

Rewterz Threat Alert – “Stealc” – An Information Stealer Malware – Active IOCs
May 22, 2023
Rewterz Threat Advisory – Multiple Apple iOS and iPadOS Vulnerabilities
May 22, 2023
Rewterz Threat Alert – “Stealc” – An Information Stealer Malware – Active IOCs
May 22, 2023
Rewterz Threat Advisory – Multiple Apple iOS and iPadOS Vulnerabilities
May 22, 2023Severity
High
Analysis Summary
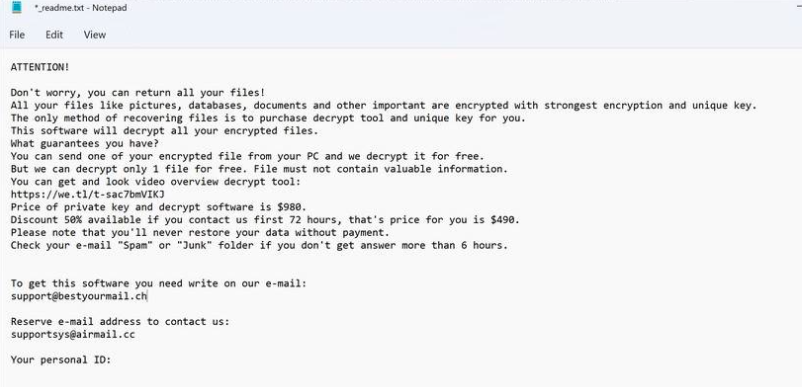
The STOP/DJVU ransomware initially made headlines in 2018 and has since been attacking individuals all around the world. It’s widespread on torrent sites and other platforms in software crack packages and adware bundles. DJVU Ransomware is a type of malicious software that encrypts the files on an infected computer and demands a ransom payment in exchange for the decryption key. The STOP/DJVU Ransomware family is one of the most prevalent ransomware threats and is known for its aggressive tactics and high-pressure ransom demands.
Malware is delivered via cracked applications, fake set-up apps keygens, activators, and Windows updates. It does not utilize local information like keyboard layouts or timezone settings to prevent infecting victims in certain countries; instead, it uses the information returned by a request to https[:]//api.2ip.ua/geo.json. The card’s MAC address is utilized to provide unique identification for the system. This identity is provided to STOP’s command and control server, which responded with an RSA-2048 public key for encryption. Additional malware, including an information stealer known as Vidar, is then downloaded and installed.
ransom note
Impact
- Information Theft
- File Encryption
Indicators of Compromise
MD5
- b9318925e37b36b0dc8998ed20c885d4
- e131c4a8304d2b552494a4c6c9e73783
- 30fc2818fae728f85b009067581780fa
SHA-256
- 8925834d9802482b1aaf21d76089690975b722f0c662a0fa12d77ae9df291de3
- 0221aa3aeb9d83a2e440d4081d2b46b85a916bb8ed8e32fa3434344180c52be0
- de319fe12278039b303cc168577005419bb443e13e3558c50059a31327983ce7
SHA-1
- 194f68d06f0101844bbb8e2cae7bb8785170a079
- df9c718854a3b7dca0033260faf491e0dc1cbe77
- 5f46f5eb2a8da0e1a0d523b9c4198bc1a4d8b182
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Emails from unknown senders should always be treated with caution.
- Never trust or open ” links and attachments received from unknown sources/senders
- Patch and upgrade any platforms and software timely and make it into a standard security policy. Prioritize patching known exploited vulnerabilities and zero-days.
- Enable antivirus and anti-malware software and update signature definitions in a timely manner. Using multi-layered protection is necessary to secure vulnerable assets.








