

Rewterz Threat Advisory – Critical WordPress Bug
January 16, 2020
Rewterz Threat Advisory – CVE-2019-1889 – Cisco Application Policy Infrastructure Controller REST API
January 17, 2020
Rewterz Threat Advisory – Critical WordPress Bug
January 16, 2020
Rewterz Threat Advisory – CVE-2019-1889 – Cisco Application Policy Infrastructure Controller REST API
January 17, 2020Severity
High
Analysis Summary
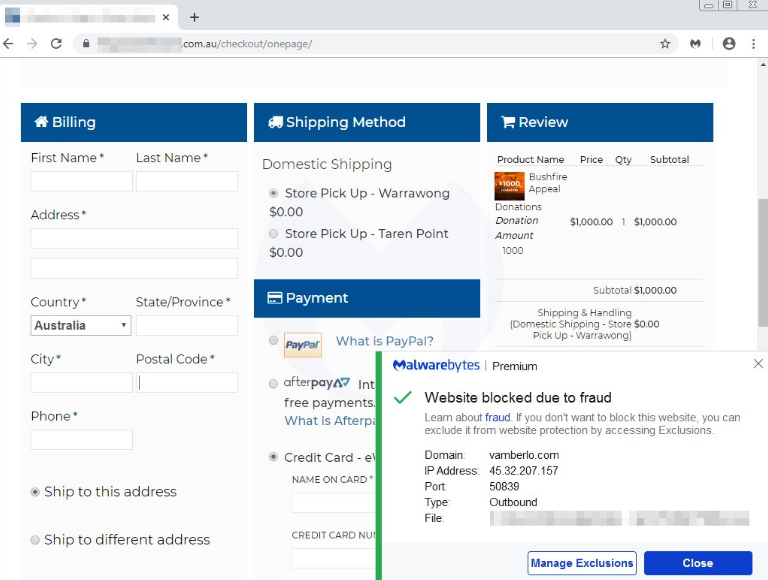
Attackers have compromised a website collecting donations for the victims of the Australia bushfires and injected a malicious script that steals the payment information of the donors. This type of attack is called Magecart and involves hackers compromising a web site and injecting malicious JavaScript into eCommerce or checkout pages. These scripts will then steal any credit cards or payment information that is submitted and send it off to a remote site under the attacker’s control.
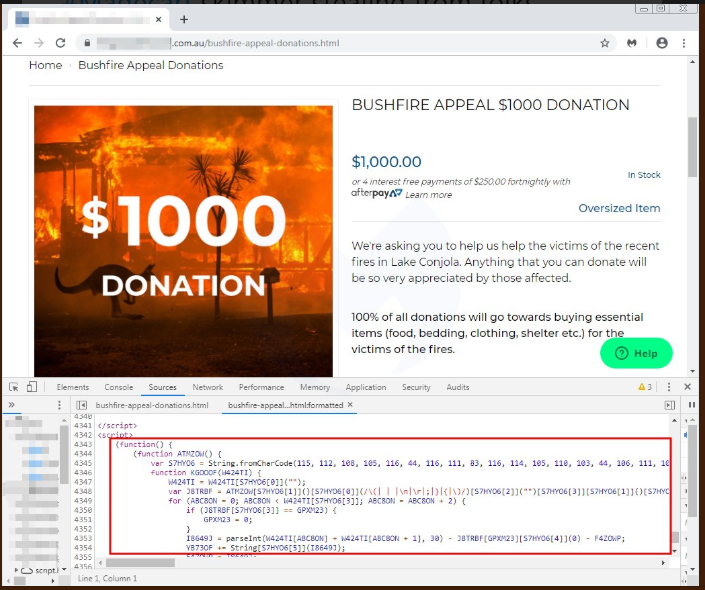
Magecart attacks often take advantage of vulnerabilities within the code of third-party scripts.
Impact
- Theft of financial information
- Financial loss
Indicators of Compromise
Domain Name
- vamberlo[.]com
- www[.]lojabondinho[.]com[.]br
- jessieboutique[.]com
- buenaprensa[.]com
- thebuzzexperience[.]com
Source IP
45[.]32[.]207[.]157
URL
- https[:]//jessieboutique[.]com/
- https[:]//www[.]gncsuplementos[.]com[.]br/
- https[:]//thebuzzexperience[.]com/
- https[:]//buenaprensa[.]com/
Remediation
- Block the threat indicators at their respective controls.
- Make sure all apps and software are patched against vulnerabilities.








