

Rewterz Threat Alert – APT MustangPanda – Active IOCs
November 23, 2022
Rewterz Threat Advisory – CVE-2022-40746 – IBM i Vulnerability
November 23, 2022
Rewterz Threat Alert – APT MustangPanda – Active IOCs
November 23, 2022
Rewterz Threat Advisory – CVE-2022-40746 – IBM i Vulnerability
November 23, 2022Severity
High
Analysis Summary
Email-based phishing campaign targeting individuals in the Middle East spiked by 100 percent in October in the lead-up to the World Cup in Qatar.
These phishing attempts increased between September and October, when the number of malicious emails doubled, according to researchers.
The initial attack vector exploited by threat actors was FIFA and other football-related lures. The campaigns use customized web sites that appear to be legitimate, and the attacks incorporate a variety of malware.
Financial fraud, credential harvesting, data exfiltration, surveillance, and reputation damage are among the objectives of these cyberattacks.
Researchers gave a variety of samples of emails observed in the wild. In one case, the email appeared to be from the FIFA transfer matching system (TMS) helpdesk and contained a fake notification that the user’s two-factor authentication had been disabled. It then sent the user to an attacker-controlled website, where the hackers stole the user’s credentials.
In another example, one email impersonates David Firisua, Auckland City FC’s squad manager, and requests confirmation of a payment paid to FIFA. Many of the emails contain hyperlinks that direct recipients to fake brand websites or phishing sites. Some of the emails pose as legal notifications involving overdue FIFA fees.
“It is a common practice for attackers to utilize the important/popular events as a part of the social engineering tactics and particularly target the organizations which are related to events and more promising victims for the attack,” they added.
Threat actors utilize highlighted World Cup-themed phishing pages that imitate the real FIFA pages they spoof. They deploy various phishing kits where the post URL is either obfuscated, Base64 encoded or contained in the ajax request instead of form action tags.
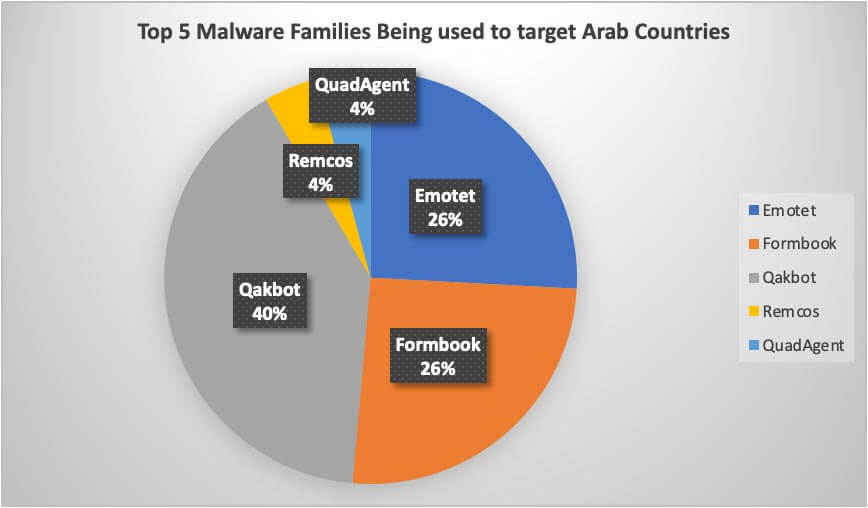
Qakbot, Emotet, Formbook, Remcos, and QuadAgent are the top five malware families that were seen targeting Middle Eastern countries.
These phishing attacks are expected to continue until January 2023. Organizations closely associated with the event are recommended to be extra vigilant since they are the most likely targets for such attacks.
Impact
- Credential Harvesting
- Data Exfiltration
- Financial Fraud
Indicators of Compromise
URL
- https://achar724.com/stt/index.php?tu-blaroe=2
- https://ac.net.pe/rmu/index.php?qiu-stlvauop=6
- https://abuhureira.sc.ke/roo/index.php?nude-ivtae=5
- https://a1revenue.com/ut/index.php?otid-urosmnt=3
Remediation
- Emails from unknown senders should always be treated with caution.
- Never trust or open ” links and attachments received from unknown sources/senders.
- Block all threat indicators at your respective controls.
- Search for Indicator of compromise (IOCs) in your environment utilizing your respective security controls
- Be wary of any solicitations for your personal information or money.
- install antivirus software on your devices
- Change your passwords frequently
- Do not download documents attached in emails from unknown sources and strictly refrain from enabling macros when the source isn’t reliable.
- Enforced Access Management Policies
- Do not use the same password for multiple platforms, servers, or networks.








