

Rewterz Threat Alert – APT Group Gamaredon aka Shuckworm – Active IOCs
February 20, 2024
Rewterz Threat Alert – A New PikaBot Malware – Active IOCs
February 20, 2024
Rewterz Threat Alert – APT Group Gamaredon aka Shuckworm – Active IOCs
February 20, 2024
Rewterz Threat Alert – A New PikaBot Malware – Active IOCs
February 20, 2024Did you know? The US has incurred the highest data breach cost, reaching USD 9.48 million, an increase from USD 9.44 million, for thirteen consecutive years (Statista, 2024).
Middle East (USD 8.07 million), Canada (USD 5.13 million), Germany (USD 4.67 million), Japan (USD 4.52 million), and the UK (USD 4.21 million), respectively followed.
The rise in cyberattacks globally is not coincidental. It is the product of the fastest-evolving technology landscape. From COVID-19, remote work, and Generative AI making the headlines, malicious tools such as FraudGPT, WormGPT, ChaosGPT, DarkBERT, and DarkBART, and new cyber threats like QR code phishing and denial-of-service (DDoS) attacks underscore the critical need for robust incident response planning.
This blog offers a comprehensive understanding of incident response (IR) and how adopting proactive defense strategies can shield businesses and users against lurking, unforeseen threats in the digital realm.
What is Incident Response (IR)?
Incident Response (or cybersecurity incident response) is a combination of processes and technologies used to detect and respond to cyber threats, cyberattacks, or security breaches. As part of the incident management lifecycle, this systematic approach aims to proactively prevent cyberattacks and minimize damage (financial and operational) without disrupting business continuity. As a result, it streamlines alert monitoring, reduces
response times, and enables security operations teams to focus on strategic threat hunting.
What is an Incident Response Plan (IRP)?
Think of an Incident Response Plan as a strategic playbook for handling digital security emergencies. Essentially, it’s a set of guidelines outlining what an organization should do in the event of a security incident to minimize the impact.
Incident Response Planning is like having a strategy in place to prepare for potential cyber "storms" – swiftly identifying and neutralizing cyber threats or data breaches through prompt and decisive action.
How does an organization develop one?
Implementing a risk-based approach, the Incident Response Planning process incorporates formal processes and technologies to detect and contain threats promptly, ultimately reducing financial losses and regulatory fines. Tailored to each organization’s unique environment and specific threats and regularly updated for ongoing relevance and effectiveness, this plan serves as a valuable guide. It details actionable security incidents, assigns roles, defines task timelines, and provides clear instructions.
Why prioritize an Incident Response Plan?
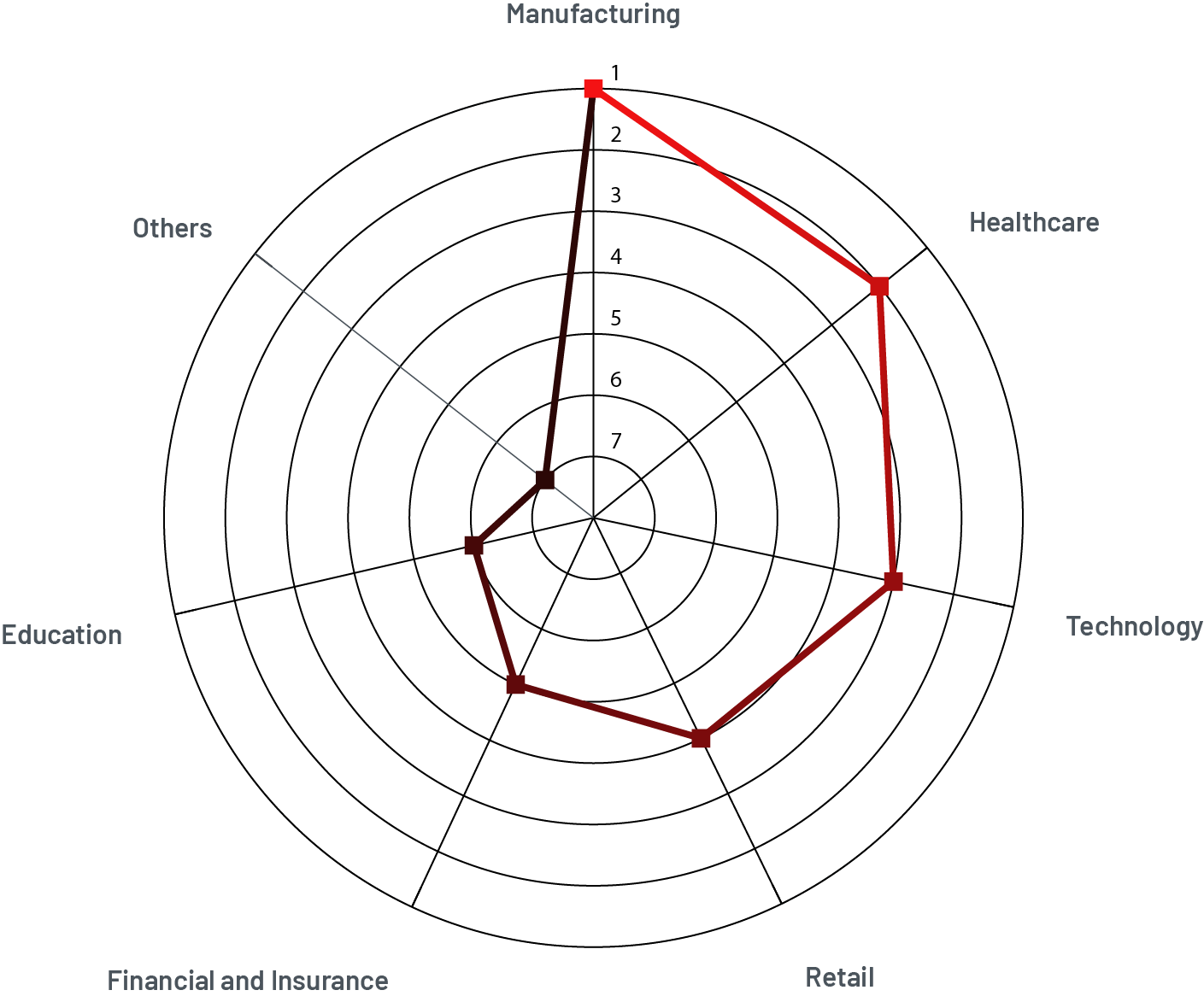
