

Rewterz Threat Update – Update on Active Exploitation of Critical VMware Vulnerability
June 21, 2023
Rewterz Threat Alert – Multiple Apple iOS and iPadOS Vulnerabilities
June 21, 2023
Rewterz Threat Update – Update on Active Exploitation of Critical VMware Vulnerability
June 21, 2023
Rewterz Threat Alert – Multiple Apple iOS and iPadOS Vulnerabilities
June 21, 2023Severity
High
Analysis Summary
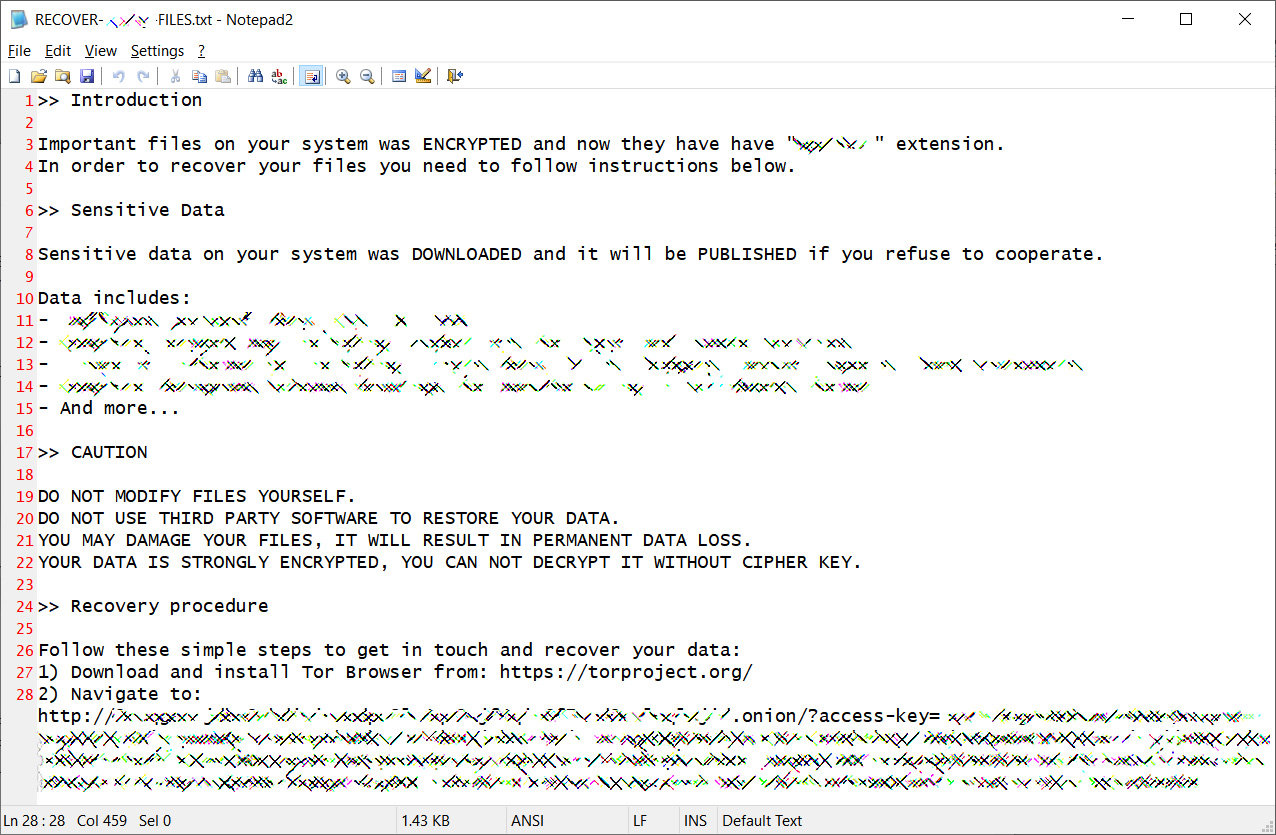
BlackCat – aka AlphaVM & AlphaV – is a Ransomware family that is deployed as a part of a Ransomware as a Service (RaaS). It is written in the Rust programming language and can run on Windows, Linux-based operating systems (Debian, Ubuntu, ReadyNAS, Synology), and VMWare ESXi.
This ransomware first appeared in November 2021. The majority of the group’s victims have been in the United States, although BlackCat and its associates have also targeted organizations in Europe, the Philippines, and other regions. Construction and engineering, retail, transportation, commercial services, insurance, machinery, professional services, telecommunication, auto components, and medicines are among the targeted sectors of BlackCat ransomware. This ransomware can be set to encrypt files using either the AES or ChaCha20 algorithms. It can destroy volume shadow copies, terminate programs and services, and stop virtual machines on ESXi servers to maximize the quantity of ransomed data.
