

Rewterz Threat Alert – Hacker-for-hire Mercenary Group CostaRicto Launches Cyber Attacks
November 13, 2020
Rewterz Threat Alert – Trickbot IOCs
November 16, 2020
Rewterz Threat Alert – Hacker-for-hire Mercenary Group CostaRicto Launches Cyber Attacks
November 13, 2020
Rewterz Threat Alert – Trickbot IOCs
November 16, 2020Severity
High
Analysis Summary
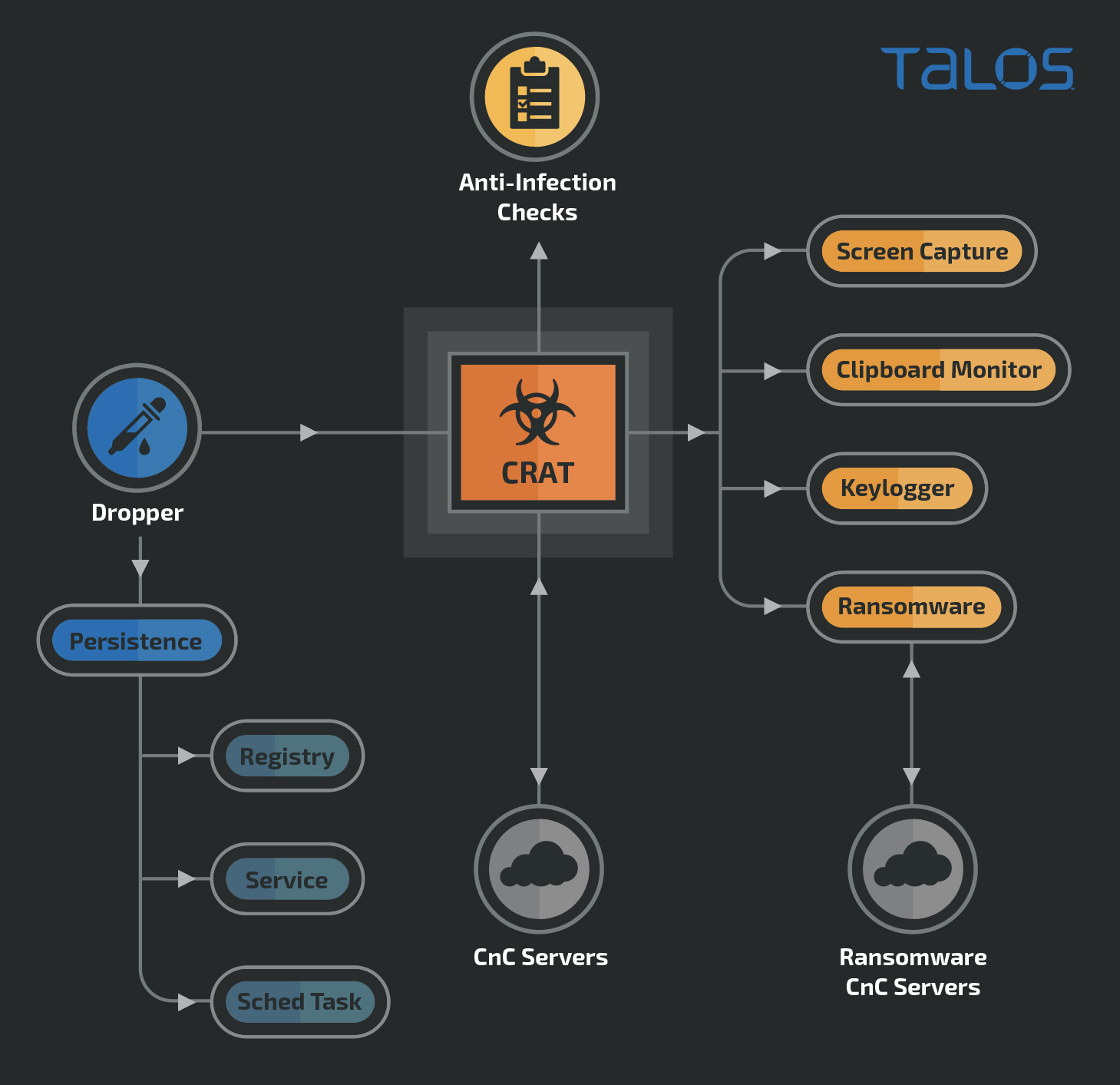
A new version of a remote access trojan (RAT) family known as CRAT is detected. Apart from the prebuilt RAT capabilities, the malware can download and deploy additional malicious plugins on the infected endpoint. One of the plugins is a ransomware known as “Hansom.” CRAT has been attributed to the Lazarus APT Group in the past. The RAT consists of multiple obfuscation techniques to hide strings, API names, command and control (C2) URLs and instrumental functions, along with static detection evasion. The attack also employs a multitude of anti-infection checks to evade sandbox based detection systems. The distribution vector of the new version of CRAT (v2) is currently unknown. However, it is highly likely the attackers may have re-used a maldoc-based infection vector to spread CRATv2 as well.
