

Rewterz Threat Advisory – Cisco Data Center Network Manager Multiple Vulnerabilities
January 6, 2020
Rewterz Threat Alert – Malicious Google Play Apps Exploit CVE-2019-2215 in Androids
January 7, 2020
Rewterz Threat Advisory – Cisco Data Center Network Manager Multiple Vulnerabilities
January 6, 2020
Rewterz Threat Alert – Malicious Google Play Apps Exploit CVE-2019-2215 in Androids
January 7, 2020Severity
High
Analysis Summary
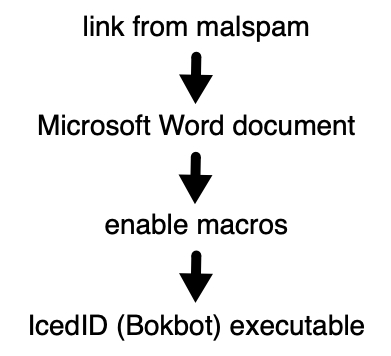
A new campaign has been distributing the IcedID banking trojan since the past week. Usually, IcedId is spread via malspam that pushes different Word docs from links which contain IcedID. The malware is executed when a user enables content or macros for these files. Below is the usual infection flow for IcedID.
If the email recipient opened the document and enabled macros, the end result would be the installation of the IcedID Trojan. Persistence is achieved using a scheduled task. IcedID will inject implants into web browsers in order to steal financial information. It also steals other information such as credentials from various applications and cookies. IcedID can also, on instructions from its C&C server, install additional malware.
Impact
- Credential Theft
- Financial Loss
Indicators of Compromise
Domain name
- bezzuhikali[.]info
- turbodieselmegane[.]info
- successkali[.]red
- kasialinia[.]info
MD5
- 7aa14ec70d17b2f7e3e312610ee79877
- 8d32be8ba719b604464fd16761b55aab
SHA-256
- 77c4de837e57a955cb3c9f584d6667ab588589b6b662b48d3ec9473c21d30216
- 837c42a394c73018179937bbafa6510054839d574ffd37046157f65641d8f1f7
Source IP
- 188[.]127[.]227[.]76
- 79[.]174[.]13[.]19
- 185[.]87[.]187[.]198
- 109[.]248[.]222[.]22
- 89[.]105[.]194[.]151
URL
- hxxp://bezzuhikali[.]info/
- hxxps://bezzuhikali[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTAmcT0xJnU9MTUyMS
- ZyPTEyMTAxMzg5NyZzPTIyOTkwODI2MDAmdD0xOTY2ODAyMTA3
- hxxps://bezzuhikali[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTAmcT0xJnU9MTgyMS
- ZyPTEyMTAxMzg5NyZzPTIyOTkwODI2MDAmdD0xOTY2ODAyMTA3
- hxxps://bezzuhikali[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTQmZj0yJmc9MQ==
- hxxp://successkali[.]red/
- hxxps://successkali[.]red/photo[.]png?id=0124FE8030BD6865020000000000FF40000001
- hxxp://kasialinia[.]info
- hxxps://kasialinia[.]info/photo[.]png?id=0124FE8030BD6865020000000000FF40000001
- hxxp://turbodieselmegane[.]info
- hxxp://turbodieselmegane[.]info/
- hxxp://turbodieselmegane[.]info/data3[.]php?6831558324FE8030
- hxxp://turbodieselmegane[.]info/data3[.]php?7D8AAD5B24FE8030
- hxxps://turbodieselmegane[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTE2
- hxxps://turbodieselmegane[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTE3
- hxxps://turbodieselmegane[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTE4
- hxxps://turbodieselmegane[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTEmaj01MjU0MDA0QUFEMjEmbT0lNTUlMDAlNTMlMDAlNDUlMDAlNTIlMDAlMkQlMDAlNTAlMDAlNDMlMDAmcD0lNTclMDAlNEYlMDAlNTIlMDAlNEIlMDAlNDclMDAlNTIlMDAlNEYlMDAlNTUlMDAlNTAlMDAmaz0zJm49Mjg5Jm89Ni4xLjc2MDEuMS42NC4xJmw9JTYxJTAwJTY0JTAwJTZEJTAwJTY5JTAwJTZFJTAwJnc9ODE5MiZxPTEmdT0xMjIw
- hxxps://turbodieselmegane[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTQmZj0xJmc9
- MQ==
- hxxps://turbodieselmegane[.]info/sqlite64[.]dll
- hxxps://bezzuhikali[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTgmZj0wJmc9MQ==
- hxxps://bezzuhikali[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTQmZj0zJmc9MQ==
- hxxps://bezzuhikali[.]info/index[.]php?z=JmE9NjIwNjU4NzM2JmI9MjEwNjI0MDM0NyZjPTEyJmQ9MCZlPTgmZj0x
Remediation
- Block the threat indicators at their respective controls.
- Do not download files/click on URLs found in untrusted emails.








