

Rewterz Threat Advisory – CVE-2023-33858 – IBM Business Automation Workflow Vulnerability
September 5, 2023
Rewterz Threat Alert – CVE-2023-41180 – Apache NiFi MiNiFi C++ Vulnerability
September 5, 2023
Rewterz Threat Advisory – CVE-2023-33858 – IBM Business Automation Workflow Vulnerability
September 5, 2023
Rewterz Threat Alert – CVE-2023-41180 – Apache NiFi MiNiFi C++ Vulnerability
September 5, 2023Severity
High
Analysis Summary
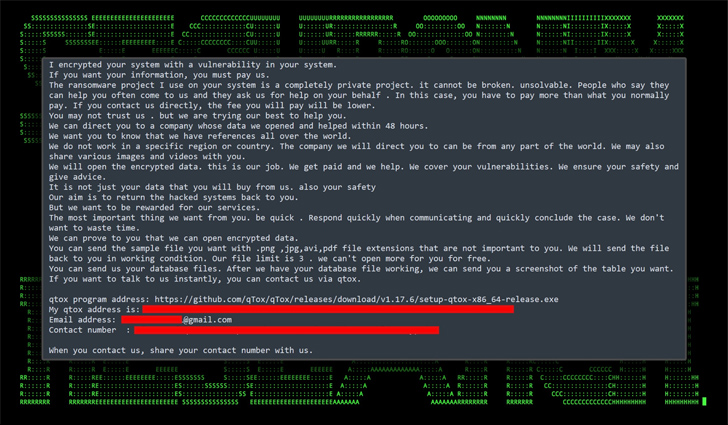
Threat actors have initiated a campaign known as DB#JAMMER, exploiting poorly secured Microsoft SQL (MS SQL) servers to deploy both Cobalt Strike and a ransomware strain identified as FreeWorld. A Cybersecurity firm has detailed this campaign, highlighting its unique approach to utilizing tools and infrastructure.
The campaign encompasses various tools, such as enumeration software, Remote Access Trojan (RAT) payloads, exploitation and credential-stealing software, and ransomware payloads. Of note, the attackers have shown a preference for a newer variant of the Mimic ransomware known as FreeWorld.
The initial access to victim hosts involves brute-forcing the MS SQL server, followed by database enumeration. The attackers leverage the xp_cmdshell configuration option to execute shell commands and perform reconnaissance. Subsequently, they manipulate the system firewall, establish persistence, and transfer files to and from the victim system via a remote SMB share. Malicious tools, including Cobalt Strike, are then installed to facilitate further actions.
The final step in this campaign involves distributing AnyDesk software and deploying the FreeWorld ransomware. A lateral movement phase is conducted before these actions. The threat actors have also attempted to establish Remote Desktop Protocol (RDP) persistence through Ngrok, although unsuccessfully.
The researchers emphasize that this attack initially succeeded due to a brute force attack on an MS SQL server, highlighting the critical importance of strong passwords, particularly for publicly exposed services.
This campaign emerges as the operators of Rhysida ransomware have claimed 41 victims, with a significant portion located in Europe. Rhysida is a relatively new ransomware strain that encrypts and exfiltrates sensitive data, threatening to release it if victims refuse to pay.
Additionally, a free decryptor has been released for the Key Group ransomware, which exploits cryptographic errors in the program. However, this script only works on samples compiled after August 3, 2023.
The year 2023 has witnessed a substantial increase in ransomware attacks compared to the previous year. Notably, the percentage of incidents resulting in ransom payment has decreased to a record low of 34%, while the average ransom amount paid has risen to $740,144, representing a 126% increase from Q1 2023.
This shifting landscape is accompanied by ransomware threat actors evolving their tactics, including sharing details of their attack techniques to invalidate cyber insurance claims, thereby pressuring victims to pay.
Impact
- Financial Loss
- Sensitive Data Theft
Indicators of Compromise
Domain Name
gelsd.com
IP
45.148.122.63
MD5
- d59aa49740acb5e45ecb65da070035e3
- dbf9675bd273e982ca5de58ac32de399
- ac34ba84a5054cd701efad5dd14645c9
- 764630841c96eaef0af17af9be00d83a
- ed34dafa3114c6dbbdfc777f2588f001
SHA-256
- 80bf2731a81c113432f061b397d70cac72d907c39102513abe0f2bae079373e4
- 75975b0c890f804dab19f68d7072f8c04c5fe5162d2a4199448fc0e1ad03690b
- c576f7f55c4c0304b290b15e70a638b037df15c69577cd6263329c73416e490e
- 95a73b9fda6a1669e6467dcf3e0d92f964ede58789c65082e0b75adf8d774d66
- 08f827a63228d7bcd0d02dd131c1ae29bc1d9c3619be67ea99d8a62440be57ab
SHA-1
- 4086107b3fb71fb02361306da6099a85be97ae1d
- 5e6df45bdc8d4a5f711988672cc43643fb35a876
- dc74a9fd5560b7c7a0fc9d183de9d676e92b9e8b
- 4f4e409278a9c069e6917ce44c3188d4495c2dff
- 31074f6d4e8af88c7ea1b4b8db93b62cc089ad2d
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Continuously monitor your network and systems for any signs of suspicious or unauthorized activity. Implement intrusion detection and prevention systems to identify potential attacks.
- Consider using Web Application Firewalls to help detect and block malicious traffic targeting vulnerabilities like the one described.
- Implement network segmentation to isolate critical systems and sensitive data from potentially compromised systems.
- Disable any unnecessary services or features on your Citrix appliances. This can reduce the potential attack surface and limit the opportunities for attackers to exploit vulnerabilities.
- Ensure that all software and applications on your network are up to date with the latest security patches. Regularly update operating systems, browsers, plugins, and other software components.
- Apply the principle of least privilege, granting users and systems only the access and permissions they need to perform their tasks.
- Regularly back up critical data and systems. In the event of a successful attack or compromise, having recent backups can help you restore operations and minimize data loss.
- Establish a robust patch management process to promptly apply security updates and patches to all software and systems in your environment.