The attackers have also used file names and export API names in the CRAT DLLs to masquerade the RAT as a benign application’s library. The implant performs checks to verify its execution on an allowed endpoint. The implant uses a variety of criteria to identify a blocklisted system. Both versions of CRAT use HTTP to communicate with the C2 servers. The data sent to the C2 is in the form of URL-encoded form data. The C2 server will respond with a JSON containing command codes and supporting data to be recognized by the implant to execute a corresponding RAT capability. The CRAT malware consists of multiple RAT capabilities that allow it to be highly versatile and dangerous. CRAT executes these capabilities by receiving command codes and corresponding data from the C2 in the form of JSONs communicated over HTTP. The RAT also shows capability of stealing browser passwords. Other discovered capabilities include:
- Screen capture plugins
- Clipboard monitor plugins
- Keylogger plugins
- Ransomware
The ransomware plugin encrypts specific file extensions on the infected endpoint.
Impact
- Unauthorized Remote Access
- Detection Evasion
- Credential Theft
- Data Exfiltration
- Unauthorized Command Execution
- Files Encryption
Indicators of Compromise
MD5
- bf318b2d789a5d45c4a5863fbe0ece92
- ccdb051ad65d9f443206d659427d155f
- a3e3886ae43c6e67acf06d8041d8f4d2
- 2a9e49fc80fe5124ac98ff5b874fb4d4
- 6dafaabebf243e1ad2e5b49178230eb6
- 2576807597d95a550a36ba844ee11c62
- 43a070f0eeeb16450e3275855759e140
- 0af049b51a11c0896cb287610c7a313f
- 0646f5a3b0e66eb698960baf50a054cf
- cea68bb0e2d54b1fdca1baa7395906fa
- 2b326540fdf2989742000b1506770663
SHA-256
- eae3dc403d36b115aa4f7db64cb1a64fa50dbff2b6ce3d118eeb1f745d1ecd14
- 7050af905f1696b2b8cdb4c6e6805a618addf5acfbd4edc3fc807a663016ab26
- b962e4580e05e004df9fe2c22b34556bc513370c9a775bfe185e05a9d0df494e
- bd1a0425ffaafa54a1c950fbb3d0defe9fa145131e4bd15d392597de408f5287
- c0bd35a36ea5227b9b981d7707dff0e2c5ca87453a5289dc4a5cd04c7e8b728c
- 389518ac65595ad9138b5dd0185aae851d979d4705d74f191492f002e63438c5
- 916654e2ee43d2ee43f0d5e9d41f8527aaf239684f91f9b92ac5c1937cd45c91
- e893b4f6b6f3ab977c96ab5e2c6115969cbe46a143531bfc9920d1b9972ebc12
- eab9136da8cc5c1a8a9fc528d64ef1ce11e385def98957712887785178e202a3
- 04c46c55336ac40d567ef0aac98ff8424872b584ea169c1a098ced833dd9bab4
- 2cff5e7d4405bf09f423db1d7a8e535a6be2f68cc4ce4a5817ae01bee09f088a
- 4aa2dc282c56e397b501d84cfd6c582cc256c42e8b6722b45a592cf2008a6495
- 05d4da2cb9f6d5d44c399f42a81bb393b2ff6669d64ea773b58d2daf4df10d00
- 5b627647df675d746f63280cf10a221abfe0a93bab88a96e45b4734beb05c021
- 11c266c1b0f0428585d40fc95d1a7d3eedb3d0f304cf7ebc692c4487e18c9afb
