

Rewterz Threat Advisory – Multiple IBM Aspera Vulnerabilities
June 5, 2023
Rewterz Threat Alert – STOP (DJVU) Ransomware – Active IOCs
June 5, 2023
Rewterz Threat Advisory – Multiple IBM Aspera Vulnerabilities
June 5, 2023
Rewterz Threat Alert – STOP (DJVU) Ransomware – Active IOCs
June 5, 2023Severity
High
Analysis Summary
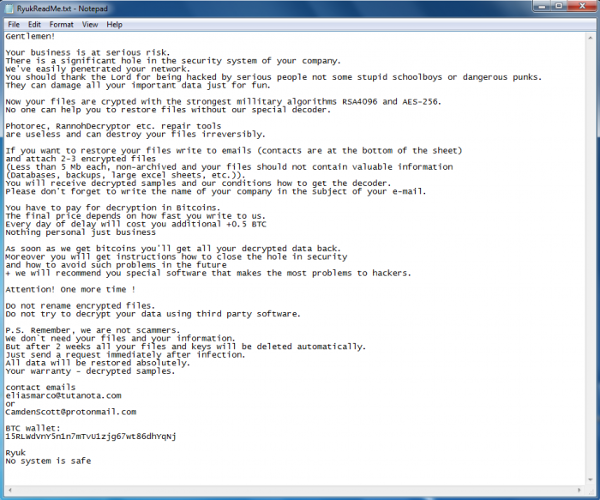
Ryuk Ransomware is a ransomware family that was first found in the wild in August 2018. It is one of the most virulent ransomware strains on the market. Ryuk has been observed being used to attack companies or professional environments. This ransomware can lock your files or systems and hold them hostage for ransom. Ryuk targets high-profile enterprises in order to obtain essential information that will impair the victim’s operations. The operators of Ryuk invest time in understanding the compromised network’s infrastructure and valuable assets. They employ manual techniques to disable security measures, move laterally within the network, and identify and encrypt critical data. This customized approach enhances their chances of extorting a higher ransom amount. The ransom amounts associated with Ryuk attacks are often substantial, with reported payments ranging from hundreds of thousands to millions of dollars in cryptocurrency.
Ryuk is a form of ransomware used in targeted attacks, in which threat actors encrypt important data to demand big ransom payments. Emotet or TrickBot malware is widely used to spread Ryuk ransomware. Ryuk’s code is comparable to that of the Hermes ransomware. The Ryuk ransomware is believed to be operated by the Russian cybercriminal group WIZARD SPIDER.
Impact
- File Encryption
- Privilege Escalation
- Information Theft
- Data Exfiltration
- Network Compromise
Indicators of Compromise
Domain Name
- gg1593.c1.biz
MD5
- 52a2853357e1f5fffaccfe3807a10593
- 5661aec52fcc80ccd4c5d263e113c115
SHA-256
- fe55650d8b1b78d5cdb4ad94c0d7ba7052351630be9e8c273cc135ad3fa81a75
- 6cbc05acf871c106f7804069fffef908472a31ea1a782add45a100d14c8f5ea0
SHA-1
- 6daaabe57e551e792179d2374059e3cab18fcd12
- b09fb5cfbfbadd6afdd536aa89ccab405ef8c5b2
Remediation
- Block all threat indicators at your respective controls.
- Search for IOCs in your environment.
- Maintain cyber hygiene by updating your anti-virus software and implementing a patch management lifecycle.
- Maintain Offline Backups – In a ransomware attack, the adversary will often delete or encrypt backups if they have access to them. That’s why it’s important to keep offline (preferably off-site), encrypted backups of data and test them regularly.
- Emails from unknown senders should always be treated with caution.
- Never trust or open ” links and attachments received from unknown sources/senders.








