

Rewterz Threat Alert – GandCrab Ransomware – Active IOCs
January 20, 2023
Rewterz Threat Alert – CrySIS aka Dharma Ransomware – Active IOCs
January 20, 2023
Rewterz Threat Alert – GandCrab Ransomware – Active IOCs
January 20, 2023
Rewterz Threat Alert – CrySIS aka Dharma Ransomware – Active IOCs
January 20, 2023Severity
High
Analysis Summary
Donot APT group is a cybercrime group, known for conducting cyber espionage and intellectual property theft against government and military organizations, as well as companies in the aerospace, defense, and high-tech industries. The group has been active since at least 2016 and is known for using a variety of tactics, techniques, and procedures (TTPs) to conduct their attacks.
One of the key TTPs used by the Donot APT group is the use of custom-developed malware. The group has been known to use a variety of malware, including remote access trojans (RATs), keyloggers, and data exfiltration tools. They also use phishing and spear-phishing tactics to trick victims into giving them access to their systems.
The group is known to use a variety of infrastructure to conduct their attacks, including compromised servers and domain names. They also use a range of encryption and obfuscation techniques to hide their activities.
It is important for organizations to be aware of the threat posed by the Donot APT group and to take steps to protect themselves from their attacks. This includes implementing strong security controls, such as firewalls, intrusion detection and prevention systems, and endpoint security solutions, as well as educating employees about the risks of phishing and spear-phishing. Additionally, organizations should also have incident response plans in place to quickly and effectively respond to a security incident.
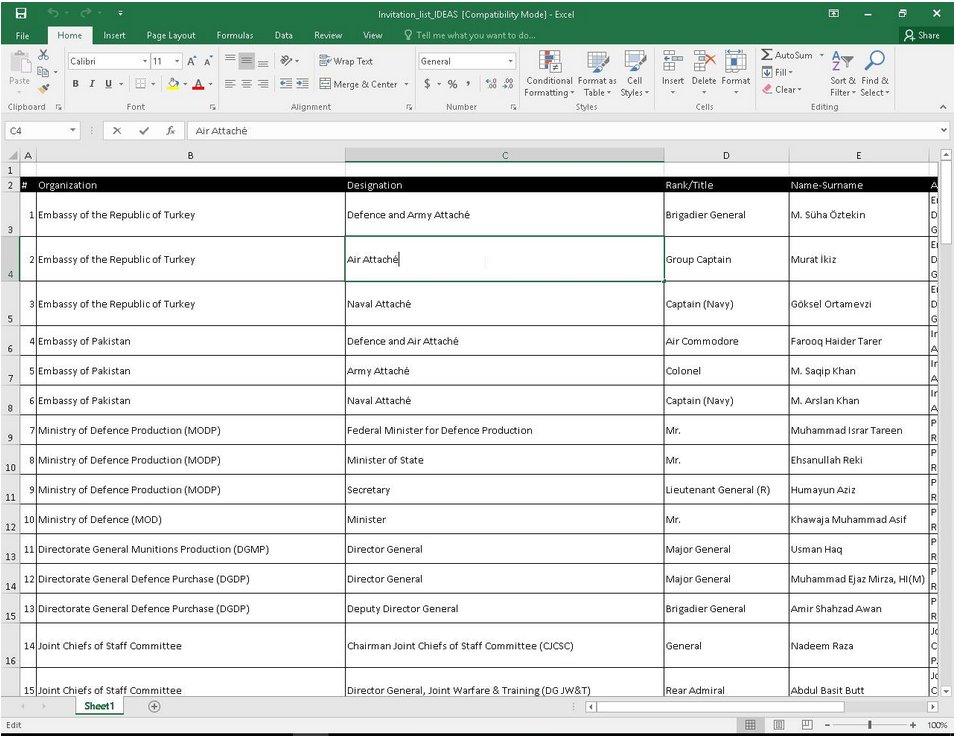
The recent malicious campaign includes the invitation list of IDEAS named Invitation_list_IDEAS.xls.
Impact
- Information Theft and Espionage
Indicators of Compromise
MD5
- 7f94ba673f2ba0d469fde4c3d40d8d4c
- 30a10652cd20bf1bbac0b9f5b483a3d7
- d45897fa6dd8e609226a19712a016884
SHA-256
- 9de6b542a323b5198dbf472d612313f0cc236e9156e78c583da055d0ce7a29f7
- b59913878de7c9b10a2c4dfc4f9d1634b95510b4efafb546c46ef076f917911c
- d1b828440268685f40a1bb45dda46748d0713a2365e669806d3b6b14f370bb3f
SHA-1
- 9b114c2de8ec98e2ef2e7e431358b74a8952d4cd
- 5f039f1ef52877744f9c91908aaeaf0db3653419
- 4bf8a688d2cf9b99c6310d8dae9074c1baaa1938
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Do not download documents attached in emails from unknown sources and strictly refrain from enabling macros when the source isn’t reliable.
- Enable antivirus and anti-malware software and update signature definitions in a timely manner. Using multi-layered protection is necessary to secure vulnerable assets
- Along with network and system hardening, code hardening should be implemented within the organization so that their websites and software are secure. Use testing tools to detect any vulnerabilities in the deployed codes.