- 26c70fa62e1d092ad1855900cd0db4e224b11e84fdf14105ade5e2b2a3dc1b62
- 37f3f6cdb0a35b4cea75b7cf2dae613c71370e00acdb2cebfc7d95fe33eb97a9
- 87ce3a13a58ae8007b002ac81f43dc364c1b93b0d3c2a19d46a4480caca9ae29
- 88f5c94ad66e75a66795875bacafb3cbbe87d1533ae3ddb41575b9711965c75b
- 844d60691d843de53d42b73d635314d50c4ba4d3b2aa2b93465ac0336e4c0588
- 931f57262214890f3eff9add25fb5dc2521185e4567c722637f173343b02b9fb
- 2263031c15809b49e7d8161e147a4844722f6f576d276b2be38a0c794417dd2a
- 6f79db3e7fa1f3c9e1ea2e0fe098994f109949f82b97c6612386693164d3c7e2
- ca3372bb37e7109896c28247faadd157759d5e68ac324a54ff0759590f956094
- 0eca58ef6f2aba6b3e686f76039945b3a8a8110d357a4f8d857757c218ca0c1e
- 59628b36ba65a57600c48eaa57c8dcfffc955e447cb3e41b7351e875b359f714
- a668af2c1b45bf83d509c88ad4b3e6fbadc7e9e3db4ea688888c7712866d1339
- 955abf30fd464dd572938eaf324d3447ecd8cb6df183bbddee2a58f54da83f4c
- 2916801be5b6d26d735aaa11eb5631fc6dbe234ed2e0980b8d7366c89ad7ba39
- 8377a53f7890f3cf01f8919207c981fb63b1b0e63860d5731622a0cad94fdd09
- 8ae6f663bf40036379857d65521ce1c78c11cd9b5b4848cec0e7f1ad56e65743
- ab794769599c3f046d34d00051685b7235bce119f212ec8739b6e206dd73b0bf
- 1ea8b9f307f2c4202380f1fe14044ff4b9140337b53fdf627e5411e979b4b5ea
- 3b55f8467b2d3bc34c7fe4e0c4502bc1045c50d7c7fedda4a14eaf9094dfc8bf
- 3f47d73a9d6597da1bdbf36f804b0b69a9958225ace088747098d3a24f5a5957
- 5464728537836d4aa3d03e4d29ef21e59a324252c4b2a15ec21e9f5280f7c280
- 7a78dacbb7ff88b536d4a8db4e647df9efed8cea2d26cef0e21f7791e61bfbad
- 1101d00223a62e77718da28053758208897d1dc627a06a01f0e620a6ccad3812
- 277931bf51f195fceb9befad6f4cc9e613d203ed90d3e4a05a16bc603809dec6
- 4dccd9861da3b47bef43c72546044c1d136a5cb020aaa65a1ea494aec35e4910
- 5e10cda5415e28b3efc9b909da6518d1cbcb56957e9850b99a4eee3893400012
- 5fd89dbd129877d5141f9731a61af867b74fc7a33213233307b725ec97532a7b
- 72d7b55e82080ff84693e1ecdfa7128ef9c513b3b8cc5e411715a40ef4ee0557
- 8f0bfbde00e5e86223e586874df892e6fb2b97b133a909b7fdeacf7614df478f
- 9461599bc85cf2ef11cb79a827fd365a086726b7c022fb2bfe5fb9f83e71cf9a
- f051c2f99b2d94b0fc5ae7893ec0467f4175cfa926cfc573a6b65a40c566f94d
- e93423a1c8add21c5676680a090ddc913d359c29ea9e44ffc91fb10396e3e858
- a24d66f4356de33ba9227d4e496cc975995f1bd72d72e47f74f07648c45c5308
- 147f1de257ccbe54b0fca9e61e0f2061172459bef4eeb12014d27e48d99f27ab
- 1c17b631988d0b8b722adf9c973c6577c7983a9b0cb069dd1d442d04f4dd73df
- 2ef70a256dde1a9700527c995be417447dee1857759e8279aa7a287f85c9de96
- 359bfd21ed9a5deedc19700355776ede266e5c8532584289db45ebe2fd8d8afe
- 3c2e708989193b3497c2c97c3957d4abd2d5989c82832ce5c4a3b5a4c9ecd3f8
- a1c7709d147d8182892585bc965317816367ebabc273e8a99559ade24b19ed7f
