

Rewterz Threat Advisory – CVE-2020-5870 – F5 BIG-IQ Centralized Management
April 28, 2020
Rewterz Threat Alert – Remote Workers Using Skype Targeted via Phishing
April 28, 2020
Rewterz Threat Advisory – CVE-2020-5870 – F5 BIG-IQ Centralized Management
April 28, 2020
Rewterz Threat Alert – Remote Workers Using Skype Targeted via Phishing
April 28, 2020Severity
High
Analysis Summary
In a new wave of phishing attacks, a new malware named ‘BazarBackdoor’, or internally by the malware developers as simply “backdoor”, is being installed that deploys a network-compromising toolkit for the threat actors. The malware has similarities to TrickBot trojan and developers of this malware are likely to be the ones behind Trickbot as well.
The initial attack starts with phishing campaigns that utilize a wide variety of lures such as customer complaints, COVID-19 themed payroll reports and employee termination lists that contain links to documents hosted on Google Docs.
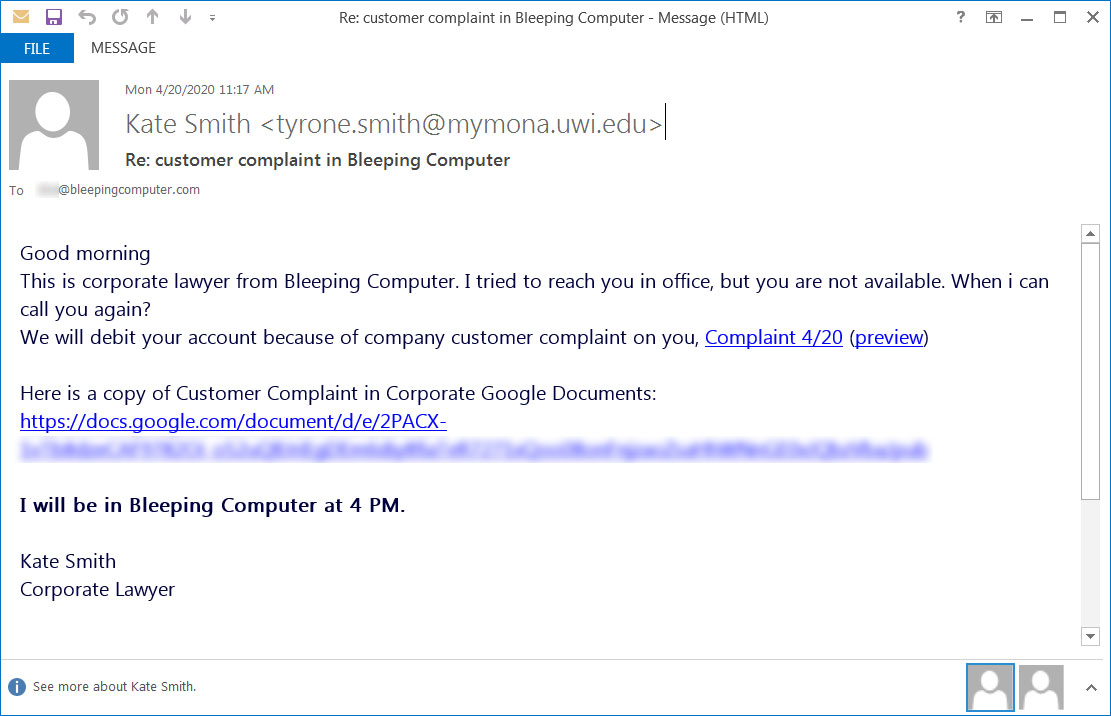
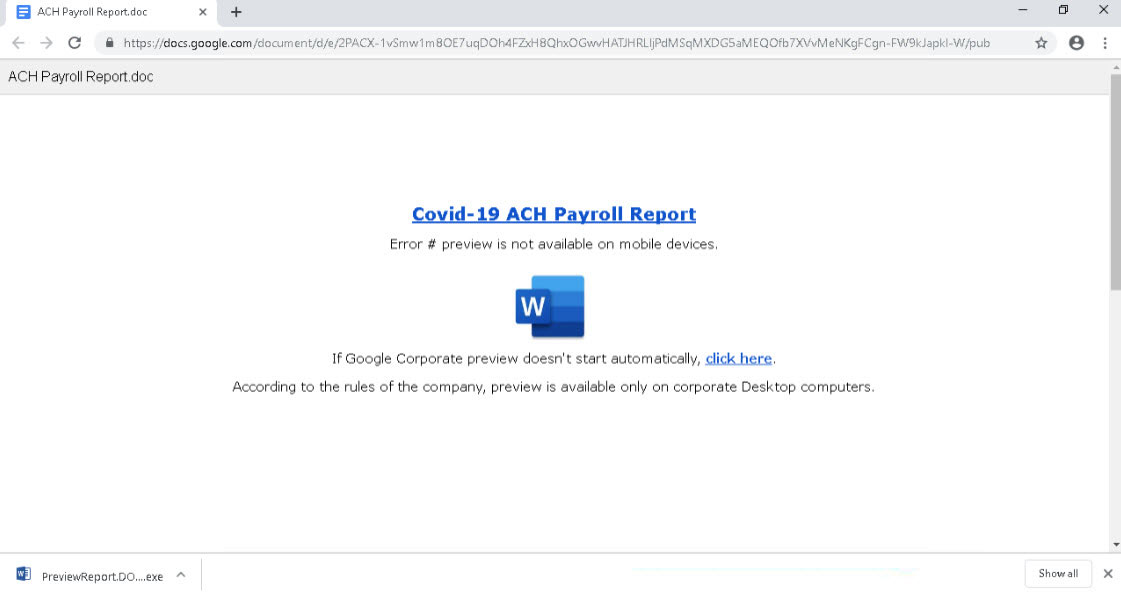
Threat actors have worked specifically on the landing page to ensure that the victim falls prey to the lure and a lot of styling and detailing has been done to make sure that the landing page looks authentic.
Fake payroll template
Fake customer complaint template
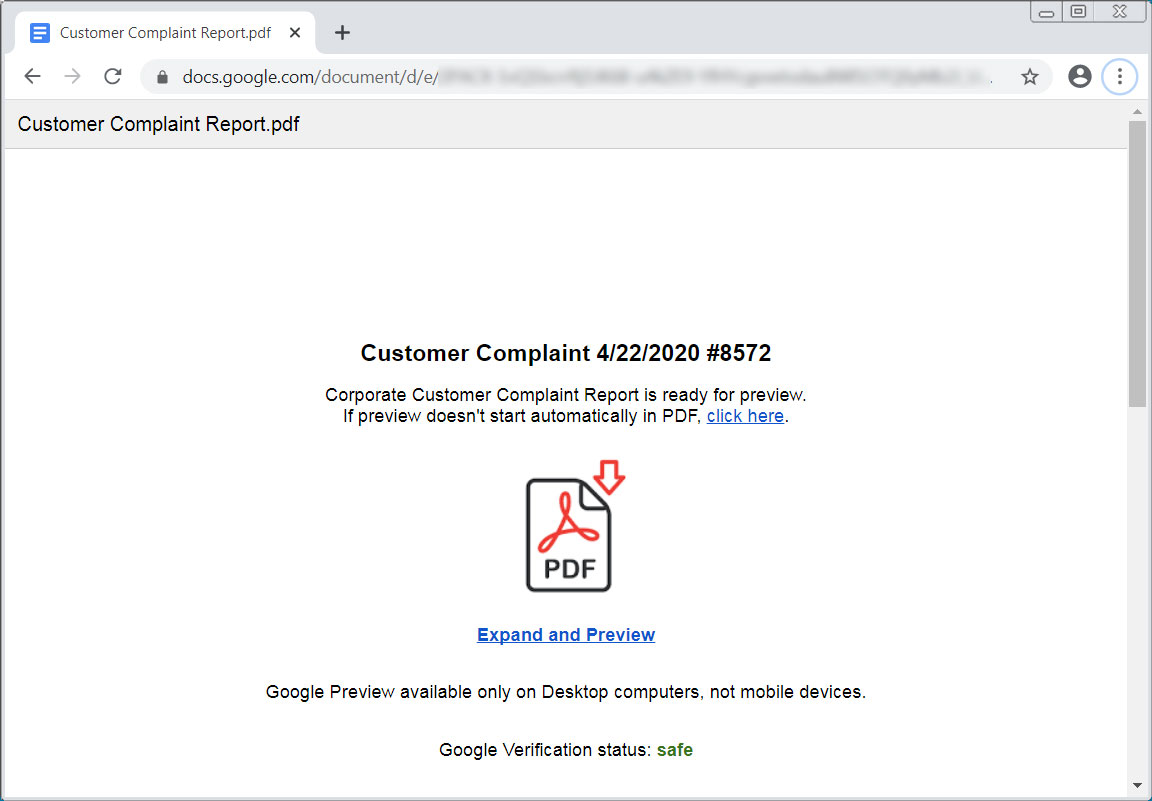
When the link is clicked, an executable will be downloaded instead that uses an icon and name associated with the icon shown on the landing page.
