

Rewterz Threat Alert – XLoader macOS Malware Variation Concealed as ‘OfficeNote’ Productivity Software – Active IOCs
August 22, 2023
Rewterz Threat Advisory – Multiple Google Chrome Vulnerabilities
August 23, 2023
Rewterz Threat Alert – XLoader macOS Malware Variation Concealed as ‘OfficeNote’ Productivity Software – Active IOCs
August 22, 2023
Rewterz Threat Advisory – Multiple Google Chrome Vulnerabilities
August 23, 2023Severity
High
Analysis Summary
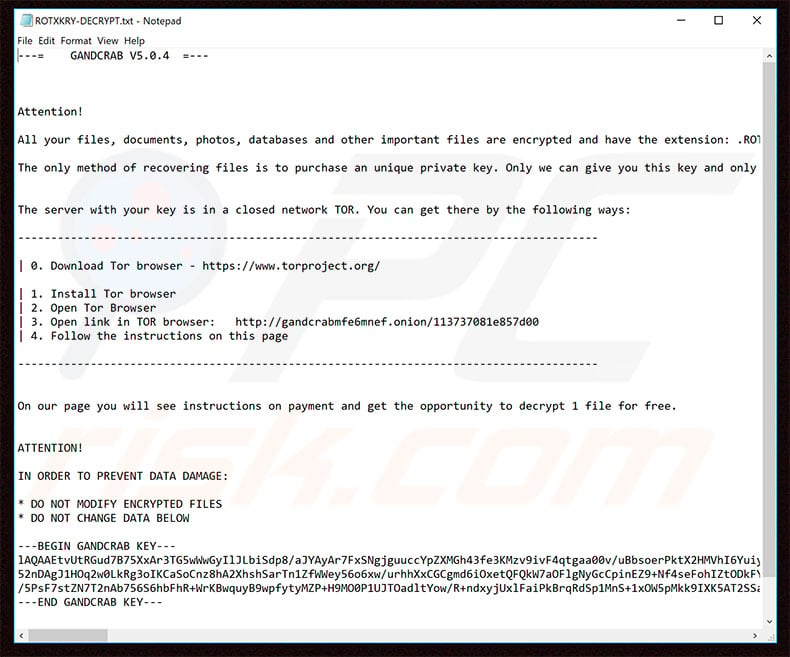
GandCrab – a ransomware-as-a-service variant – was discovered in early 2018. At least five versions of GandCrab have been created since its discovery. GandCrab ransomware encrypts victims’ files and demands ransom money in exchange for decryption keys. GandCrab targets organizations and individuals that use Microsoft Windows-powered PCs. This ransomware has attacked a huge number of systems in India, Chile, Peru, the United States, and the Philippines. This ransomware has been linked to some of the most notorious ransomware outbreaks, resulting in enormous financial losses for victims. To effectively victimize the target, its operators frequently try to imitate reputable services. In January 2020, for example, GandCrab was transmitted in a word document labeled “Flu pandemic warning.doc” that purportedly came from the Centers for Disease Control. The virus is assigned various name by different antivirus software including Trojan.Ransom.GandCrab, Win32/Filecoder.GandCrab, Ransom: Win32/GandCrab, and others
Impact
- Files Encryption
Indicators of Compromise
MD5
- ffd686da1923301cdc6190a15052f15f
- ee7cc21d62fd495198159bbae80dbcc2
- ce4d60928635dd4d4abb874224733f71
- 7e3b2b10d66955465c12da9f2ab43e36
- 4d68c9b40f348262248e55ec972892ab
- 2e0d33ba5dbfa8eccdcbddc0bc3b3390
SHA-256
- 7c91058133a449a21c3032d23853121b90fc990a8f5a33e8eb12497230a49399
- c14ebfc076f06e2194587fd7246a520c648f78c4ed730be88c6f6deb0ae1f70a
- a4fc5a4d4ab1c6834e63f2e3d7e9dcd5e874357c0cb5673215e97d67752b4a8f
- 01aabfaa4177d8d4953a65e8c0d92df98d5eb9a3b8d557a369301660a252f550
- e041f63cab919d1af8614fb83b362cbff733bd06bc89d30cd04dcea3fac8651f
- f955035242ffa9bde3904e1c51b491ba81b76e16e912c5ed292efcaf55b04c1b
SHA-1
- db2321cd93e92d13269702deabd1e442bf4f4014
- 19f3d53a63dcfc293884006d779471d251c32570
- 831ebe472632005fe56c06d0fd03190bdf76dcf2
- 2ee3d7ce4ec3461026e910fdfcf9d18dd43eb380
- d9fd5b8bc91c27842731a8cb3ac43fd41502b32a
- f9becff777f42eb77db9cf3f5f77f1be7e3fa880
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Maintain cyber hygiene by updating your anti-virus software and implementing a patch management lifecycle.
- Maintain Offline Backups – In a ransomware attack, the adversary will often delete or encrypt backups if they have access to them. That’s why it’s important to keep offline (preferably off-site), encrypted backups of data and test them regularly.
- Emails from unknown senders should always be treated with caution.
- Never trust or open ” links and attachments received from unknown sources/senders.
- Patch and upgrade any platforms and software timely and make it into a standard security policy. Prioritize patching known exploited vulnerabilities and zero-days.
- Along with network and system hardening, code hardening should be implemented within the organization so that their websites and software are secure. Use testing tools to detect any vulnerabilities in the deployed codes.
- Enable antivirus and anti-malware software and update signature definitions in a timely manner. Using multi-layered protection is necessary to secure vulnerable assets








