

Rewterz Threat Alert – Phobos Ransomware – Active IOCs
September 12, 2023
Rewterz Threat Update – Mirai Variant Using Android TV Boxes for DDoS Attacks
September 12, 2023
Rewterz Threat Alert – Phobos Ransomware – Active IOCs
September 12, 2023
Rewterz Threat Update – Mirai Variant Using Android TV Boxes for DDoS Attacks
September 12, 2023Severity
High
Analysis Summary
A recent phishing attack, known as the “MrTonyScam,” is utilizing Facebook Messenger to spread malicious messages containing attachments from a multitude of fake and hijacked personal accounts. The main objective of this attack is to gain control of the victims’ Business accounts. The campaign is associated with a Vietnamese-based group and employs a compressed file attachment that contains a Python-based stealer using various obfuscation techniques.
The attack begins by sending potential victims enticing messages with RAR and ZIP archive attachments. Clicking on these attachments triggers the deployment of a dropper that fetches the next stage from either a GitHub or GitLab repository. This next stage includes an archive file containing a CMD file, which, in turn, harbors an obfuscated Python-based stealer. This stealer is designed to exfiltrate all cookies and login credentials from various web browsers, sending the stolen information to an actor-controlled Telegram or Discord API endpoint.
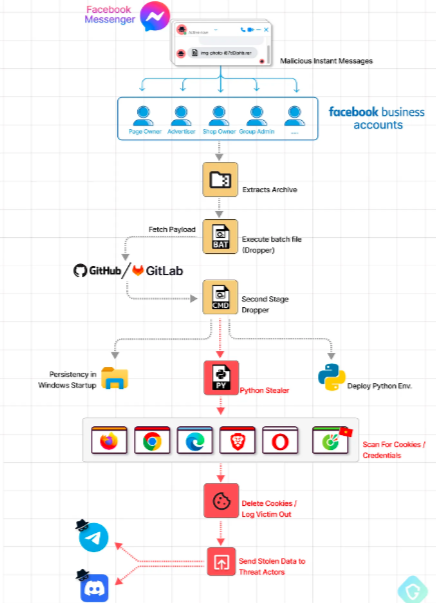
One cunning tactic used by the attackers involves deleting all stolen cookies after theft. This action effectively logs victims out of their own accounts, allowing the scammers to hijack their sessions. The stolen cookies are used to change victims’ passwords, enabling the attackers to seize control of the compromised accounts.
This campaign has seen a high success rate in compromising victim’s accounts, despite the fact that the infection requires user interaction to actually download the malicious file. The majority of victims have been reported from the US, Australia, Canada, France, Germany, Indonesia, Japan, Nepal, Spain, the Philippines, and Vietnam.
” These threat actors are targeting millions of business accounts on Facebook’s platform — from highly-rated marketplace sellers to large corporations, with fake business inquiries, achieving a staggering “success rate” with approximately 1 out of 70 infected!”, researchers mentioned
The main targets are Facebook accounts having high following, reputation and seller rating as these are easily sold for a big amount of money on dark markets. These kinds of accounts are used to reach a wider audience for spreading advertisements and scams.
Most of these Vietnam-related cyberthreats have similarities in their infrastructures and capabilities which suggest that the threat actors may have working relationships, like sharing tools and TTPs with each other.
Impact
- Identity Theft
- Credential Theft
Indicators of Compromise
Domain
- shoppingvideo247.com
MD5
- 54f90d3b8353c83f6c9760fa439ffcf5
- 684539ba644f89564a7a5dbc33c788e1
- 15d19f1bb46fdcab29d8df89eb1eba75
- 5fa892802e1df9033e0aae6d248b9a35
- 173b17e195b0a80611c22f333c3d2ec2
- 72619e9542f2491d08240a2416fc0293
- 29230c757551944a751a699259c5e021
- a0960542caf0b23e01da9dd379e64923
- 771a32eb5b45bda9e1b939e81060941b
- 3e9e177f8daf7e2d4589f9769761c2a2
- 13f94cda395bfdd2c87a024ee497e576
- be51f347873b4de0c027851a345e360a
SHA-256
- a39f0c56dd602fcc14adcdeaa31c21d389af8ea8abcb89862fac19e2807c799d
- 1af8a147d6e77ffcbf8e5dda14b32c715c4149b5e1c933fa69e451600ecfbf8e
- bca1c784742fc086d381f4e1e4495941626d1b829147d0d5f6d3f47af78364dd
- c116663954c00ef7be0ce7d391bed95fe0c1f775b97652906c49ec3fcd814719
- e7cd3233fd39175970675135dac2c582382747b328b3786f8a833ae2ab8f4239
- c95694003557ed3e22b29215ed8ee53c8560a1fbdc5ccce53aa3442aaf116a7e
- 474d1dcec292401ade40bd90a95b872e5ab2c8fb68737b786e4308444d3ad33a
- 91dff3d1e940290529d064a0b13e190e6231679ea067df399de559d5bd071d81
- d0237b6e1ab07c8300ad282ed3aa1f6e0e90220d893bbeee26786e886cedb9ad
- 12444acca1f75247e756516a5d3ca2a33d67641f0664c00c3220f141b3dd8ce1
- 3bf11184b67b82e367d36cb9ed3380a43814b000d84aef0bb89d4e08e4fcd581
- 0ed36afbfe255076e759c8fe4dca89b0e0d0de82c4ffd822f4f589f8b0f39688
SHA-1
- bf4dcafd866e888a1a6c77189dda53f1925f7a6a
- 4784572ae95b342b105a749ed59142392e205070
- cea7716f76731530dec498839dda308ac06fdf73
- 32ff452494c987910139ebeef9be58f5c2ede8f1
- 2a81754e3eac8123ee98b4060795489a3ed4f220
- 24378017b30b0feb2a2b6759810f933a62a6326e
- fe46d6dcfac42f886750cb60770aa34ef7a1c6a0
- a5d32afacd1bdd3a3a2e420e581e0dad0cfac532
- 2bc8afa2b021b410868120d74468dd1e6e16cd12
- 01e82d4c625911a83ab9e22d236984c456293a24
- 0bd8c2f2d263da163aab247b66986aa773f54a76
- b476eaad1c1ad62801ab37c2cb5679a8a50cd98d
Remediation
- Block all threat indicators at your respective controls
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Do not download documents attached in emails from unknown sources and strictly refrain from enabling macros when the source isn’t reliable.
- Enable antivirus and anti-malware software and update signature definitions in a timely manner. Using multi-layered protection is necessary to secure vulnerable assets
- Along with network and system hardening, code hardening should be implemented within the organization so that their websites and software are secure. Use testing tools to detect any vulnerabilities in the deployed codes.








