

Rewterz Threat Alert – The Latest Attacks by Kimsuky APT Use AppleSeed, MeterPreter, and TinyNuke – Active IOCs
January 2, 2024
Rewterz Threat Alert – Tofsee Malware – Active IOCs
January 3, 2024
Rewterz Threat Alert – The Latest Attacks by Kimsuky APT Use AppleSeed, MeterPreter, and TinyNuke – Active IOCs
January 2, 2024
Rewterz Threat Alert – Tofsee Malware – Active IOCs
January 3, 2024Severity
High
Analysis Summary
An exploit was revealed in October 2023 that can generate persistent Google cookies by manipulating tokens. A threat actor can use the exploit to gain access to Google services even if the user has reset their password. Reverse engineering performed by security researchers uncovered that the exploit relies on an undocumented Google OAuth endpoint called “MultiLogin”.
The MultiLogin endpoint is a mechanism that allows Google accounts across services to be synchronized. It receives a vector that contains account IDs and auth-login tokens that are used to handle concurrent sessions or smoothly transition between user profiles.
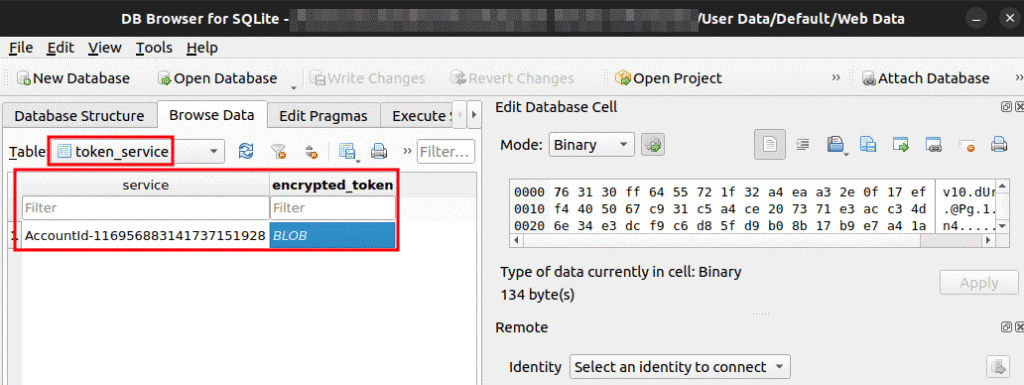
The notorious Lumma Infostealer malware was seen utilizing the exploit on November 14. Some other malware like Risepro, Rhadamanthys, Meduza, White Snake, and Stealc Stealer have also leveraged the exploit. The malware targets the token_service table of WebData in Chrome browsers to harvest token and account IDs of Chrome profiles that are logged in.
The researchers stated, “The insights from the Chromium codebase confirm that while the MultiLogin feature plays a vital role in user authentication, it also presents an exploitable avenue if mishandled, as evidenced by recent malware developments.”
The table has two columns that are GAIA ID and encrypted_token. The tokens are decrypted using an encryption key that is stored in the UserData directory in Chrome’s Local State. The Lumma malware constantly regenerates cookies for Google services by manipulating the token:GAIA ID pair. The exploit works even after the users have reset their passwords, allowing the threats to achieve persistence that allows potentially unnoticed exploitation of user accounts and data.
Analysis of the user-agent string that was found in the source code shows that a penetration test on Google Drive’s services for Apple devices could be a potential origin for the exploit. The source code was revealed due to imperfect testing of the exploit. So far, Google has not confirmed whether threat actors are leveraging the zero-day exploit in the MultiLogin endpoint.
Impact
- Unauthorized Access
- Sensitive Information Theft
Remediation
- Upgrade to the latest version of Google Chrome, available from the Google Chrome Releases Website.
- Always be suspicious about emails sent by unknown senders.
- Never click on links/attachments sent by unknown senders.
- Ensure that general security policies are employed including: implementing strong passwords, correct configurations, and proper administration security policies
- Enable multifactor authentication (MFA).
- Enable conditional access policies to block attacks that use stolen credentials.
- Enable antivirus and anti-malware software and update signature definitions promptly. Using multi-layered protection is necessary to secure vulnerable assets.








