

Rewterz Threat Alert – GoMiner Mutates and Spreads via Public Cloud Storage Providers
January 27, 2020
Rewterz Threat Advisory – CVE-2019-16018 – Cisco IOS XR Software BGP EVPN Operational Routes Denial of Service Vulnerability
January 27, 2020
Rewterz Threat Alert – GoMiner Mutates and Spreads via Public Cloud Storage Providers
January 27, 2020
Rewterz Threat Advisory – CVE-2019-16018 – Cisco IOS XR Software BGP EVPN Operational Routes Denial of Service Vulnerability
January 27, 2020Severity
High
Analysis Summary
FireEye has tracked extensive global exploitation of CVE-2019-19781, which continues to impact Citrix ADC and Gateway instances that are unpatched or do not have mitigations applied. Previously reported on attackers’ swift attempts to exploit this vulnerability and the post-compromise deployment of the previously unseen NOTROBIN malware family by one threat actor. FireEye continues to actively track multiple clusters of activity associated with exploitation of this vulnerability, primarily based on how attackers interact with vulnerable Citrix ADC and Gateway instances after identification. Recent compromises suggest that this vulnerability is also being exploited to deploy ransomware. If your organization is attempting to assess whether there is evidence of compromise related to exploitation of CVE-2019-19781.
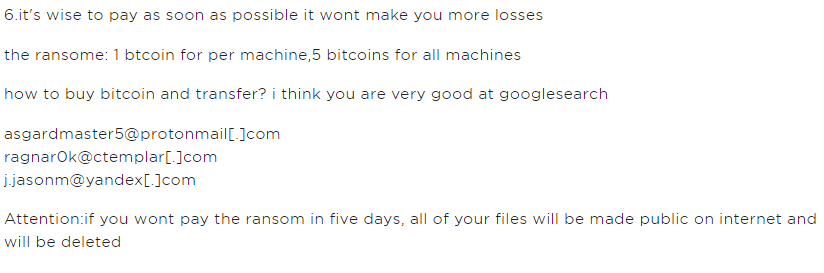
Further analysis and sandboxing of this binary brought all the pieces together—this threat actor may have been attempting to deploy ransomware aptly named ‘Ragnarok’

Impact
File encryption
Indicators of Compromise
- asgardmaster5@protonmail[.]com
- j[.]jasonm@yandex[.]com
- ragnar0k@ctemplar[.]com
MD5
- b0acb27273563a5a2a5f71165606808c
- 9aa67d856e584b4eefc4791d2634476a
- 01af5ad23a282d0fd40597c1024307ca
- 6cf1857e569432fcfc8e506c8b0db635
- e345c861058a18510e7c4bb616e3fd9f
- 0caf9be8fd7ba5b605b7a7b315ef17a0
- 55b40e0068429fbbb16f2113d6842ed2
- 48452dd2506831d0b340e45b08799623
- 9e408d947ceba27259e2a9a5c71a75a8
- bd977d9d2b68dd9b12a3878edd192319
Remediation
Block all threat indicators at your respective controls.
Apply upgraded patches.








