

Rewterz Threat Alert – China-Linked Hackers Behind Barracuda ESG Zero-Day Attacks – Active IOCs
June 16, 2023
Rewterz Threat Alert – Unveiling the Attacks by White Elephant Group: Exploiting BADNEWS and Remcos Commercial Trojans – Active IOCs
June 17, 2023
Rewterz Threat Alert – China-Linked Hackers Behind Barracuda ESG Zero-Day Attacks – Active IOCs
June 16, 2023
Rewterz Threat Alert – Unveiling the Attacks by White Elephant Group: Exploiting BADNEWS and Remcos Commercial Trojans – Active IOCs
June 17, 2023Severity
High
Analysis Summary
NIFT, the National Institutional Facilitation Technologies, claimed to have experienced a severe cyber attack resulting in the complete shutdown of both their data centers in Karachi and Islamabad. The attack had a significant impact on their operations, prompting NIFT to conduct a thorough analysis of the server and assess the damage caused by the attack. They are currently reviewing the data in an effort to recover the compromised information.
Despite the attack, NIFT managed to complete the processing of outward clearing transactions from the previous day and updated the inward clearing bags for the current day. However, they have decided to temporarily halt the clearing process for today’s physical cheques. This cautious measure is in place until they can consolidate the situation and successfully recover the data and images affected by the cyber attack.
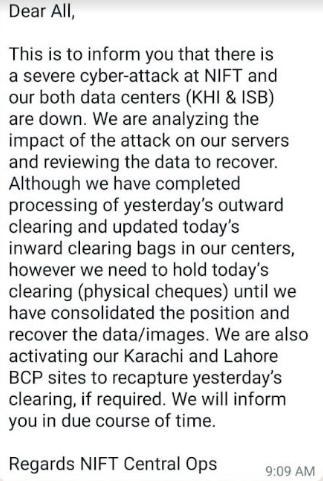
Snapshot taken from external source:
To ensure continuity of operations and minimize disruption to their customers, NIFT is taking proactive steps. They are activating their Business Continuity Plan (BCP) sites in Karachi and Lahore, which will assist in recapturing the clearing data from the previous day if deemed necessary.
The exact attribution and motivation behind the cyber attack on NIFT Pakistan remain unclear at this stage. Further investigation is required to determine the responsible party and their objectives, whether they are financially motivated, state-sponsored, or driven by other malicious intent.
NIFT is actively engaged in analyzing the impact of the cyber attack on their server infrastructure. They are conducting a thorough review of the servers to determine the extent of the breach and assess the potential loss of data and images. This analysis is critical to understanding the scope of the attack and initiating appropriate remediation measures.
In terms of communication, NIFT acknowledges the importance of keeping stakeholders informed. They have assured stakeholders that they will provide updates regarding the recovery process, resumption of clearing operations, and the status of data recovery. Timely and transparent communication will help manage expectations and maintain trust among customers, employees, and other relevant parties.
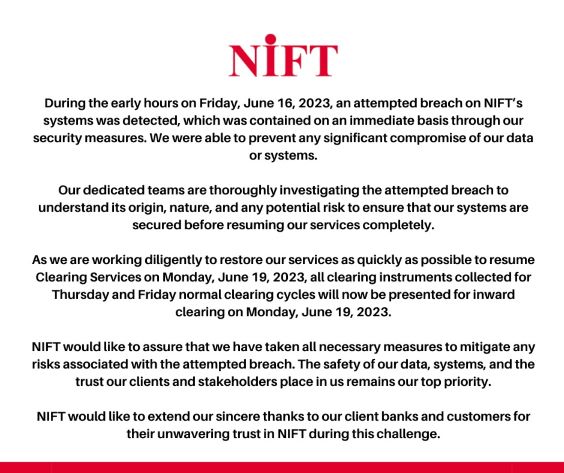
Moreover, The National Institutional Facilitation Technologies (NIFT) reported an attempted breach on its systems, which was detected and contained immediately through their security measures. The organization reassured that there was no significant compromise of data or systems. NIFT’s dedicated teams are investigating the breach to determine its origin, nature, and potential risks. They are working to restore services promptly and plan to resume Clearing Services on Monday, June 19, 2023. All clearing instruments from Thursday and Friday will be processed on that day. NIFT emphasized that they have taken necessary measures to mitigate risks and prioritize the safety of data, systems, and the trust of their clients and stakeholders. They expressed gratitude to their client banks and customers for their unwavering trust during this incident.
Note: This report also includes Indicators Of Compromise (IOCs) provided by Regulatory Authority.
Impact
- Operational Disruption
- Clearing Process Delay
- Reputational Damage
Indicators of Compromise
Domain Name
- fashionmasala.pk
- agspharmas.com
IP
- 169.228.66.212
- 45.146.252.37
- 202.63.219.133
- 202.63.219.134
- 203.101.170.4
- 66.45.251.115
- 66.45.251.120
MD5
- 5bc0c1d8e14b6bc1cda573c43a5114e0
SHA-256
- c008739106b0929f9e550ce1b97c5cfd9232e7cf9513dca30982cd7ac1602733
SHA-1
- 106e4f96c989cd8bc9f8d8b00f4f0eb468946daa
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Do not download documents attached in emails from unknown sources and strictly refrain from enabling macros when the source isn’t reliable.
- Enable antivirus and anti-malware software and update signature definitions in a timely manner. Using multi-layered protection is necessary to secure vulnerable assets
- Along with network and system hardening, code hardening should be implemented within the organization so that their websites and software are secure. Use testing tools to detect any vulnerabilities in the deployed codes.