Cyberattacks do not discriminate, targeting individuals, businesses, and industries alike. Our Threat Intelligence Report - 2023 shows that the manufacturing industry remains a top target. However, last year saw an intensive target in the healthcare, technology, and retail sectors, with the healthcare industry incurring data breach costs of around USD 10.93 million. Moreover, the financial and insurance sectors faced significant cyberattacks, not just from ransomware but also from Advanced Persistent Threat (APT) groups. Consequently, this year, the education, government, public services, and energy sectors are highly susceptible to cyberattacks.

Industries struckby phishing in 2023
Our latest report uncovered the top industries affected by phishing last year, including finance, social media, cloud, healthcare, internet/telecommunication, e-commerce/logistics, government, and other sectors.
The phishing attacks spiked by 173% in Q3 2023, posing a pervasive threat across all industries. While finance and social media are major targets, the cloud and internet industries also witnessed a massive surge in cyber incidents.
Attackers frequently obtained access to multiple environments in the cloud, as evidenced by 39% of breaches spanning various platforms, resulting in a higher-than-average cost of USD 4.75 million.
This dynamic threat landscape necessitates a flexible cybersecurity strategy. As technological innovations continuously evolve, malware will persist in becoming more sophisticated, taking many forms, ransomware being only one. It is only practical for forward-looking businesses to not only react to emerging threats but also proactively anticipate and mitigate potential vulnerabilities. Establishing a well-rounded security incident response plan and arming up with human-centric security designs and threat exposure management will ensure peace of mind and preparedness for both its customers and employees.
Incident Response Plan (IRP) Frameworks
There are two recognized IR frameworks, the National Institute of Standards and Technology (NIST) and SysAdmin Audit Network Security (SANS), which numerous organizations utilize to equip their IT teams in establishing robust incident response planning.
NIST Framework: Offers an integrated approach, combining containment, eradication, and recovery, ideal for rapid response and significant, complex incidents. Favored for its holistic, less compartmentalized handling of incident response.
SANS Framework: Provides a structured, phase-by-phase process with clear roles and responsibilities suitable for methodical, step-by-step incident management. Ideal for environments requiring detailed phase tracking and documentation.
It's essential to understand that no singular "right" or "wrong" approach exists. The framework selection often stems from the fact that different organizations and situations call for different strategies. Both frameworks are highly respected and widely used in cybersecurity, but they each have unique strengths and applications.
