

Rewterz Threat Alert – Quasar RAT – Active IOCs
September 7, 2022
Rewterz Threat Alert – GuLoader Malspam Campaign – Active IOCs
September 7, 2022
Rewterz Threat Alert – Quasar RAT – Active IOCs
September 7, 2022
Rewterz Threat Alert – GuLoader Malspam Campaign – Active IOCs
September 7, 2022Severity
High
Analysis Summary
A zero-day vulnerability in Microsoft Office is being actively exploited in the wild, and while there isn’t currently a patch, the software giant has published workarounds to thwart attacks. CVE-2022-30190, also known as “Follina,” is a remote code execution (RCE) vulnerability affecting the Microsoft Support Diagnostic Tool (MSDT) in Windows.
CVE-2022-30190
Microsoft Windows could allow a remote attacker to execute arbitrary code on the system, caused by a flaw in the Support Diagnostic Tool (MSDT) component. By persuading a victim to open specially-crafted content, an attacker could exploit this vulnerability to execute arbitrary code on the system. Microsoft Support Diagnostics Tool (MSDT) is used by support professionals for troubleshooting.
According to the researcher, maldoc retrieves an HTML file from a server using Word’s template feature. The malicious payload is then obtained via the “ms-msdt: //” URI scheme.
The attackers who successfully exploit this vulnerability can run arbitrary code with the privileges of the calling application. The attacker can then install programs, view, change, delete data, or create new accounts in the context allowed by the user’s permissions.
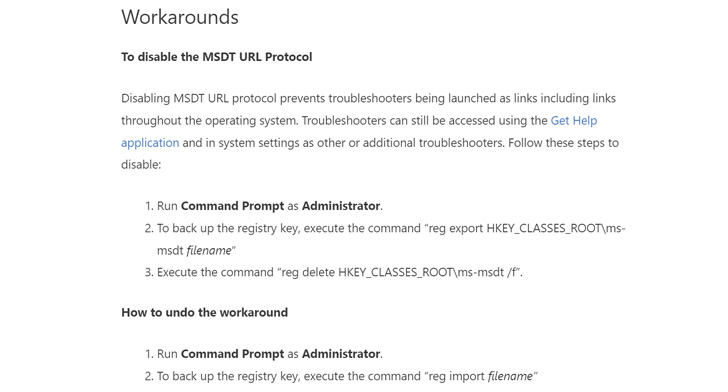
Here are the workaround guidance shared by Microsoft:
Impact
- Code Execution
- Privilege Escalation
Indicators Of Compromise
Domain Name
- kitten-268[.]frge[.]io
- kompartpomiar[.]pl
MD5
- eafa11070f213f16efc030f625a423d1
SHA-256
- daaa271cee97853bf4e235b55cb34c1f03ea6f8d3c958f86728d41f418b0bf01
SHA-1
- b1847c89143fad810b7a3686296b9c1e91ad087c
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicator of compromise (IOCs) in your environment utilizing your respective security controls
- Use Microsoft Automatic Update to apply the appropriate patch for your system, or the Microsoft Security Update Guide to search for available patches.
- Customers using Microsoft Defender Antivirus should turn-on cloud-delivered protection and automatic sample submission.
- Customers that use Microsoft Defender for Endpoint can set the “BlockOfficeCreateProcessRule” attack surface reduction rule, which prevents Office apps from generating child processes.