- 057cffe539a414ec4cef730e4fbf7861b61a7331bbd6d7feb55c76221a8cc6d3
- 12a7cec5631141f61ef159fbb43103a3cdd79ddd3a0270df62d4c4fa4635b03e
- 6d57df368c3e58be61bc36ee35123dcc5ce6d7a04cd6acfe7e10588038589ad4
- a7da1ec5745bb7ef5a4fd05d37d83b49b41ab70fae518e6a00b7caa30c417576
- 3c6b9fb9d680704a1a6c17ef5b3e10b043d15c137dc04688f5802cddbddf90fe
- a52a8a9c99f58fb18ca3f969736f1deffd611c35851cff1bd5bd36ef27f2426d
- f070b78ca7269addb922f9ea9a31f76198edb2e1064d9b04ca8d80ecba175ca4
- 683b4472a0df8af6c93ff10179e981a7908173bfb81bac2e12a3b9a022cf08d7
- 49aa98e2100752c09d01a7638ea9ead3dd2fc72d826c4b77d188990b3599b08c
- 9f953f544afd265176ecb904cc8286cafc27270df0cec56265259c1588083202
- a052ee9f75231a60ad1210411b7296ff5adf7e9e268bf2f123f0560e0cb37b09
- 46fd13169cf8e3dcefbd552918a0914261fd22dc22bd9cba167042288432f2b2
- 9a6d3d07e784247fac1292c0f17a46247e8bdeb1f468c9b8b48c4459063c3ed5
- 70d92da003eb044d9c5aa057400256a51836466d2f20066deedf64e294466c20
- eb9382b77f7ed3429b0fcfb5d5d64c0702f0c4d91c45bb8d3442ff1f851b8035
- cd20d7209db84b35cae88affe228f42258b497eee2b36f0e3364779e58e5e2ce
- e4c1eaf014773cc25e2881fa2b2a67490a73c66683f5746276af7067777ed8b2
- 396ffa925165de08d0b5bf6cc6974a02a18b44ce60c3d3e657ba6c6153760138
- 9fc572e3a6c30221e5eecdd488efabbaf1bab04dff34860263495620fa4706c1
- 0313641c0ed1defa6cb52e787f81eab3de8c0c546b4e157d803aab721fec3dc8
- 7a3915a7d919fb266496616a06311c456c8e45b98cfd24c92ac4bf0af75fa3ef
- 02c4ba967900b49828985f7b67ebd21daa11b8bc9e4e0b6e5e9fef2de8fdc6d4
- 3d47ca0810b2d296aaa2541ef621f5d834dfbbd89cb671a2a95b7f2bddbd3e4e
- bb1af121502e40a549135b72f34ad49d11cfbfa49b5cbcf549777549087fe751
- fb2ad747903f46d03b19b12c46a3e678e8a0c156092fb334aab47714a041265c
- cb141c743ac41784501e2e84ccd9969aade82b296df077daff3c0734bb26c837
SHA1
- 750f7f89b89bf9d33661e11d18562d2d90b09ac9
- 14050be50c0220f70c60af7a1d279afcca06294e
- 288af05268b194be58183f87cad4ba664c73202e
- 49bc6b93623861982bb68cf7b0b2fbfc78b5443d
- 5a6fc000489cde1bb70274562210ee1738923986
- 6bb3c6032ff60820cf0ad5dd097e88c72173674f
- 05fc48aa9558377874b2ee7df45b41333117f89f
- d60032efb552c1af6ca3d62166804c8fd9bff641
- 44ab359993da31d9f335b58ecf1ae091704a987d
- eabbe1d9e495dabc2a4c538502ef6fea44dc975e
- 613750e0ab2c1243d5c4debd1220288571762d7c
URL
- http[:]//www[.]sofa[.]rs/wp-content/themes/twentynineteen/sass/layout/h1[.]jpg
- http[:]//teslacontrols[.]ir/wp-includes/images/detail32[.]jpg
- http[:]//teslacontrols[.]ir/wp-includes/images/detail31[.]jpg
- http[:]//publishapp[.]co/update/check[.]php
- http[:]//publishapp[.]co/update/check[.]php
- http[:]//sideforum[.]cc/forum/list[.]php
- http[:]//freeforum[.]co/forum/list[.]php