As with other ransomware families, BlackCat encrypts the victim’s files and demands payment in exchange for the decryption key. It is important for individuals and organizations to take proactive steps to protect themselves against ransomware, such as regularly backing up important files, implementing strong passwords and multi-factor authentication, and staying up-to-date with software patches and security updates.
Note: This report also includes Indicators Of Compromise (IOCs) provided by Regulatory Authority.
Impact
- File Encryption
- Reputational Damage
- Operational Disruption
Indicators of Compromise
IP
- 89.44.9.243
- 142.234.157.246
- 45.134.20.66
- 185.220.102.253
- 37.120.238.58
- 152.89.247.207
- 198.144.121.93
- 89.163.252.230
- 45.153.160.140
- 23.106.223.97
- 139.60.161.161
- 146.0.77.15
- 94.232.41.155
MD5
- 861738dd15eb7fb50568f0e39a69e107
- 20855475d20d252dda21287264a6d860
- 91625f7f5d590534949ebe08cc728380
- a3cb3b02a683275f7e0a0f8a9a5c9e07
- 173c4085c23080d9fb19280cc507d28d
- 817f4bf0b4d0fc327fdfc21efacddaee
- 9f60dd752e7692a2f5c758de4eab3e6f
- 09bc47d7bc5e40d40d9729cec5e39d73
- f5ef5142f044b94ac5010fd883c09aa7
- 84e3b5fe3863d25bb72e25b10760e861
- 9f2309285e8a8471fce7330fcade8619
- 6c6c46bdac6713c94debbd454d34efd9
- e7ee8ea6fb7530d1d904cdb2d9745899
- 815bb1b0c5f0f35f064c55a1b640fca5
- 6c2874169fdfb30846fe7ffe34635bdb
SHA-256
- 7d8671c91a02bfbff8b89a76501b9be017a66a8bba624ed4fe2c7f81b9380ac9
- 1b90e6f959db883fb4a036dac06242be724a7637708058e2c439e2250222d6d1
- 3c300726a6cdd8a39230f0775ea726c2d42838ac7ff53bfdd7c58d28df4182d5
- 31eb1de7e840a342fd468e558e5ab627bcb4c542a8fe01aec4d5ba01d539a0fc
- 731adcf2d7fb61a8335e23dbee2436249e5d5753977ec465754c6b699e9bf161
- f837f1cd60e9941aa60f7be50a8f2aaaac380f560db8ee001408f35c1b7a97cb
- 80dd44226f60ba5403745ba9d18490eb8ca12dbc9be0a317dd2b692ec041da28
SHA-1
- e96950f2b7a9c1cdd542ab5bce025303a0b032f9
- 04589618b18ed1e073768bd5669127aaf916c4f1
- bf1b0ab5a2c49bde5b5dbe828df3e69af5d724c2
- d241df7b9d2ec0b8194751cd5ce153e27cc40fa4
- a186c08d3d10885ebb129b1a0d8ea0da056fc362
- 8917af3878fa49fe4ec930230b881ff0ae8d19c9
- fce13da5592e9e120777d82d27e06ed2b44918cf
- 1b2a30776df64fbd7299bd588e21573891dcecbe
Remediation
- Block all threat indicators at your respective controls. Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Implement SOC-level monitoring for the mentioned IP addresses/domains.
- Conduct a thorough cyber investigation if any system/device is found communicating with the aforementioned IPs/URLs.
- Ensure that the connected systems follow established banking security practices or information security policies. This includes implementing strong access controls, regular patch management, encryption mechanisms, and secure configurations to protect sensitive data.
- Endpoint Detection and Response (EDR) and Security Information and Event Management (SIEM) systems should be in place to centralize log management, event correlation, and analysis. Verify that SIEM solutions are integrated with connected systems, collecting relevant security logs, and generating alerts for suspicious activities or potential security incidents.
- If VPN connections are utilized to establish end-to-end connectivity, ensure that the VPN infrastructure is properly configured, using strong encryption protocols, and enforcing secure authentication mechanisms. Regularly review and update VPN configurations, monitor VPN logs for any suspicious activities, and promptly address any identified vulnerabilities.
- Ensure that robust data backup mechanisms are in place, regularly tested, and securely stored. Implement a thorough data recovery strategy to minimize potential data loss and expedite the restoration process.
- Conduct a comprehensive review of existing cybersecurity measures, including network security, access controls, and intrusion detection systems. Enhance these defenses to prevent future cyber attacks and fortify the organization’s overall security posture.
- Develop and implement an effective incident communication plan to keep stakeholders, including customers, employees, and relevant authorities, informed about the progress of recovery efforts, expected timelines, and any necessary precautions to be taken.








