

Rewterz Threat Advisory – ICS: Advantech WebAccess Vulnerability
October 13, 2023
Rewterz Threat Alert – IcedID Banking Trojan aka BokBot – Active IOCs
October 15, 2023
Rewterz Threat Advisory – ICS: Advantech WebAccess Vulnerability
October 13, 2023
Rewterz Threat Alert – IcedID Banking Trojan aka BokBot – Active IOCs
October 15, 2023Severity
High
Analysis Summary
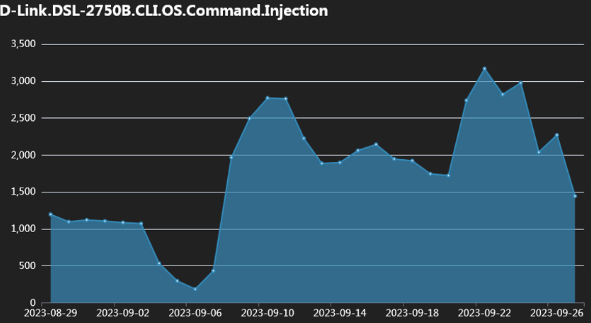
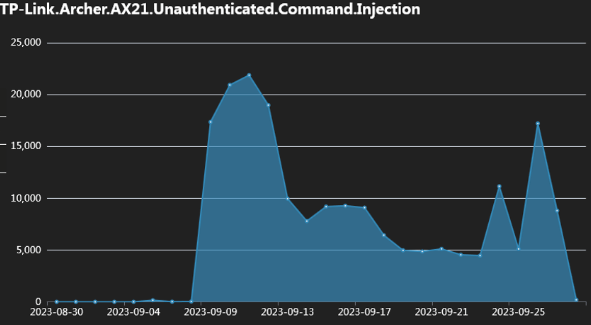
A Mirai-based DDoS malware botnet that is tracked as IZ1H9 has recently expanded its payloads by adding thirteen new exploits to target Linux-based routers as well as other routers from Zyxel, D-Link, TP-Link, TOTOLINK, etc.
The cybersecurity researchers have observed an alarming increase in the exploitation rates during the first week of September, the peak reaching up to tens of thousands of attempts to exploit vulnerable devices.
IZ1H9 enlists all of its compromised devices into its DDoS swarm to launch DDoS attacks on specific targets, which is presumed to be ordered by its clients who rent its firepower.
As more and more devices and vulnerabilities are targeted by a DDoS malware, there are increased risks of a powerful and large botnet that is fully capable of launching huge attacks against websites. Researchers have listed down the flaws exploited by IZ1H9 all the way back from 2015 to 2023:
D-Link devices: CVE-2015-1187, CVE-2016-20017, CVE-2020-25506, CVE-2021-45382 (These significant vulnerabilities enable remote attackers to deliver command injection through a carefully crafted request)
- Netis WF2419: CVE-2019-19356
- Sunhillo SureLine (versions before 8.7.0.1.1): CVE-2021-36380
- Geutebruck products: CVE-2021-33544, CVE-2021-33548, CVE-2021-33549, CVE-2021-33550, CVE-2021-33551, CVE-2021-33552, CVE-2021-33553, CVE-2021-33554 (arbitrary command execution flaws)
- Yealink Device Management (DM) 3.6.0.20: CVE-2021-27561, CVE-2021-27562
- Zyxel EMG3525/VMG1312 (before V5.50): CVE not specified but targets the Zyxel device’s /bin/zhttpd/ component vulnerability
- TP-Link Archer AX21 (AX1800): CVE-2023-1389
- Korenix JetWave wireless AP: CVE-2023-23295
- TOTOLINK routers: CVE-2022-40475/25080/25079/25081/25082/25078/25084/25077/25076/38511/25075/25083
The attack chain starts with the exploitation of one of the aforementioned CVEs, after which an IZ1H9 payload is deployed and injected into the targeted device. This payload launches a command used to fetch a shell script downloader from a specified URL.
After running the script, it performs several actions, including deleting logs, downloading, and executing various bot clients designed for specific Linux architectures. Subsequently, the shell script downloader disrupts network connections on multiple ports by modifying the device’s iptables rules.