The following section will expand on the six steps outlined by SANS:
Phase 1: Preparation
Goal: Establish foundation readiness for incident management
Comprehensive preparation is essential before any incident. Organizations conduct rigorous risk assessments to identify vulnerabilities and adapt security policies for emerging threats. Training, extending beyond the incident response team to all personnel, focuses on recognizing and responding to cyber threats. Templated incident response plans clarify roles across the organization, ensuring cohesion among executives, security leaders, and operational teams. Training and awareness programs are continuously refined to align with evolving cyber threats. Advanced logging technologies are prioritized to expedite event analysis, alongside establishing a virtual environment for efficient log review with ample storage. Lessons learned from incidents are documented to enhance future incident management strategies.
Phase 2: Identification
Goal: Detect incidents and collect indicators of a breach
Security teams, facing thousands of daily alerts indicating suspicious activity, work diligently to separate real threats from false positives. Internal and external detection systems are combined for a comprehensive approach. Upon identifying an incident, the focus shifts to a thorough investigation of its nature, documenting crucial details such as the breach's source, the type of attack, and the attackers' goals. Ultimately, systems are finely tuned to balance alert sensitivity, ensuring critical threats are identified without overwhelming the security team. This stage also involves promptly informing stakeholders about the incident and outlining the next steps, ensuring clear communication and preparedness for immediate actions.
Phase 3: Containment
Goal: Rapid response and strategic isolation of threats
Containment, a critical phase where swift action is essential, minimizes potential damage. The team's immediate priority is to isolate affected applications or systems, effectively cutting off attackers' access and preventing further penetration into the business network. This involves short-term actions like shutting down compromised systems and closely monitoring for any malicious activities. Simultaneously, long-term measures are implemented, which include isolating affected devices until the entire eradication process is complete. Throughout this phase, every action taken is meticulously documented, devices are categorized based on the severity of compromise, and protection of critical assets like domain managers and file servers is prioritized — ensuring mitigation of the overall impact while maintaining business continuity.
Phase 4: Eradication
Goal: Thorough elimination of threats
Following containment, the eradication phase is critical for completely removing any trace of attackers and malware from the system. The process involves meticulous cleaning of disks, restoring from clean backups, or reimaging entire disks as needed. It is crucial to adhere to company policies throughout this process and to document every action taken during this removal phase. Additionally, the team may need to take systems offline as part of this comprehensive cleanup temporarily. After eradication efforts are complete, conducting active scans is essential to ensure no remnants of the threat persist. Throughout this phase, ongoing communication with stakeholders is necessary to keep them informed about the progress and actions taken.
Phase 5: Recovery and Reflection
Goal: Restore normal operations
The recovery phase marks the return to normalcy, which involves reinstating systems, retrieving data from backups, and monitoring any remaining threats to reinforce security. Simultaneously, a thorough reflection of incident response steps is crucial. This includes evaluating detection timing, containment duration, tool effectiveness, and staff training. Regular updates to incident response plans and processes, complemented by ongoing training and drills, ensure continuous improvement and readiness for future incidents. This integrated approach not only addresses immediate recovery needs but also fortifies the organization's overall incident response capability.
Phase 6: Lessons Learned
Goal: Document incidents, evaluate, and enhance future incident response strategies
Post-incident, the team conducts a comprehensive review to learn from it. Using insights from this experience helps fortify the organization's overall preparedness and response *capabilities for future incidents. The team iteratively evaluates tools, staff training, and response effectiveness and regularly updates incident response plans, technology, and processes. To leave no stone unturned, ongoing training, simulations, and drills to ensure a well-prepared team
What’s next?
Did you know? A Ponemon survey revealed that 77% of participants lack a consistently applied formal incident response plan within their organizations. Additionally, among those organizations with incident response plans, only 32% characterized their initiatives as "mature.”
These findings are concerning, especially with the severity of the cyberattacks increasing year by year. The above facts and explanation underscore the indispensable need for a robust incident response plan. Facing the crisis is not an ideal time for learning and practicing actionable plans for business security. It is vital to establish an internal security incident response team equipped with the appropriate vulnerability management tools, SIEM systems, and low-code security automation playbooks.
How can Rewterz Incident Response Services assist you?
Whether you want to manage it internally or outsource some or all incident response activities, Rewterz Incident Response Services can help you streamline this pathway to security. Recognized among the top 250 MSSPs list for 2022 by MSSP Alert, Rewterz SIEM Optimization and SOC teams are poised to empower you against evolving cyber threats, ensuring Confidentiality, Integrity, and Availability (CIA). Utilizing cutting-edge threat intelligence and advanced Security Orchestration Automation and Response (SOAR) platform, SIRP, we enable real-time oversight of threat data, enhancing your incident response through standardized and streamlined processes.
Connect with our experts to tailor your Incident Response Playbook to fit your business dynamics!








