

Rewterz Threat Advisory – CVE-2022-41207 – SAP Biller Direct Vulnerability
November 10, 2022
Rewterz Threat Advisory – CVE-2022-41205 – SAP GUI for Windows Vulnerability
November 10, 2022
Rewterz Threat Advisory – CVE-2022-41207 – SAP Biller Direct Vulnerability
November 10, 2022
Rewterz Threat Advisory – CVE-2022-41205 – SAP GUI for Windows Vulnerability
November 10, 2022Severity
High
Analysis Summary
APT-C-23 (aka AridViper) is an Arabic-speaking Advanced Persistent Threat group working for Hamas. The threat group has been previously known to target Middle-Eastern countries but has been recently observed targeting Israeli officials and individuals. Their espionage campaign aims to steal credentials and sensitive information from the victim’s PC and mobile devices. Their most active targets are Israeli individuals working for the military, emergency services, and any law enforcement agencies. Their primary infection method is social engineering, through which they deliver trojanized messages via facebook or other social media applications. The group has been using an upgraded malware called “Barb(ie) Downloader” and “BarbWire Backdoor” and an android implant named VolatileVenom.
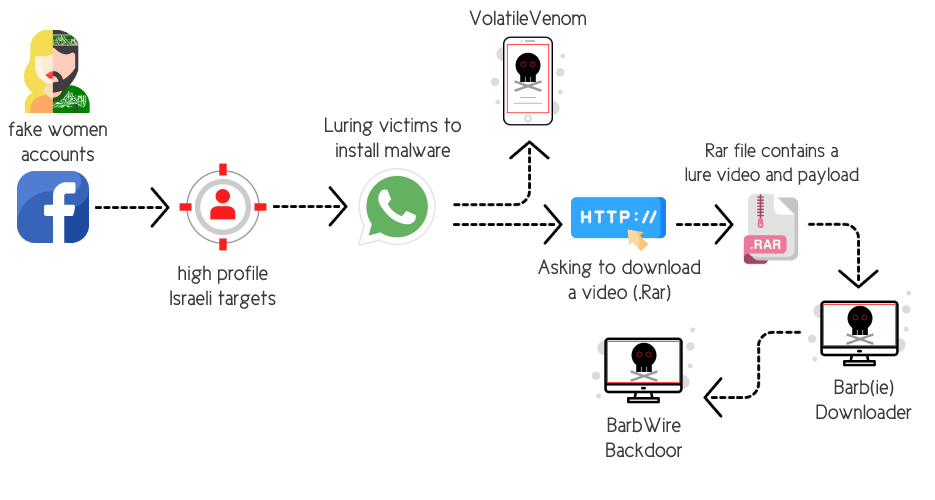
The campaign observed in October contains a file disguised as a word document, named ‘The Ministry of State for Wall and Settlement Affairs established by the Palestinian government.xz’
Impact
- Information Theft and Espionage
Indicators of Compromise
Domain Name
zakaria-chotzen[.]info
MD5
- 116967e277b8e095697eff6741fad165
SHA-256
- cb9fb42bfcae30b849fcc210d1ac4b39a12e32c6dc9d8523fcf9883632d7135e
SHA-1
- 60480323f0e6efa3ec08282650106820b1f35d2f
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on links/attachments sent by unknown senders.
- Search for IOCs in your environment








