

Rewterz Threat Alert – Vidar Malware – Active IOCs
July 10, 2023
Rewterz Threat Alert – A New SolarMarker Infostealer – Active IOCs
July 10, 2023
Rewterz Threat Alert – Vidar Malware – Active IOCs
July 10, 2023
Rewterz Threat Alert – A New SolarMarker Infostealer – Active IOCs
July 10, 2023Severity
High
Analysis Summary
TA453, a nation-state threat actor also known as Charming Kitten, PHOSPHORUS, and APT42, has been identified in a recent malware campaign targeting both Windows and macOS systems. This campaign marks a shift in TA453’s tactics as they have started using LNK infection chains instead of Microsoft Word documents with macros. The initial attack vector involves spear-phishing emails that pose as benign conversations, impersonating a senior fellow from the Royal United Services Institute (RUSI) to a public media contact at a US-based think tank focused on foreign affairs.
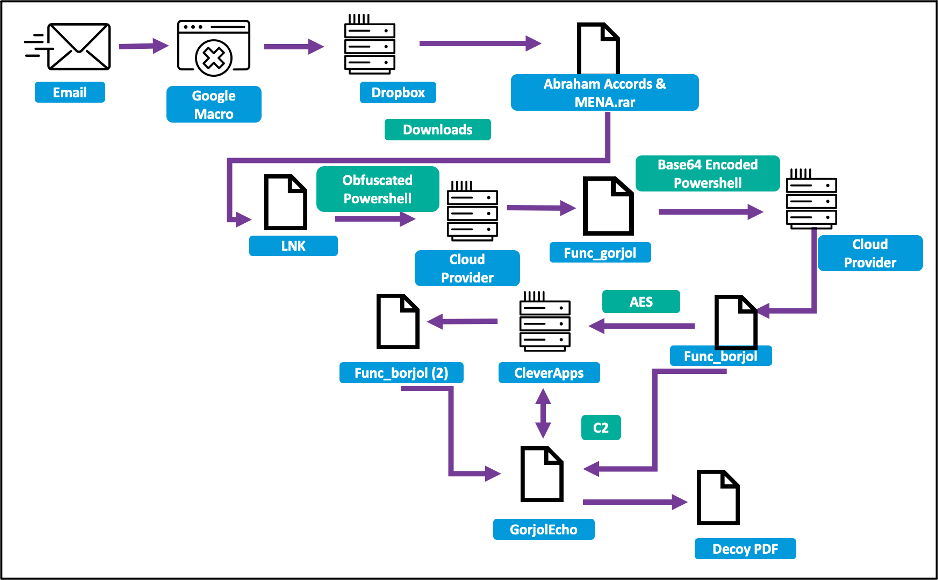
Upon engagement with the emails, TA453 sends a malicious link leading to a Google Script macro, redirecting the victim to a Dropbox URL. At the provided URL, a password-encrypted .rar file named “Abraham Accords & MENA.rar” is hosted, containing a dropper named “Abraham Accords & MENA.pdf.lnk.” This departure from TA453’s usual infection chain involving VBA macros or remote template injection is noteworthy. When the LNK file is opened, PowerShell downloads additional stages from a cloud hosting provider.
The final-stage malware employed by TA453 is the GorjolEcho backdoor, which disguises itself by displaying a decoy PDF document while awaiting instructions from the command and control (C2) server. To maintain persistence, GorjolEcho copies the initial stages malware into a StartUp entry.
For macOS systems, TA453 employs a different approach. They send a second email containing a ZIP archive with a Mach-O binary masquerading as a VPN application. This binary, an AppleScript, connects to the C2 server and downloads a Bash script-based backdoor called NokNok. NokNok establishes a backdoor on the system and achieves persistence using LaunchAgents. It is believed that NokNok is a port or evolution of GorjolEcho and serves as an initial foothold for TA453’s intrusions.
The researchers suspect that TA453 has additional espionage-focused modules for both GorjolEcho and NokNok. The observed similarities in code and functionality between NokNok and other malware associated with Charming Kitten indicate a connection. These findings align with previous reports from Google’s Threat Analysis group, which also highlighted overlaps in code and techniques. The presence of NokNok modules resembling Charming Kitten’s Mac malware from early 2017 further strengthens this connection.
Impact
- Information Theft
- Intelligence Gathering
- Disruption Of Critical Infrastructure
Indicators of Compromise
Domain Name
- library-store.camdvr.org
- filemanager.theworkpc.com
- fuschia-rhinestone.cleverapps.io
IP
- 144.217.129.176
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Implement strong access controls: This includes using multi-factor authentication, strong passwords, and limiting access to sensitive systems and data.
- Regularly patch and update systems: Keeping systems up-to-date with the latest security patches and configurations is essential to prevent known vulnerabilities from being exploited.
- Monitor network activity: This includes using intrusion detection and prevention systems to detect and respond to potential attacks.
- Conduct regular vulnerability assessments: This can help identify and remediate weaknesses in network defenses before they can be exploited by attackers.
- Implement network segmentation: Limiting access to critical systems through network segmentation can help prevent lateral movement by attackers in the event that they gain access to the network.
- Prioritize employee training and awareness: This can help prevent social engineering attacks, such as phishing, which are commonly used by nation-state threat actors to gain access to sensitive systems and data.
- Have an incident response plan in place: This should include regular testing and updating of the plan to ensure that it remains effective in the face of evolving threats.








