

Rewterz Threat Advisory – Multiple Security Vulnerabilities In Cisco Products
June 18, 2020
Rewterz Threat Advisory – CVE-2020-3355 – Cisco Data Center Network Manager Stored Cross-Site Scripting Vulnerability
June 18, 2020
Rewterz Threat Advisory – Multiple Security Vulnerabilities In Cisco Products
June 18, 2020
Rewterz Threat Advisory – CVE-2020-3355 – Cisco Data Center Network Manager Stored Cross-Site Scripting Vulnerability
June 18, 2020Severity
High
Analysis Summary
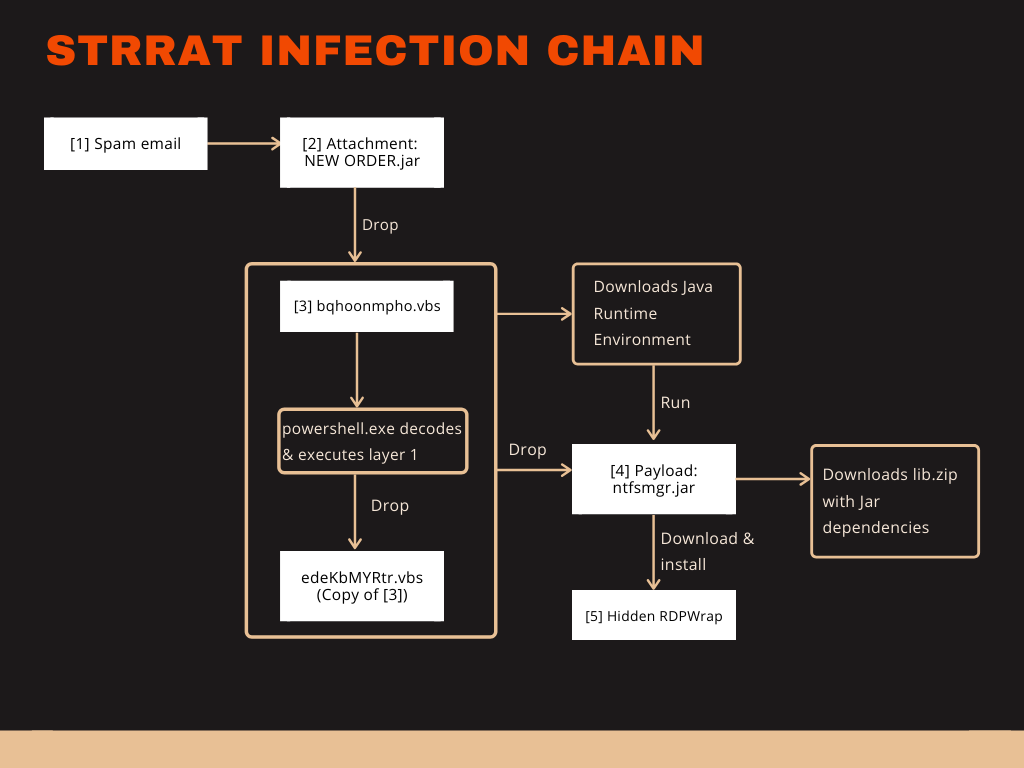
Java has a new RAT titled STRRAT that is now shipping with the .crimson ransomware module. Typical infection begins with a spam email containing a malicious attachment with a .JAR extension. This JAR file drops a .VBS file which executes a script via PowerShell. This script drops a second .VBS file. This file downloads the Java Runtime Environment allowing the payload ntfsmgr.jar to download and install a hidden RDPWrap. Finally, there is a download of lib.zip containing jar dependencies. With a variety of commands at its disposal, this RAT is robust and persistent. Features contained in the RAT include rebooting the machine, downloading and executing files, enabling cmd.exe, keylogging, and a rudimentary ransomware module. This module appends .crimson to encrypted files. This RAT is limited in that it only works with Windows machines, needs a pre-installed JRE (presently), and Outlook blocks the attachment.
Impact
File encryption
Indicators of Compromise
SHA-256
- e6b0a56662d1f0544257c63e63b2f85ad7215f0df3a7f5a689dee66f27e24db7
- 0f0e25e859bc6f21447ed196d557eb6cdba9737dd3de22a5183a505da0126302
- b76e2eea653b480c8a559215aa08806fad4c83c60f9a5996e89d51709212ee29
- 7c24d99685623b604aa4b2686e9c1b843a4243eb1b0b7b096d73bcae3d8d5a79
- ac92d4c6397eb4451095949ac485ef4ec38501d7bb6f475419529ae67e297753
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.








