

Rewterz Threat Alert – IcedID Banking Trojan aka BokBot – Active IOCs
July 10, 2023
Rewterz Threat Alert – APT Group Gamaredon aka Shuckworm – Active IOCs
July 10, 2023
Rewterz Threat Alert – IcedID Banking Trojan aka BokBot – Active IOCs
July 10, 2023
Rewterz Threat Alert – APT Group Gamaredon aka Shuckworm – Active IOCs
July 10, 2023Severity
High
Analysis Summary
A new tool called “TeamsPhisher” has been made available on GitHub, allowing attackers to exploit a recently disclosed vulnerability in Microsoft Teams. This tool is designed to deliver malicious files to targeted Teams users within an organization. It specifically works in environments where internal Teams users can communicate with external users or tenants. The tool exploits a vulnerability highlighted by security services company Jumpsec. TeamsPhisher automates the attack process, utilizing techniques from various sources and verifying the target’s ability to receive external messages.
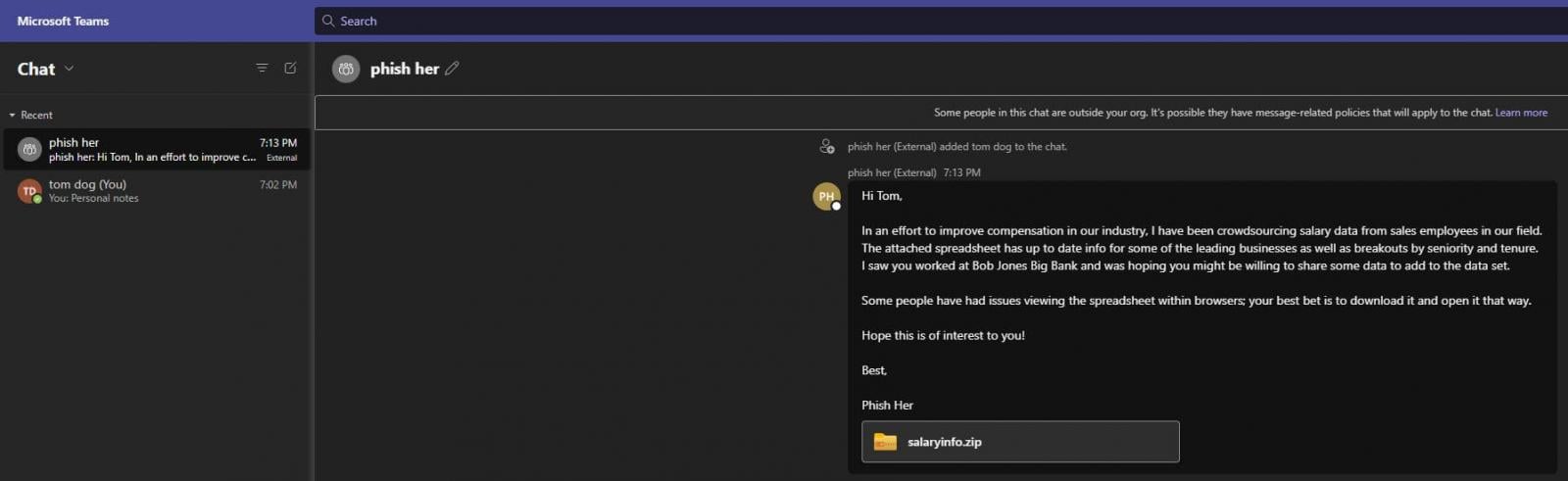
source: phishing message
The tool uploads an attachment to the sender’s Sharepoint and creates a new thread with the target user, sending them a message with a Sharepoint attachment link. TeamsPhisher requires a Microsoft Business account with a valid Teams and Sharepoint license. It offers a “preview mode” for verification and additional features such as sending secure file links and specifying transmission delays.
