

Rewterz Threat Alert – STOP (DJVU) Ransomware – Active IOCs
December 5, 2022
Rewterz Threat Advisory – CVE-2022-46366 – Apache Tapestry Vulnerability
December 5, 2022
Rewterz Threat Alert – STOP (DJVU) Ransomware – Active IOCs
December 5, 2022
Rewterz Threat Advisory – CVE-2022-46366 – Apache Tapestry Vulnerability
December 5, 2022Severity
High
Analysis Summary
Researchers have uncovered a large-scale phishing campaign aimed at the government, academic, foundation, and research sectors, with a focus on Australia, Japan, Taiwan, Myanmar, and the Philippines.
The campaign was observed from March 2022 to October 2022 and it is tied to an Advanced Persistent Threat (APT) group known as Earth Preta (also known as Mustang Panda and Bronze President). Earth Preta is well known for developing its own loaders and using them in conjunction with existing tools like PlugX and Cobalt Strike to compromise.
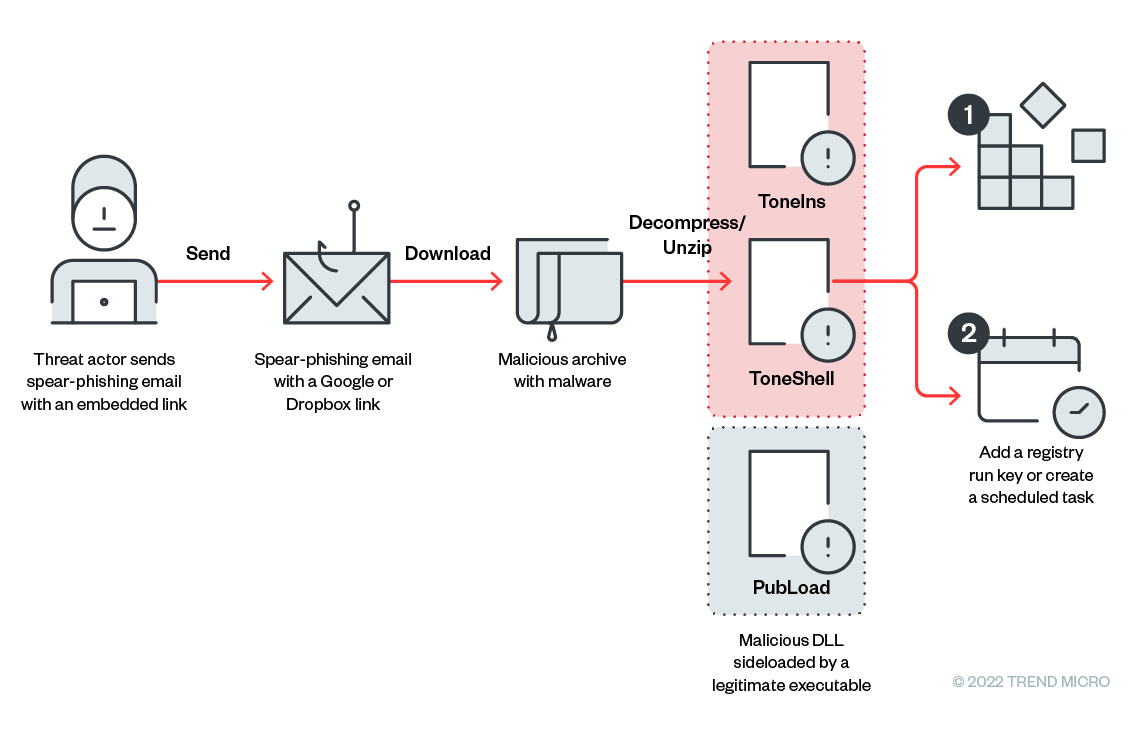
In the latest campaign, Earth Preta exploited fake Google accounts to spread malware via spear-phishing emails, the malware was initially stored in an archive file (such as a rar/zip/jar file) and distributed through Google Drive links. Throughout the campaign, researchers discovered new malware families utilized by the gangs (TONEINS and TONESHELL), including PUBLOAD, a previously disclosed malware.
PUBLOAD – A stager capable of downloading next-stage payload from its command and control (C&C) server. Cisco Talos initially revealed this in May 2022.
TONEINS – A first stage of malware that will install the TONESHELL backdoor and establishes the persistence for it.
TONESHELL – Mostly utilized backdoor in this campaign. It is a shellcode loader that uses a 32-byte key stored in memory to load and decode the backdoor shellcode.
Additionally, the threat actors employ a variety of techniques, including code obfuscation and unique exception handlers, to avoid discovery and analysis. Also, the senders of the spear-phishing emails and the owners of Google Drive URLs were discovered to be the same.
“we also believe that the attackers were able to conduct research and, potentially, prior breaches on the target organizations that allowed for familiarity, as indicated in the abbreviation of names from previously compromised accounts.”
At least three types of arrival vectors were observed in the latest campaign as the intrusions’ entry points, including over 30 lure archives around the world distributed via Google Drive links, Dropbox links, or other IP addresses hosting the files.
Researchers concluded from their analysis that after the gang has gained access to a victim’s networks, the sensitive data they have taken can be manipulated as entry points for the subsequent wave of intrusions.
They also share some mitigation plans including:
- Implement ongoing phishing awareness training for partners and staff.
- Always double-check the sender and subject of an email before opening it, especially if it has an unidentifiable sender or an ambiguous subject.
- Use a multi-layered protection solution to identify and block threats as far left in the malware infection chain as feasible.
Impact
- Information Theft
- Exposure To Sensitive Data
Indicators of Compromise
IP
202.53.148.26
98.142.251.29
202.58.105.38
103.15.28.208
MD5
a0e268be651237d247b00de5054d46ef
ae358c1915e794671a1d710d9359146d
19f22b4c9add7d91a18b2e3de76757a3
d1ec01ff605a64ab8c12e2f3ca2414a4
b9327186666fd00ae01bc776006b85ae
fcd6691fc59610a50740a170a8a5a76f
SHA-256
d8f54575aff075268200250b3ed4af1da894db2199432b7110605003c6afba4a
492fd69150d0cb6765e5201c144e26783b785242f4cf807d3425f8b8df060062
6478cbb620e1a6fe1fb7e9e15b37fdc10668aa5bf2c825b8cd65b129e6443e60
f2b10278aaa2dfc4344119551f624679b5a3d2501b39ec989b87690e0d357f42
dcefa4f651108d8371806403da4be9675797940faa580cc64f83116517c55ca7
ef3966d15af3665ee5126df394cefdf6f78fce77db7a70d5f35c19c234715035
SHA-1
cc7f6e53b4e43ec5e37b03eabd07bfbc5ecef180
cacc3eb2f415852f57579a69662744f75438e891
b857a32765a62f6d6af0ee4d02f4c9ca014571fd
cded487238543e875a901b503701611ad0ae9525
2f9f6752f4d22aba8750d7302a1980a7b257c000
396c9bf470fed61ed771561346b60678a6958fce
Remediation
- Block all threat indicators at your respective controls.
- Search for IOCs in your environment.
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.
- Implement ongoing phishing awareness training for partners and staff.
- Use a multi-layered protection solution to identify and block threats as far left in the malware infection chain as feasible.
- Enable antivirus and anti-malware software and update signature definitions in a timely manner. Using multi-layered protection is necessary to secure vulnerable assets








