589e5ba447789dec4b77e68ca54737586073ed
- 0b54affdae59d77fbb3d88a3316faf9b1a2a49de9723e75df2fa09c2354a6f6e
- e76b69418c1abf66207316cac4ba4858
- 4a05aa6a5667598f93a5a5089bf110f52a0f7c6fc510db2bbcccccf789565090
- 98dd2b2ab44502731941bfb3b33316f0
- ceb68a619dd39cca9537cfe4d426dd36cf20b698
- ac27ad89f4631944761d1a3cf0cd47a4
- bf75d3f9476e31cc37eccd22cd069149b5a15489
- 28d46e41b92ad8b9ad6588904e0a556b9f04d3d6
- f855043ba5aac868dcfb7c5fcb484de201de111b50767059c8f9c766d187d067
- a157c3e084364723e590c07ba9b2d5b5
- bef95198b4091328e21b5f7e1d36b5a7b5f489e1
- be040f7f933a530e729ed77323157f96b50350953ba2642e6a99d3ead043e9a7
- 6d66397ff0a87aaab2accaebfe008a44
- 3503cd7f7265c468b12403df77da4fed65c53879
- 74b9517eef8c87cea0923f9eb5bf334b022e2125b985e42ef34de710ecb06846
- 3f3fbdd54a4de179a00e6828c70c4ac5
- 360ea97e95a6690a8344ff7775d66cd82880c523
- 83fa77f61ee57a5dd037d9994b5d991543860d9f56e962f4e41319132fb70a09
- 275d1dd0b0cbeb3fdd713d95d3b62468
- d929c8cce0c5b43f7feeed679f30516c8f8c8472
- b6025360afba9ebbb3d4c5ff30223309550d4fa68056fc8251b0e9a486ff2125
- 205102aae7b504e92b5af5a4ff821a8f
- 1d53c33ef841f142bc16fc21895e002e9bac6836
- 7f9076610442d01461af314e158d592415c0adf60b0d22016ca64d35f1756d5a
- 67be33210235d2419dbef71e769ad1e5
- ade64bcb51b89e2662efecbfa589d14a1157a317a62ce2aa98e393e8f2610a4e
- 091c46b7168f2f18368f120ae2e31197
- bd84a8bd2e1380b917baae55124766c5d4c1fd5e
- 1f2be0267a715b6537e14dc8150b32e5cd48bd2642889f89912ec3d1a4bfe1ea
- 5f972e9640095bbf27ffcf4ef3bd2b54
- 42d5d442d1cee8d224fba15cf7ecbffedaadfb51
- 412a76221b95352ff08b86f569ed99599a7cd6ebacc24ccbdd770a7b24b121c7
- 17d11b9e324faf3b1a53d8fdb002508fc0b6236472d762822d9b550c690b2623
- 5ff1fb5a71605746af7679bdee63d531341f8699b45db6155d784bae8e520d75
- 18485e39f50aecbc7efc5d3ce10f30fe
- 743caed376fee068b23233a8bcc5b910d4078f51
- 9346bc43fff2eff3ecf15c9d63bce47f4d011a5abbdef76863a5a0de4513afdd
- 05e8cd144e276fb6c7f91fb3b56a7747
- de69cbe279c63e06dfef878b8581723a372d81e1
- c05f5f4559ce43fbcefdcbf76c7a9e71db4db97afe45786b5c7e924aa130fcfb
- d89b0bea527d846bcb94b2cc2003bb53
- af978782e026e18399beaea0ad168c4404724f98
- 2662581b71ba12d265592beb66ed7f681cf84c93132e37eb32b63cbe14aaf7c4
- 7b54477d926ce5b0b0e6aba4f3b5ca4c
- 8bbc2cbcdd4bc484a21949874818c4fa3ce689cc
- ff6f9f3006945512678c8f8148345ea75468cbb5a2e7f82f470db3d2382f9007
- b67d94ef23ad11b8b77491b6695bfe36
- 9fc75cbd459f570168f512fdf11a57ea24c08d9f
- 5c361bab21f7db6a58f23c6db38d88b35943544687bd8c643031add429ed135d
- d3e480399071fd7050eb010e42585472
- 5050037c5a09cb964becb9003866caf023e91bfc
- 20f5739547252061a9d5f054b5f5e1061afb5cdbfba84ebd0edf840acadcbe43
- 7adcd1d371242f178820ae391eca584b
- e6dcf74839e42bad56acc25590837e54af28d101
- 6b6f208a153bb9d8d7bf8611ccedd8253aadf954659eaca3fb828dd3b05de030
- fd74a2ee6ca88139b1108f42cbb4c464
- 6858a2767f7a20661fd7e30fe19b6239b4f6c8f1
- f3749d2e368ee50ea41a91e07b5c487cf2f699aa2901421a430b6d00c5a210ba
- f3fa8f85ae78b2fa14957890f54beb8a
- 62d723da6a90a7e6cc58358631c45c5a4cc4e470
- da924ab92888144f769b39b509d5984ae654f06a041215be1c7c1ef7b6e083d3
- ec6aacb606f1e29d38efe34d345accda
- 181d7a5478d5a0174b416fea4fc195e5e02a1f0a
- 9a1cde5e4e066932debff522b48144ddcf9507955b618cd99815853a230a0ebe
- 4392e4cd4022d21fc56d4b24a2618573
- 54d1384928432b38411d470d9eb1d83d5cf6bbdc
- 515d14fb14dae31a24cbfa4c8c3b6f5694753c57aed90e8714b975fd161b925a
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on the link/ attachments sent by unknown senders.








