

Rewterz Threat Alert – APT37 aka GoldBackDoor Group – Active IOCs
June 9, 2023
Rewterz Threat Alert – STOP (DJVU) Ransomware – Active IOCs
June 9, 2023
Rewterz Threat Alert – APT37 aka GoldBackDoor Group – Active IOCs
June 9, 2023
Rewterz Threat Alert – STOP (DJVU) Ransomware – Active IOCs
June 9, 2023Severity
High
Analysis Summary
A recent espionage campaign in North Africa has raised concerns as a new custom backdoor called “Stealth Soldier” has been deployed. The campaign involves highly-targeted attacks and is characterized by the use of command-and-control (C&C) servers that mimic websites belonging to the Libyan Ministry of Foreign Affairs. According to a technical report by cybersecurity company, the earliest artifacts associated with the campaign date back to October 2022.
The Stealth Soldier malware is described as an undocumented backdoor that primarily focuses on surveillance functions. It is capable of performing various malicious activities, including file exfiltration, screen and microphone recording, keystroke logging, and stealing browser information. Researchers warn that the malware is modular in nature, indicating that it is designed for flexibility and can potentially evolve with new capabilities in the future. The researchers have discovered three versions of the Stealth Soldier backdoor, suggesting active maintenance by the threat actors.
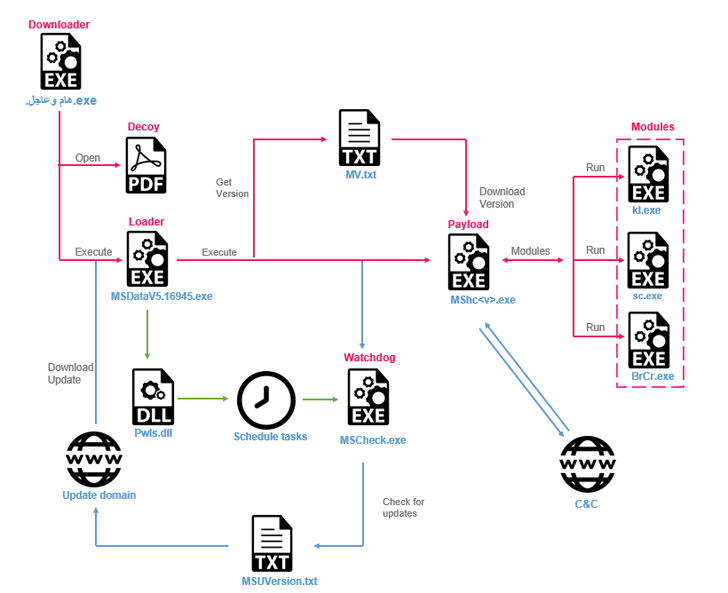
The attack starts with potential targets downloading fake downloader binaries through social engineering techniques. These binaries serve as a conduit for retrieving the Stealth Soldier backdoor onto the victim’s system. Simultaneously, a decoy empty PDF file is displayed to deceive the user. Once installed, the malware enables the attackers to gather directory listings, capture keystrokes, take screenshots, upload files, and execute PowerShell commands. Researchers note that some components of the malware, such as the screen capture and browser credential stealer plugins, appear to have been inspired by open-source projects available on GitHub.
Interestingly, there are overlaps between the infrastructure used in the Stealth Soldier campaign and another phishing campaign known as “Eye on the Nile.” Eye on the Nile targeted Egyptian journalists and human rights activists in 2019. This connection suggests a potential re-emergence of the same threat actor, indicating a continued focus on surveillance against Egyptian and Libyan targets.
It was predicted that the attackers behind Stealth Soldier are likely to evolve their tactics and techniques, deploying new versions of the malware in the near future. Given the sophistication and modularity of the malware, it is crucial for organizations and individuals in the affected regions to remain vigilant, apply security patches, and follow best practices to mitigate the risk of falling victim to these targeted attacks.
Impact
- Unauthorized access
- Information theft
- Exposure of sensitive data
Indicators of Compromise
Domain Name
- filestoragehub.live
- customjvupdate.live
- filecloud.store
- webmailogemail.com
IP
- 94.156.33.228
- 94.156.33.229
MD5
- 1ea8a827ad4c565b1c2ae43b0a020092
- 0db6239ad0755392c31a09e58773cd3b
- a418886a31852be25064d3573f2bc87d
- b9c7e04b892f21984b4f8e318e07caa7
- 7d0fdc7b1cc7fdb95019d3d76ad56ed2
- 027e013d26197ccd4c0a38c0b8704f75
- f325716b2a4c3414ea7e5b95728753c8
- e713e4d65877a8b549a51203832183ec
- f722013acb21448189cbae852e4a287e
- 1791cc958b2d00a884167d8e4c41fe75
- c9152cb6d094d7a8739c56c91a437fe2
SHA-256
- 2cad816abfe4d816cf5ecd81fb23773b6cfa1e85b466d5e5a48112862ceb3efb
- 05db5e180281338a95e43a211f9791bd53235fca1d07c00eda0be7fdc3f6a9bc
- b9e9b93e99d1a8fe172d70419181a74376af8188dcb03249037d4daea27f110e
- d57fc4e8c14da6404bdcb4e0e6ac79104386ffbd469351c2a720a53a52a677db
- e7794facf887a20e08ed9855ac963573549809d373dfe4a287d1dae03bffc59f
- 8c09a804f408f7f9edd021d078260a47cf513c3ce339c75ebf42be6e9af24946
- df6a44551c7117bc2bed2158829f2d0472358503e15d58d21b0b43c4c65ff0b4
- e546d48065ff8d7e9fef1d184f48c1fd5e90eb0333c165f217b0fb574416354f
- c0b75fd1118dbb86492a3fc845b0739d900fbbd8e6c979b903267d422878dbc6
- cb90a9e5d8b8eb2f81ecdbc6e11fba27a3dde0d5ac3d711b43a3370e24b8c90a
- d6655e106c5d85ffdce0404b764d81b51de54447b3bb6352c5a0038d2ce19885
SHA-1
- 9c80d85e90175ec3bf419a902f2bdb8420628516
- 5c55009e452039f73fddd503648caf6bd82eb451
- a32c247d543ed54f5a4a881882fef8e14840234c
- 9d98fc4aed2a1fc1810b9a432465e32c612f5fa0
- b584cde1421bf311f274eb20cbf1161efc37f2ca
- 3241787f7fff3d2580ca99ae4ccbdcd92ed58100
- cfd4f53f986afad33d702e39691a2a90140bb8a3
- ddf129abed288f4f7aee17e8df1238d6c146d92f
- 54865875d13d78843b9670d0808b56089f1f8b1c
- ca336d78c77e74e9fc89abe5351ad5c0614c281a
- 1ffc141241ee5644d1e3b7a37dcafa89d5ddabb0
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Emails from unknown senders should always be treated with caution.
- Never trust or open links and attachments received from unknown sources/senders
- Maintain cyber hygiene by updating your anti-virus software and implementing a patch management lifecycle.
- Patch and upgrade any platforms and software timely and make it into a standard security policy. Prioritize patching known exploited vulnerabilities and zero-days.
- Change your passwords: If you suspect that your passwords may have been compromised, it is important to change them immediately. Use strong, unique passwords for each account and enable two-factor authentication wherever possible.
- Disable any suspicious processes: Use the Windows Task Manager to check for any suspicious processes running on your system and disable them. Look for any processes that are using a lot of CPU or memory resources or that you don’t recognize.
- Stay vigilant: Keep an eye out for any suspicious activity on your system and avoid downloading or opening any suspicious files or links.








