

Rewterz Threat Alert – Revival of Crimson RAT – IoCs
February 3, 2020
Rewterz Threat Alert – Iranian Campaign Tailored to US Companies Introduces TONEDEAF 2.0
February 3, 2020
Rewterz Threat Alert – Revival of Crimson RAT – IoCs
February 3, 2020
Rewterz Threat Alert – Iranian Campaign Tailored to US Companies Introduces TONEDEAF 2.0
February 3, 2020Severity
High
Analysis Summary
A new phishing campaign distributing malware pretends to be from the Spamhaus Project warning that the recipient’s email address has been added to a spam block list due to sending unsolicited email. Spamhaus Project is an organization that creates spam block lists that mail servers can utilize to block known spammers from sending emails to recipients in their organization. Due to this, using Spamhaus as the theme of phishing scam could alarm email administrators enough to cause them to hastily open the link in the email and thus become infected. These email states that the recipient must “Urgently Take Action” because their email address has been added to the Spamhaus Block List (SBL) and will be blacklisted on mail servers unless they follow the instructions found at a listed URL.
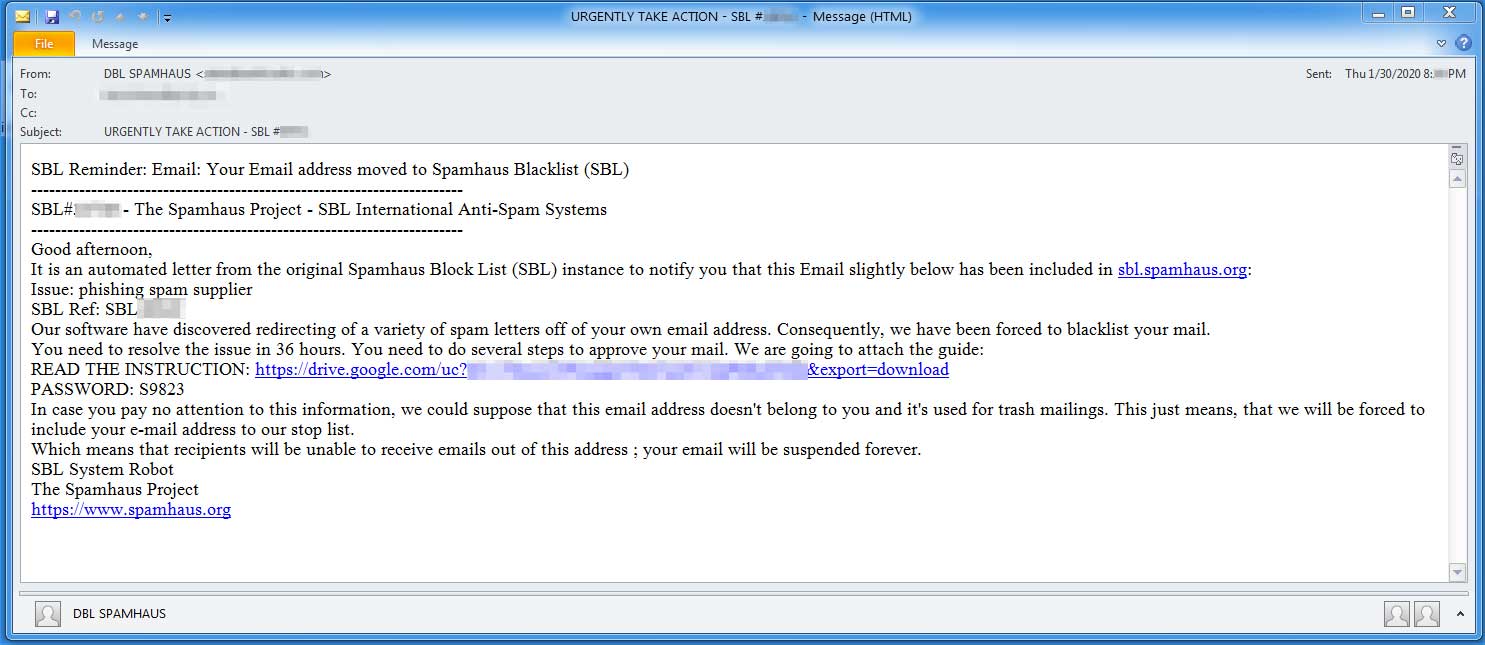
In the email will be a Google Drive link and a password for a file that is allegedly the instructions needed to remove the email address from the Spamhaus Block List.
Clicking on this link will download a password protected file named SPAMHAUS_SBL_i9k#888771.zip that contains an obfuscated Visual Basic Script (VBS) file SPAMHAUS_SBL_i9k.vbs.
When executing the VBS file, it will create a randomly named text file in the %Temp% folder, which are reported to be Ursnif malware executables, which is then launched by the script.
Ursnif is a data-stealing Trojan that records what a victim types on a computer, what sites they browse to, what is copied into the Windows clipboard, and what programs they run. This information is then saved in log files and sent back to the attacker’s web site.
Impact
- Credential theft
- Exposure of sensitive information
- Data exfiltration
Indicators of Compromise
Filename
- SPAMHAUS_SBL_i9k#888771[.]zip
- SPAMHAUS_SBL_i9k[.]vbs
MD5
- f7f748dadd2785c05af1747997caf331
- 8b341edd7c197ab87599689a69b8a016
- 26fe92f0e744ca60857f9e98c91c2a35
- 63b3fbf9a89cb6a6b88c324c6dd247d2
- 264d59a72ca08158c6fc43082554058e
SHA-256
- 279c3ce5e4ef8d0a58e2571b47eee36063d6655e66d20a62b2175960b040a1e3
- e6ad7e2acd02f980d038e3b007a556ea1f3dbe9f9a98bc8b3f7e4d4ac25b7310
- 926052d7e82f540bc99906759f15bd3c6cf49be1f229f57bf43ab6b6062b6104
- b99d38aa1493b28f7b9623129f20f5a8be0933712f92dbacace710be3313f4a6
- 5692db418539eda5d897e4eaabe43b31675220f2f6173b8c6c87b969d91329d4
Remediation
- Block the threat indicators at their respective controls.
- Do not download files attached in unexpected emails.
- Do not execute .vbs files downloaded from unverified sources.








