

Rewterz Threat Alert – Weaponized Legitimate Open-Source Software
November 27, 2020
Rewterz Threat Alert – Nanocore – IoCs
November 27, 2020
Rewterz Threat Alert – Weaponized Legitimate Open-Source Software
November 27, 2020
Rewterz Threat Alert – Nanocore – IoCs
November 27, 2020Severity
High
Analysis Summary
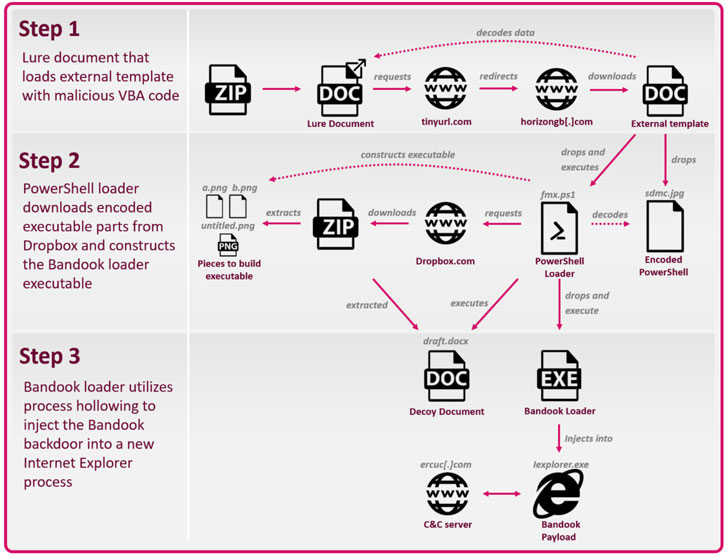
A new digitally-signed Bandook malware sample is spotted in the wild, aiming at high-value targets across multiple sectors, including government, financial, energy, food industry, healthcare, education, IT, and legal institutions. Victims have been spotted covering a diverse and large geographical area. reportedly, a cyberespionage group with suspected ties to the Kazakh and Lebanese governments has unleashed a new wave of attacks against a multitude of industries with a retooled version of a 13-year-old backdoor Trojan. The infection chain is a three-stage process that begins with a lure Microsoft Word document (e.g. “Certified documents.docx”) delivered inside a ZIP file that, when opened, downloads malicious macros, which subsequently proceeds to drop and execute a second-stage PowerShell script encrypted inside the original Word document.
Impact
- Unauthorized Remote Access
- Code Execution
- Information Theft
Indicators of Compromise
Domain Name
- pronews[.]icu
- ntsclouds[.]com
- vsimperial[.]com
- mxtms[.]com
- nopejohn[.]com
- horizongb[.]com
- olex[.]live
- styleco[.]me
- raysdoor[.]com
- mainsrv[.]top
- idcmht[.]com
- vdscloud[.]net
- ewsdocs[.]com
- jtoolbox[.]org
- htname[.]info
- ercuc[.]com
- p2020[.]xyz
- tancredis[.]com
- 2ndprog[.]monster
- branchesv[.]com
Filename
- Malaysia Shipment[.]docx
- Jakarta Shipment[.]docx
- malta containers[.]docx
- Certified documents[.]docx
- Notarized Documents[.]docx
- bank statement[.]docx
- passport and documents[.]docx
- Case Draft[.]docx
- documents scan[.]docx
Hostname
- ec2[.]mbcde[.]net
- s2[.]fikofiko[.]top
- s1[.]megawoc[.]com
- d2[.]p2020[.]club
- d1[.]p2020[.]club
- s2[.]megawoc[.]com
- s3[.]megawoc[.]com
- s1[.]fikofiko[.]top
- s3[.]fikofiko[.]top
MD5
- 70ff19341dee7973ea6dd8e15c6ba86f
- 27f8d8bbbeeda5fc439ee18d9d4da343
- f037f3961f7d9fe1eb7afa889b556cb1
- d22b31848b6f17efc87d538dede2f2a7
- b9b8d6f46ff3a9058ffe4b304604b4e7
- 96f09c5c56f59c733d1a9b01fea0cfb4
- 17fe9611ea566887b3ef42284f96de03