- http[:]//goodfriend[.]pro/projects/list[.]php
- http[:]//friendship[.]me/users/register[.]php
- http[:]//threegood[.]cc/api/manage/customers
- http[:]//Engpro[.]xyz/images/detail[.]php
- http[:]//infocop[.]me/products/list[.]php
- http[:]//teamspit[.]pro/adverts/follow[.]php
- http[:]//dodoi[.]cc/photos/preview[.]php
- http[:]//advertapp[.]me/user/invite[.]php
- http[:]//insideforum[.]me/forum/list[.]php
- http[:]//anyoneforum[.]cc/forum/list[.]php
- http[:]//goodproject[.]xyz/projects/list[.]php
- http[:]//hellofriend[.]pro/users/register[.]php
- http[:]//moonge[.]cc/wp-content/plugins/google-sitemap-generator/sitemap-builder-embed[.]php
- https[:]//calculactcal[.]org/wp-content/themes/twentysixteen/body[.]php
- http[:]//3cuartos[.]com/wp-content/plugins/music-press-pro/templates/global/update[.]php
- https[:]//http[:]//worldfoodstory[.]co[.]uk/wp-includes/register[.]php
- https[:]//bokkeriejesj[.]nl/wp-content/plugins/music-press-pro/upload[.]php
- https[:]//encontrosmaracatu[.]com[.]br/wp-content/plugins/music-press-pro/templates/global/topmenu[.]php
- https[:]//http[:]//theblackout[.]fr/wp-content/plugins/music-press-pro/music-pro[.]php
- https[:]//mokawafm[.]com/wp-content/plugins/ckeditor-for-wordpress/ckeditor/plugins/image/dialog[.]php
- https[:]//http[:]//tiramisu[.]it/wp-content/plugins/wp-comment-form[.]php
- http[:]//http[:]//kartacnictvi[.]cz/wp-content/plugins/ckeditor-for-wordpress/ckeditor/plugins/image/upload[.]php
- http[:]//http[:]//dimer-group[.]com/wp-content/plugins/ckeditor-for-wordpress/ckeditor/plugins/image/download[.]php
- https[:]//ecolerubanvert[.]com/wp-content/plugins/image-intense/know[.]php
- http[:]//lwac[.]com/wp-content/plugins/gallery-plugin/includes/demo-data/images/music/photo[.]php
- https[:]//http[:]//copansrl[.]it/wp-admin/user/invite[.]php
- https[:]//arar-musique[.]fr/wp-content/plugins/music-press-pro/includes/admin/upgrade[.]php
- https[:]//http[:]//firstalliance[.]church/wp-content/plugins/music-press/templates/404[.]php
- https[:]//erickeleo[.]com[.]br/wp-content/plugins/music-press-pro/go[.]php
- http[:]//http[:]//kingsvc[.]cc/index[.]php
- http[:]//http[:]//sofa[.]rs/wp-admin/network/server_test[.]php
- http[:]//http[:]//afuocolento[.]it/wp-admin/network/server_test[.]php
- http[:]//http[:]//mbrainingevents[.]com/wp-admin/network/server_test[.]php
- http[:]//http[:]//afuocolento[.]it/wp-includes/process[.]php
Remediation
- Block the threat indicators at their respective controls.
- Do not download files attached in untrusted emails.
- Keep all systems and software updated to latest versions.
- Enable multi factor authentication.