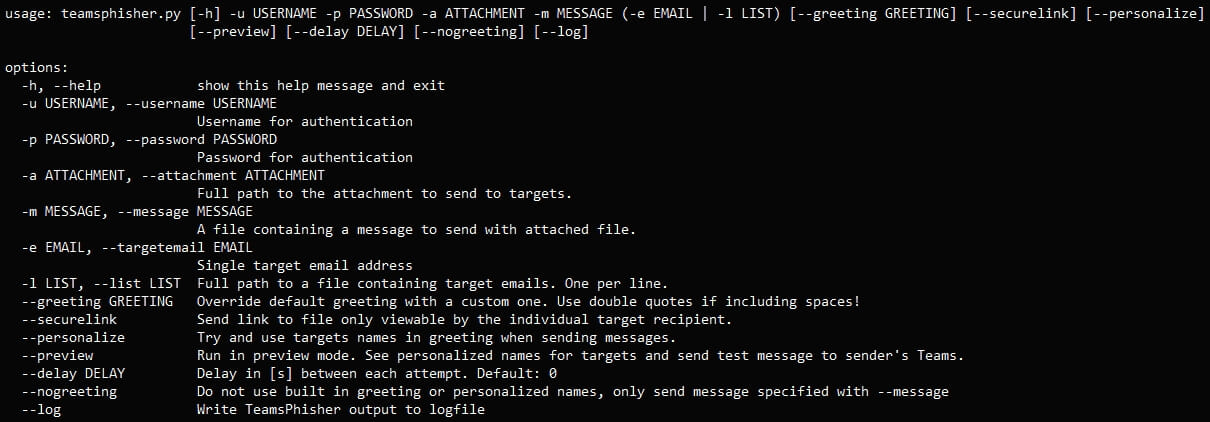
The security issue that TeamsPhisher exploits remains unresolved, with Microsoft stating that it does not meet the bar for immediate servicing. While the tool was developed for authorized red team operations, threat actors could potentially utilize it to deliver malware without detection. Organizations are advised to disable communications with external tenants if not necessary or create an allow-list with trusted domains to mitigate the risk.
The security services company has strongly advised organizations that utilize Microsoft Teams to carefully assess their business requirements for enabling communications between internal Teams users and external tenants. The company suggests that if there is no immediate need for regular communication with external parties, organizations should consider tightening their security controls and potentially disabling the option altogether.
“If you are not currently using Teams for regular communication with external tenants, tighten up your security controls and remove the option altogether,” the company advised.
Until Microsoft addresses the security issue, users are encouraged to exercise caution when interacting with links, opening files, or accepting file transfers.
Impact
- Security Bypass
- Unauthorized Access
- Malware Distribution
Remediation
- Evaluate the business need for enabling communication between internal Teams users and external tenants. If there is no significant requirement, consider disabling this feature altogether. By limiting external communication, the attack surface and the potential for malicious file delivery can be reduced.
- Strengthen the security controls within the Microsoft Teams environment. It includes enforcing strong authentication mechanisms, enabling multi-factor authentication (MFA), and implementing access controls to restrict unauthorized file transfers or interactions between internal and external users.
- Stay up-to-date with the latest security patches and updates provided by Microsoft for Microsoft Teams. Regularly applying these patches can help address known vulnerabilities and protect against potential exploitation.
- Educate users about the risks of phishing attacks and social engineering techniques used to deliver malware. Train them to exercise caution when clicking on links, opening attachments, or accepting file transfers, especially from external or unknown sources.
- Implement robust monitoring and detection mechanisms to identify any suspicious activities or attempts to exploit the security issue in Microsoft Teams. This can include monitoring for abnormal file transfer patterns, analyzing network traffic, and using security solutions that provide real-time threat intelligence and detection capabilities.
- Conduct regular security assessments and penetration testing to identify vulnerabilities and weaknesses within the Microsoft Teams environment. By proactively identifying and addressing security gaps, organizations can enhance their overall security posture.
- By implementing these remediation measures, organizations can reduce the risk of exploitation through the TeamsPhisher tool and enhance the overall security of their Microsoft Teams environment.