- 83311c960609418d5f0a5160324ceb1d
- 44584c8d010242fddb44afe5ce860872
- d1600f45005aa8b8fcbb446f34f7b9f5
- 4d7e67ed02713c789336f8804231b1ca
- 4e9e12c98cfbc5f3aa3c1345bd063fa0
- 045ce6679ed4086e2ded58470e24c15a
- 7c15ee5b9a12dacaace8fb62271f12f1
- 3f310215a70d748f9335c767e61a2ab4
- 7ef261c151519e66ec369c63e4b1aed4
- 0475771b8bc3efc28b1834f3add608f3
- b5138c77983dba10c4976c411161bbf9
- 9bcf889b14968c61df95961a161719ba
- 07111aff7afc052a81f267ea2e83dcef
- 07776b2dd00bcd0be1c7713c37d41120
- 53b7bdd75776f342bf5f5395d4c46520
- eb402e8dd2cae58476acc8e697ee7171
- a6501c62b3a6ffa8d028a88138fe509f
- 1a3889ded73044f8ba0a00c2f089a3bd
- bca04d74261fedfbd191ffd5e7cf6214
- d6e524514e0d112015c841b62377d648
- cfea49c577ef865de659d5b8025db3f9
- 28ad9ace11919b57bf540e2b9debf8dd
- 6effed1b1bb5e9ed6aafacb075c1d4e2
- 5a3f7c46748791494e29383d1f58a908
- 573c7dbf4d3aed421bff58df770610fe
- 54ad403349831b175a98a429f818f02a
SHA-256
- 9a0ee2430f7c77942d544dad6787ca8a94470f6555f1cb08baa9d099c92f8447
- 74feaf3aa116a88ef3b10453e77feadefbe4e53dd7a71dd3b8309cc9d76cdec9
- 6af6fe3eafd4cf2c82738d45a6a95577d970f3fbbe094afd24d1d4a0bb5ad1b4
- aa868d007c4dfd825104faafb3798b9ab745b29794a57365bef41ec3f6019eea
- 9a19522b23acfc6705e4fac65640527a8adbbc9719dab436f28101b6cbc140c6
- 408c11caf548048732ac21e88a54e80d47a05b9619c1c16b65fa850e0172f428
- 766917fe9b543bf218bd824d55967d63f94b28456f1d4919bc990d8262dc608d
- 5900abb869c61928f0ef931d6f9d8b62183b2bab9a69b0ef886551005d6c9622
- a9a8b0aa5f137e7353db62dc1609da3c709ca30287a5605c73aafaf4968d1e8d
- 3fda0a5da313886b0339eee65c69c779ed620b303ba079ee0864ca4a1496b0b4
- 9de287f9af63f02c51c69d9c8480fee2bd4d4bd3c818f2ba81324b1f8ce495c0
- 1ad83e9d06428dd87203ab8fcc6142014a9c05f3eb9afd61347834f39082d72a
- 27c6341554a04bdc792ffbc5cda26511cbcfcc66334fb6ebbc24a14969b4e498
- 8cb1f713761a6b31c9c25dd2c7ae11e575a634c9f052cfd598ada35a61783230
- 1b0d2d096c5f7fff02a5a4ce623b71b862f63e306a0760722f710c425b4e16ec
- add9f9dca97c3b6d52efe7d48ecd3d349a70411eaa3d4aeff6e6215b77f42b90
- 2ee74ae5b202c8aab288ca167c630e9ee3569240958e984474b960cd560bbe95
- 6287fc617ff6881169990e6b877c16d8ca3c199f7e453241a0b18a7907c67ab0
- 306238a63896fa8b79b4c9a6d25fd906bb9e4919bc698608ab970677d15b0694
- ea4792353e0f97968e7c69ffba81c144f22f54382af4e61a1347edd0ae15830f
- 072c103759968253b7b25837b43eec546c625ae9c04edd52321d848cf6078b87
