

Rewterz Threat Alert –Ursnif Banking Trojan – Active IOCs
June 8, 2021
Rewterz Threat Advisory – ICS: Schneider Electric IGSS
June 9, 2021
Rewterz Threat Alert –Ursnif Banking Trojan – Active IOCs
June 8, 2021
Rewterz Threat Advisory – ICS: Schneider Electric IGSS
June 9, 2021Severity
High
Analysis Summary
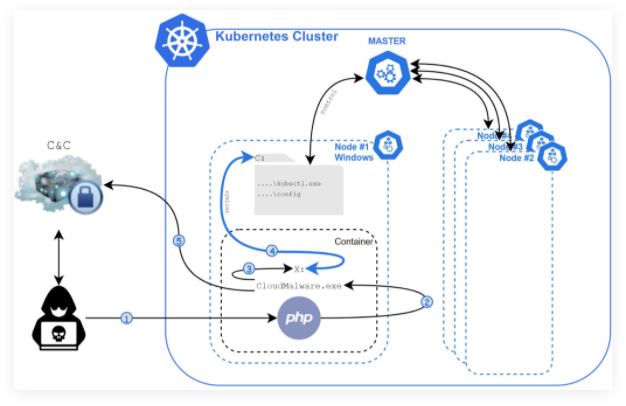
Siloscape – like silo + escape – is a new malware that targets windows containers. This comes as no surprise to anyone since cloud adoption has escalated aggressively over the last few years. Siloscape is a heavily obfuscated malware targeting Kubernetes clusters through Windows containers. Siloscape aims to open a backdoor into poorly configured Kubernetes clusters in order to run malicious containers.
Siloscape targets clusters instead of individual containers as they contain much more information like usernames and passwords for an entire organization, internal files, and confidential data, and even entire databases. What’s worse is that the attack could be escalated to ransomware instead of simply being a malware infestation attack.
Another critical problem arises as many organizations, moving to the cloud, use Kubernetes clusters as their testing and development environments. A breach of such an environment can lead to devastating software supply chain attacks. The .onion domain is used by the Tor proxy to anonymously connect to a C2 (command and control) server.
Several techniques and behaviors characterize the malware:
- The malware uses zero-day vulnerabilities or exploits-in-the-wild to target common clouds and gain initial access to web servers.
- The malware uses Windows container escape techniques to escape the container and gain code execution on the underlying node.
- To spread in the cluster, it abuses the node’s credentials.
- It then connects to the C2 server over the Tor network (using the IRC protocol).
- And then waits for further commands.
The malware can also leverage Kubernetes computing resources for data exfiltration and crypto-jacking.
Flow and behavior:
- Using a vulnerability, the attacker achieves RCE (remote code execution) inside a Windows container.
- The CloudMalware.exe Siloscape is executed with the necessary C2 connection information.
- CExecSvc.exe is impersonated by Siloscape to obtain SeTcbPrivilege privileges.
- A global link to the host is created.
- The Kubernetes config file is searched by Siloscape.
- Siloscape checks if the compromised node has enough privilege to create new Kubernetes deployments.
- An unzip binary is used by Siloscape to extract the Tor client.
- Siloscape connects to the Tor network.
- The C2 server’s password is decrypted by Siloscape.
- The .onion domain is used by the Tor proxy to anonymously connect to a C2 server.
- Siloscape waits for commands from the C2 and executes them.
The IOCs attached are vendor IOCs for their own variant.
Impact
- Information and credential theft
- Ransomware
- File encryption
- Data exfiltration
- Backdoor creation
Indicators of Compromise
MD5
- fecf803f7d84d4cfa81277298574d6e6
SHA-256
- 81046f943d26501561612a629d8be95af254bc161011ba8a62d25c34c16d6d2a
- 5B7A23676EE1953247A0364AC431B193E32C952CF17B205D36F800C270753FCB
- 010859BA20684AEABA986928A28E1AF219BAEBBF51B273FF47CB382987373DB7
SHA1
- 0fd9a61bf9a361f87661de295e70a9c6795fe6a1
Remediation
- Do not use Window’s containers as a security feature.
- Use Hyper-V containers instead as a security boundary.
- Any process running in Windows Server containers should be assumed to have the same privileges as admin on the
- host (Kubernetes node).
- Securely configure the Kubernetes cluster.
- keep clouds well-configured and secured.