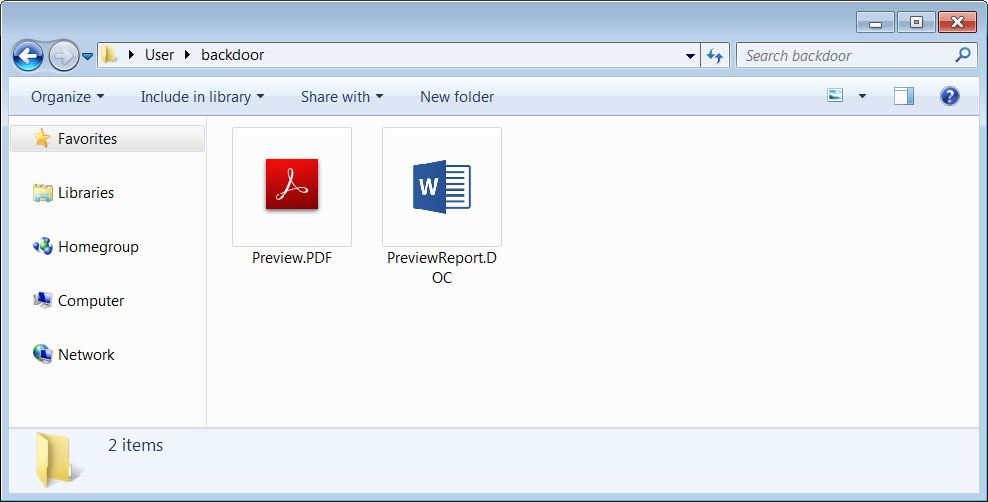
After a victim launches the downloaded file, the loader will sleep for a short period of time and then connect to command and control servers to check-in and download the backdoor payload. After the payload is downloaded, it will be filelessly injected into the C:\Windows\system32\svchost.exe process.
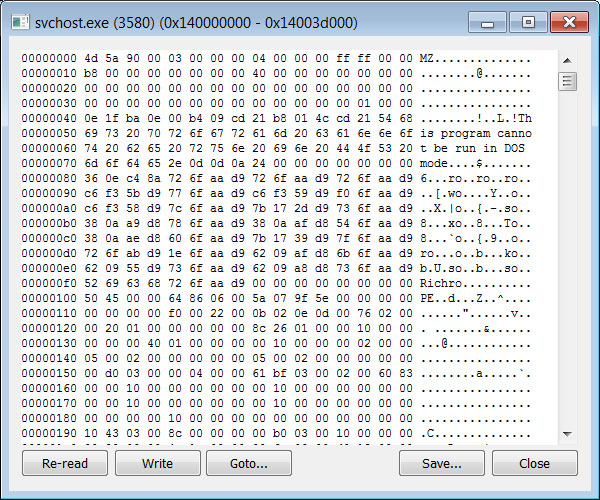
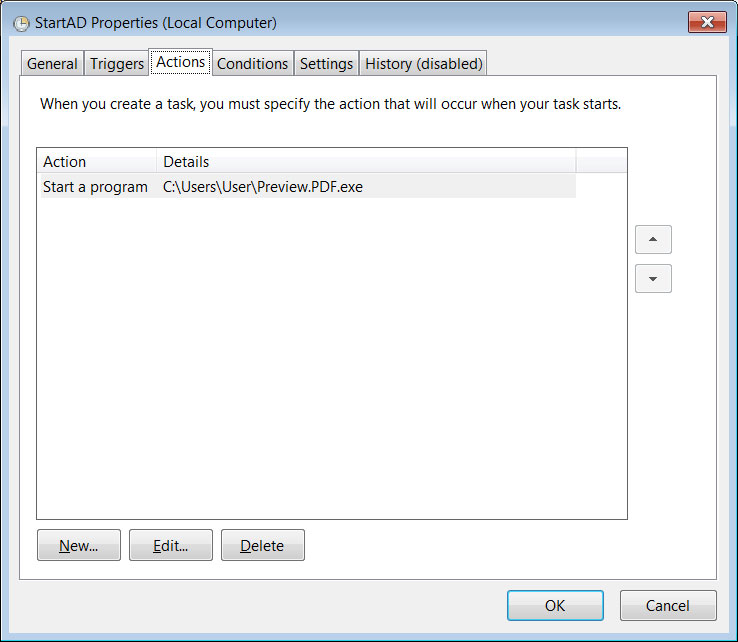
A scheduled task will also be configured to launch the loader when a user logs into Windows, which will allow new versions of the backdoor to be routinely downloaded and injected into the svchost.exe process.