- 034d8ec8d510033c387bb87cac35d240b7b8daa3b5167732118c755c5e6c1d48
- aed7ab5d0de01c3724c917c034e26a5e9eed3f7fbf4082b024576a41725d66cf
- d217288a046e2739159d0081608a44c2e79d41de12c57ebe88a8591693fa15d5
- d4cf5c5c60e972cc19782d1f37ec9d47dd1e81cdf481b64dab62f96bac846bb4
- 97ea91fb673f4994da491433751c4fca011993ba10191f09c70ca6c8d2b4f944
- ba153e449ee926c019b548997c32d0579b9c6f350b1590a025d5d9a216ddbffd
- ce8ad96819c814dd1735e621639a8845ae7132375879cc5b5d5f6877cb909a68
- 40cc5933e608f7a2a5c13af1066257c9e41528bb85e434e2bc3d1f4802dec24d
- 0750c7cdc538d79d9ffed0d37f5d9a083902b49ec02d75ee88028db9f3668b59
- 41ccf6de0d51bd29d35be12ae24f04b2f88ec2b202b239424f90c666d25473e8
- 66c86f29afb1152aad8e426ebb6569ad03ce7b69ea3c8a5cc40011c2a3ab973b
- 06ed3daccfbb30c68a33583a761fc20cc3e21adb8dd64a42d922e6da2a01c0dd
SHA1
- 816b2442c17585396b73b54fbc87be624d55276c
- d6b69cb3689341997d93b03fbd4499fe60f29b35
- 7e9fcbd7f31c3a4ddb3221351e8d04ecdce69474
- a8f2b1f1a1200d25d751b5559a31c034781ea33e
- 47b8d74725f353dad8177c478ffa77d424e9a34e
- a31296f1eed15262f070abb3e89acf1a3917746a
- 57c9411b444ce4fddf6ddf210dd7dfd008c156ac
- 8790c9c1ffdf7ce7d7c1a0825a73ef75958fd9c5
- 99e724a6941c65eed20ac13c4940e325fd323082
- 788489ecd0e43f74c7d8df841bee8367cba2164d
- b1604a158cdd24182d8d4198fb17f4d348b92601
- 118633bbe46520c65529c0cd1d6eb52f810f6327
- c4d7332f09c7e917d5dd56930854e735cfce45fa
- 49a8149054440e33a6228b42f731e2f8035049e5
- 03508cbeec86346d6658da8c9d34638c57dad920
- aad7ec556d8d6e4333552d23588734d339373ab8
- 1e45d9c3ff9bb7e2ed236384694237dcd956de2b
- 9d0deca8dbdf25bdb9208772f861c28aa5a4e95f
- 9b47ab36a00d83c119620318e4924ce50cec2512
- cf96410d1cde40aaebfe32f26354282a7773abaf
- 9e33cbc25a8ad9987f88d5e1d181098142579f54
- e98700d562edb0ed29e429d0263ec448daf8a5f2
- 500813f95615b25f622e82e6c79431d7f4928bc4
- 424e3570f36fdb541e9b49f9d6824949ccf96ea6
- 7f534338d1399221bb2134d917a1e3eef8b309e5
- e78721fd283b0093fb0556167e1b38b81ed0c7bb
- 8971b585f8bf7d9f086d97d2d640ed4ce7f6b178
- 154c16ecfa56b71ce7b6f3fca4be4e0820e34665
- 55d1a679ae7e812d5c91ef78bec4095a2048427c
- 8c4d5618c3ab2d2411ede54f443560891a78986b
- b0d64b13407da0c6db1aced2d9e110802c05a6d3
- 9087c24b181d58bb57d02a1ce19f8d17d63476b4
- f6b1b3fc532b516366de6b3452b5c23441386e17
Remediation
- Block the threat indicators at respective controls.
- Do not download files attached in untrusted emails sent by unknown senders.