Finally, the bot connects to the C2 sever to wait for further commands to execute. The commands it supports are concerned with the type of DDoS attack it wants to launch, like UDP, UDP Plain, TCP SYN, and HTTP Flood. The researchers also report that IZ1H9 has a data section with lots of hardcoded credentials that are used for brute-force attacks.
These brute-force attacks help in hacking into adjacent devices or authenticating to IoTs which don’t have any working exploit for the time being. It is highly recommended for the owners of IoT devices to use strong admin user passwords and keep them updated regularly to the latest version. Reducing their exposure to the public internet whenever possible is also helpful in avoiding risks.
Impact
- Denial of Service
- Command Execution
- Cross-Site Scripting
Indicators of Compromise
IP
- 194.180.48.100
- 2.56.59.215
- 212.192.241.72
MD5
- 9fbdcd7e36c9fd01085a96825d0bc186
- ca732733cd816e60655c82bce09bc715
- c0e82281a49e836a9ca75f44ca0749b5
- d3dc81a5e1f00704c32fe8e5f79ab84f
- 9f471c6d81cfcbb1d13b9401a9ffd7b2
- e06c85ea1da870053d4734a9ce52efa8
SHA-256
- c8cf29e56760c50fa815a0c1c14c17641f01b9c6a4aed3e0517e2ca722238f63
- 1e15d7cd0b4682a86620b3046548bdf3f39c969324a85755216c2a526d784c0d
- 7b9dce89619c16ac7d2e128749ad92444fe33654792a8b9ed2a3bce1fee82e6a
- b5daf57827ced323a39261a7e19f5551071b5095f0973f1397d5e4c2fcc39930
- b523ea86ebfd666153078593476ca9bd069d6f37fa7846af9e53b1e01c977a17
- 8d07f15dd7d055b16d50cb271995b768fdd3ca6be121f6a35b61b917dfa33938
- 34628bcfc40218095c65678b52ce13cea4904ce966d0fd47e691c3cb039871ec
- afc176f7b692a5ff93c7c66eee4941acf1b886ee9f4c070faf043b16f7e65c11
- df9ee47c783fbe8c3301ed519033fc92b05d7fd272d35c64b424a7e46c6da43b
- 737ba9e84b5166134d491193be3305afa273733c35c028114d8b1f092940b9a3
- 0aa9836174f231074d4d55c819f6f1570a24bc3ed4d9dd5667a04664acb57147
SHA-1
- 3c092422bf2dbb743f9b58534c36d2866a32e4ee
- f9095595b1d8b9c1c649b1ec0b602e7a478e8f20
- 8426aba296c22fd4a4d5fe5f12762e49612d417d
- 8d68ffdfd36e63133d6ee1ab89f1b9558035cfc3
- 5812b95f33335da463c7aa33feafa514e72f49cf
- d2043490c52410808cfe043e8e6c0df60859e662
- 59d9c55be338a85dddbd53cc3546e2a4e7b9e704
- 5aa63fba63bd4e9b5c213cc7c0ae7f0161e76dc2
- 908b5ecefbd95791185855c9db8843d2f1054424
- 60ff3f8b1f685a66c8a74539a424062a9ca865aa
- 5a092c1f9760b9bb19f2e132e74c1d174ebdb532
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Ensure that firmware updates are received only from official sources and not from third-party websites or unverified sources.
- Avoid downloading firmware updates from unfamiliar websites or links shared through unverified sources.
- Only install apps from trusted sources, such as Google Play Store for Android TV. Avoid sideloading apps from unverified third-party sources.
- Consider installing reputable security software or antivirus apps on your Android TV box to detect and block malware.
- If the device allows you to change default passwords or access credentials, do so immediately to prevent unauthorized access.
- Use a strong and unique Wi-Fi password to secure your home network.
- Consider implementing network-level security features like firewalls and intrusion detection/prevention systems to monitor and block malicious network traffic.
- Isolate your Android TV box from other devices on your network to minimize the potential impact of a compromise.
- Patch – Patch and upgrade any platforms and software timely and make it into a standard security policy. Prioritize patching known exploited vulnerabilities and zero-days.
- 2FA – Enable two-factor authentication.
- Antivirus – Enable antivirus and anti-malware software and update signature definitions in a timely manner. Using a multi-layered protection is necessary to secure vulnerable assets.








