

Rewterz Threat Alert – Evasive Panda APT Delivers MgBot Malware To Target International NGOs In Mainland China – Active IOCs
April 28, 2023
Rewterz Threat Advisory – CVE-2023-21990 – Oracle JVM VirtualBox Vulnerability
April 28, 2023
Rewterz Threat Alert – Evasive Panda APT Delivers MgBot Malware To Target International NGOs In Mainland China – Active IOCs
April 28, 2023
Rewterz Threat Advisory – CVE-2023-21990 – Oracle JVM VirtualBox Vulnerability
April 28, 2023Severity
High
Analysis Summary
A new QBot malware campaign has been discovered by Kaspersky researchers, which is leveraging hijacked business correspondence to trick victims into installing the malware. The campaign began on April 4, 2023, and has primarily targeted users in several countries, including Germany, Argentina, Italy, Algeria, Spain, the US, Russia, France, the UK, and Morocco. QBot, also known as Qakbot or Pinkslipbot, is a banking trojan that has been active since at least 2007. The malware is capable of stealing passwords and cookies from web browsers and acting as a backdoor to inject next-stage payloads such as Cobalt Strike or ransomware.
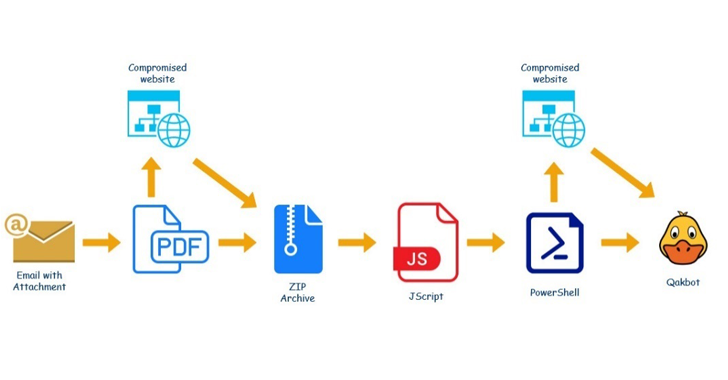
QBot is distributed through malware already residing on victims’ computers, social engineering, and spam mailings. In this campaign, the attackers are using email thread hijacking attacks to insert themselves into existing business conversations or initiate new ones based on compromised email accounts. The attackers are using an enclosed PDF file that appears to be a Microsoft Office 365 or Microsoft Azure alert. When victims open the document, it leads to the retrieval of an archive file from an infected website that contains an obfuscated Windows Script File (.WSF). The script incorporates a PowerShell script that downloads a malicious DLL from a remote server. The downloaded DLL is the QBot malware. Kaspersky researchers also noted that the QBot malware has seen constant updates during its lifetime that include anti-VM, anti-debugging, and anti-sandbox techniques to evade detection. It is currently the most prevalent malware for the month of March 2023, according to Check Point.
In a related development, researchers have discovered a multi-stage social engineering campaign that uses weaponized Microsoft Word documents to distribute Agent Tesla and XWorm by means of a custom .NET-based loader.
The trojan’s spreading tactics have developed as well. Previously, it was delivered via malicious websites and pirated applications. “The banker (banking trojan) is now delivered to potential victims via malware already present on their computers, social engineering, and spam mailings,” they conclude.
It is important for organizations and individuals to be vigilant and take proactive steps to protect against malware campaigns like QBot. This includes implementing strong security measures, such as using reputable antivirus software, regularly updating software and operating systems, enabling two-factor authentication, and being cautious of suspicious emails and attachments.
Impact
- Unauthorized Access
- Financial Theft
- Information Theft
Indicators of Compromise
MD5
- 299fc65a2eecf5b9ef06f167575cc9e2
- a6120562eb673552a61f7eeb577c05f8
SHA-256
- 6449a2a841019fdf88fc388c4c3d07872f4e3be89e866795b9f632d249a59e3e
- 28f092cd301b16e3bdfdb7e12c4480254174009bbaf17a72cc14833289baa360
SHA-1
- ebcfbd9c6f3d465cc821f2c88ad56d58a83253d9
- 94d44e96ccce74b57b1efc2a11905c625a40357c
Domain Name
- rosewoodlaminates.com
- agtendelperu.com
- capitalperurrhh.com
- centerkick.com
- chimpcity.com
- graficalevi.com.br
- kmphi.com
- propertynear.co.uk
- theshirtsummit.com
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Emails from unknown senders should always be treated with caution. Never trust or open links and attachments received from unknown sources/senders.
- Maintain cyber hygiene by updating your anti-virus software and implementing a patch management lifecycle.
- Patch and upgrade any platforms and software timely and make it into a standard security policy. Prioritize patching known exploited vulnerabilities and zero-days.
- Enable antivirus and anti-malware software and update signature definitions in a timely manner. Using multi-layered protection is necessary to secure vulnerable assets.