Impact
- Gain access
- Exposure of sensitive data
Indicators of Compromise
MD5
- cdddcbc43905f8a1a12de465a8b4c5e5
- 8f290a2eacfdcfea4f5ca054ae25bc62
- b533f8b604b2cc99ce938d8303994e43
- 0e9f7f512a7eae62c091c7f0e2157d85
- 267b23b206cde7086607e2c4471a97c4
- 0708c3b1c48d71148cfd750e70511820
- df3db8d75d6c433c4c063d17f22e9b21
- 3fe91dbbcf0962895f768da6e40853ee
- 8b3215a899af33e3f6beb47a08787163
- 3078b0b4b1dc48d62019d6ccca9cf098
- e16a92cccc3700196337c9ad43210f38
- 9066f4c98967e27a1d32f01c47884785
- 07d1c4952795e804b87c7c9d536dc547
- c25965d25b5ccdc2f401188f27972c22
SHA-256
- 11b5adaefd04ffdaceb9539f95647b1f51aec2117d71ece061f15a2621f1ece9
- 5a888d05804d06190f7fc408bede9da0423678c8f6eca37ecce83791de4df83d
- 7c93d9175a38c23d44d76d9a883f7f3da1e244c2ab6c3ac9f29a9c9e20d20a5f
- ca8194e9a1232e508619269bdf9a9c71c4b76e7852d86ed18f02088229b0f7c7
- 05abd7f33de873e9630f9e4f02dbd0cbc16dd254f305fc8f636dafba02a549b3
- 4ee0857d475e67945af2c5e04be4dec3d6d3eb7c78700f007a7ff6f8c14d4cb3
- b10dcec77e00b1f9b1f2e8e327a536987ca84bcb6b0c7327c292f87ed603837d
- e90ccb9d51a930f69b78aa0d2612c4af2741311088b9eb7731857579feef89c3
- 6cbf7795618fb5472c5277000d1c1de92b77724d77873b88af3819e431251f00
- 2f0f0956628d7787c62f892e1bd9edda8b4c478cf8f1e65851052c7ad493dc28
- 94dcaa51e792d1fa266cae508c2c62a2ca45b94e2fdfbca7ea126b6cd7bc5b21
- 37d713860d529cbe4eab958419ffd7ebb3dc53bb6909f8bd360adaa84700faf2
- 210c51aab6fc6c52326ece9dbd3ddab5f58e98432ef70c46936672c79542fbd0
- 58880777c4b2d9d1ac7cd145c6704a936a54510eaaa7ae61ce8ca8390e355006
- 0f94b77892f22d0a0e7095b985f30b5edbe17ab5b8d41f798ef0c708709636f4
- 3ee36a9401a4df622be5dc12ac9b9bcf1d607c8d394b12e863ec17776c2e0fe7
- c55f8979995df82555d66f6b197b0fbcb8fe30b431ff9760deae6927a584b9e3
- 35b3fe2331a4a7d83d203e75ece5189b7d6d06af4abac8906348c0720b6278a4
SHA1
- 3884ccf43010733ead38ddea11f249b33f2f1609
- 66f66cd650c9a08d2433c92d0fb78b22cfc279be
- c47ba9a3bd09ac601e8766acf7add73710743984
- 76e1b95f5fb6251bb79de78ae5169044885e07e3
- 15d070be7838e73a3862d267cb9aff0f0b77b715
- 9c14c7958a58ad5916c91a5ea42bc453db73b947
- b19620bfa0a6311cdeac1a63aaf477d5b3df7730
- 81982119280c2a435f13b09a2995d06f422ca013
- 0dd83eb2235f1775b981ed992f121367f723b23c
- fb5a481431a0bfc6785cb101e2eefec1840d1d16
- 53ee27c7893574d496a0b512363e690ac9f6d7ba
- 6b14b1634706ddd60af62dd276645727c7762094
- 68d8e4654662c4e83c4c101e70eb132a1d879e0e
- 078f815f9b4e3dc108dedc3a00eaa666058f035e
URL
- https[:]//allacestech[.]com/PreviewReport[.]DOC[.]exe
- https[:]//www[.]ruths-brownies[.]com/PreviewReport[.]DOC[.]exe
- http[:]//www[.]afboxmarket[.]com/CompanyReportList[.]exe
- http[:]//invent-uae[.]com/Document_Preview[.]exe
- https[:]//51[.]81[.]113[.]26/api/v88
- https[:]//daralsaqi[.]com/PreviewReport[.]DOC[.]exe
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.








