

Rewterz Threat Alert – North Korean Lazarus APT group Push Linux Malware In Recent Attacks Via Fake Job Offers – Active IOCs
April 21, 2023
Rewterz Threat Alert – New All-in-One Stealer ‘EvilExtractor’ Campaign Targets Windows User Data – Active IOCs
April 24, 2023
Rewterz Threat Alert – North Korean Lazarus APT group Push Linux Malware In Recent Attacks Via Fake Job Offers – Active IOCs
April 21, 2023
Rewterz Threat Alert – New All-in-One Stealer ‘EvilExtractor’ Campaign Targets Windows User Data – Active IOCs
April 24, 2023Severity
Medium
Analysis Summary
An Iranian government-backed actor, dubbed as Mint Sandstorm, has been linked to attacks on critical infrastructure in the U.S between late 2021 to mid-2022.
“This Mint Sandstorm subgroup is technically and operationally mature, capable of developing bespoke tooling and quickly weaponizing N-day vulnerabilities, and has demonstrated agility in its operational focus, which appears to align with Iran’s national priorities,” according to the Threat Intelligence team
Mint Sandstorm is a threat actor group known for targeting both private and public organizations, including political dissidents, journalists, activists, the Defense Industrial Base (DIB), and employees from multiple government agencies. The group has been known to engage in cyber espionage, stealing sensitive information and credentials, as well as conducting cyberattacks aimed at disrupting the operations of targeted organizations.
The activity associated with Mint Sandstorm overlaps with several other threat actor groups, including APT35, APT42, Charming Kitten, and TA453.
According to Microsoft, the Mint Sandstorm subgroup attacked several key US infrastructure from late 2021 to mid-2022, including seaports, energy companies, transit systems, and a US utility and gas entity. The operations were carried out in retaliation for catastrophic cyberattacks that targeted the nation’s railway network, marine activity at a significant Iranian seaport, and the nation’s petrol station payment systems.
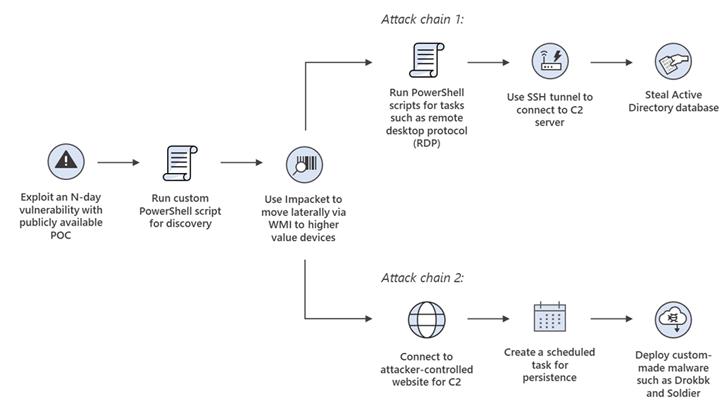
Following a successful breach, a customised PowerShell script is deployed and used to launch one of two attack chains. The first attack chain uses additional PowerShell scripts to connect to a remote server and steal Active Directory datasets.
The second phase involves connecting to an actor-controlled server via Impacket in order to install a custom implant named Soldier, a multistage.NET backdoor that has the ability to download and run tools as well as remove itself, and a bespoke implant called Drokbk.
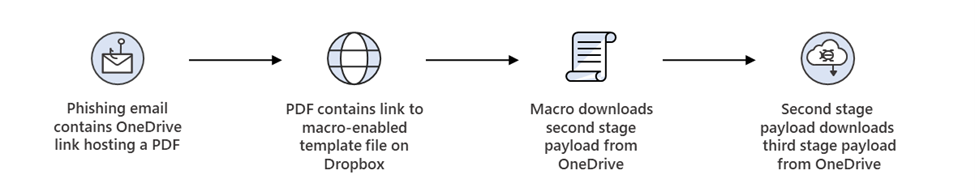
Microsoft also claimed the threat actor of conducting low-volume phishing efforts that culminated in the usage of CharmPower, a third bespoke and modular backdoor that can read files, acquire host information, and exfiltrate data.
“Capabilities observed in intrusions attributed to this Mint Sandstorm subgroup are concerning as they allow operators to conceal C2 communication, persist in a compromised system, and deploy a range of post-compromise tools with varying capabilities.”
They also added that “A successful intrusion creates liabilities and may harm an organization’s reputation, especially those responsible for delivering services to others such as critical infrastructure providers, which Mint Sandstorm has targeted in the past.”
Impact
- Unauthorized Access
- Financial Theft
- Information Theft
Indicators of Compromise
Domain Name
- sync-system-time.cf
- update-windows-security.tk
- dns-iprecords.tk
- universityofmhealth.biz
- oracle-java.cf
- 0onlyastep0.xyz
- 0readerazone0.xyz
- 0tryamore0.xyz
IP
- 54.39.202.0
- 51.89.135.15
- 51.89.169.201
- 51.89.187.222
MD5
- 45b50d42e8d827ca0373c12533211c33
- cdf4108bf0abf29a51feeaa42b44c09b
- 052fbe0aaefa848bdf109b982fc161e3
- 06e5891856dacb6f1b15c2d2f66277c4
SHA-256
- 57cc5e44fd84d98942c45799f367db78adc36a5424b7f8d9319346f945f64a72
- 3dcdb0ffebc5ce6691da3d0159b5e811c7aa91f6d8fc204963d2944225b0119d
- 65e48f63f455c94d3bf681acaf115caa6e1e60499362add49ca614458bbc4f85
- 444075183ff6cae52ab5b93299eb9841dcd8b0321e3a90fb29260dc12133b6a2
SHA-1
- b98a24144067ec3605e84158e12d6498222295ae
- 46d401f4c829521629d7cccb8885a2662c46ff67
- 3a1085bbd318fc304037a596abf3521245fad92b
- 5d329849b3359aa13733c0d7279d1db7c8ac15ac
Recommendations
Mitigating against a nation-state threat actor such as Mint Sandstorm can be challenging, as they often have significant resources and expertise at their disposal. However, there are several steps that organizations can take to protect themselves against this type of threat:
- Implement strong access controls: This includes using multi-factor authentication, strong passwords, and limiting access to sensitive systems and data.
- Regularly patch and update systems: Keeping systems up-to-date with the latest security patches and configurations is essential to prevent known vulnerabilities from being exploited.
- Monitor network activity: This includes using intrusion detection and prevention systems to detect and respond to potential attacks.
- Conduct regular vulnerability assessments: This can help identify and remediate weaknesses in network defenses before they can be exploited by attackers.
- Implement network segmentation: Limiting access to critical systems through network segmentation can help prevent lateral movement by attackers in the event that they gain access to the network.
- Prioritize employee training and awareness: This can help prevent social engineering attacks, such as phishing, which are commonly used by nation-state threat actors to gain access to sensitive systems and data.
- Have an incident response plan in place: This should include regular testing and updating of the plan to ensure that it remains effective in the face of evolving threats.
While these measures may not guarantee protection against all nation-state threat actors, they can significantly reduce an organization’s risk and make it more difficult for attackers to successfully compromise their systems and data.
Also, click here to check some of the mitigations and protection guide provided by Microsoft against the techniques used by this Mint Sandstorm group.








