

Rewterz Threat Alert – NetWire RAT Delivered via IMG Attachment
January 8, 2020
Rewterz Threat Advisory – Active Scanning of Vulnerable Citrix Servers
January 8, 2020
Rewterz Threat Alert – NetWire RAT Delivered via IMG Attachment
January 8, 2020
Rewterz Threat Advisory – Active Scanning of Vulnerable Citrix Servers
January 8, 2020Severity
High
Analysis Summary
A new ransomware called SNAKE that is targeting networks and aiming to encrypt all of the devices connected to it. The ransomware contains a level of routine obfuscation not previously and typically seen coupled with the targeted approach.When started Snake will remove the computer’s Shadow Volume Copies and then kill numerous processes related to SCADA systems, virtual machines, industrial control systems, remote management tools, network management software, and more.
It then proceeds to encrypt the files on the device, while skipping any that are located in Windows system folders and various system files.
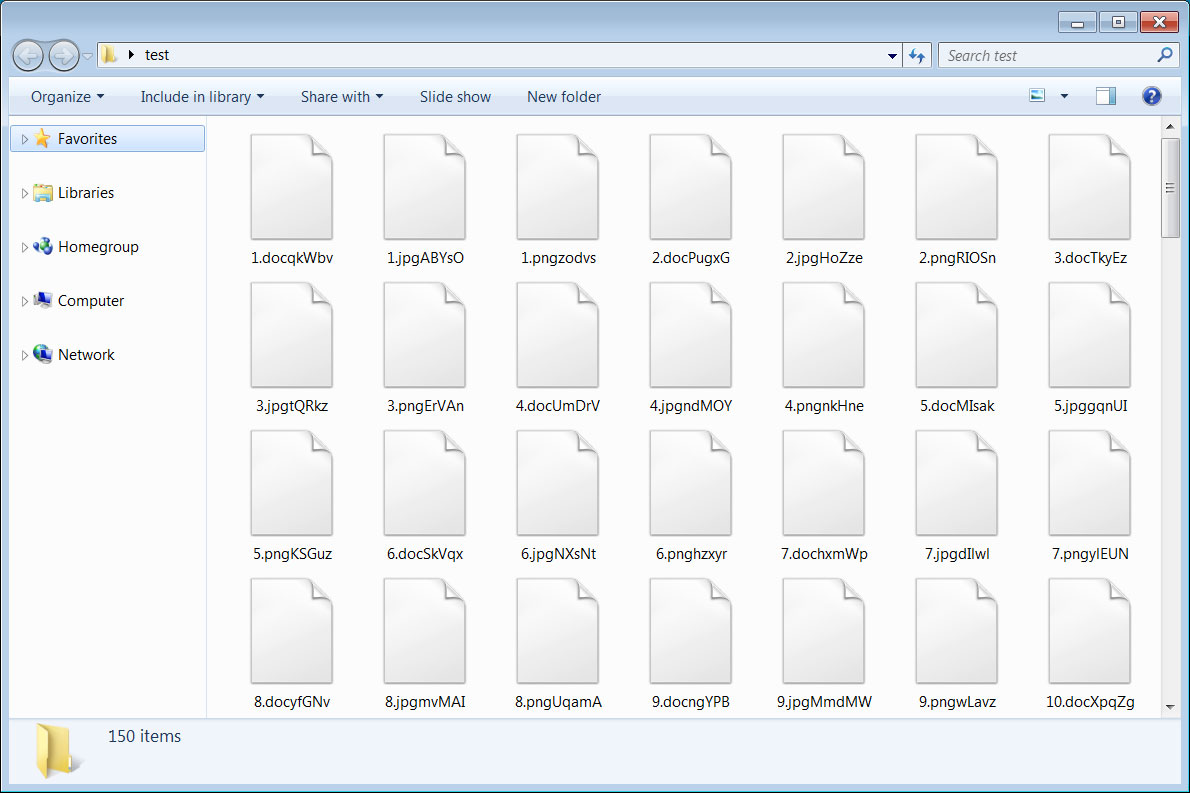
When encrypting a file it will append a ransom 5 character string to the files extension. For example, a file named 1.doc will be encrypted and renamed like 1.docqkWbv.
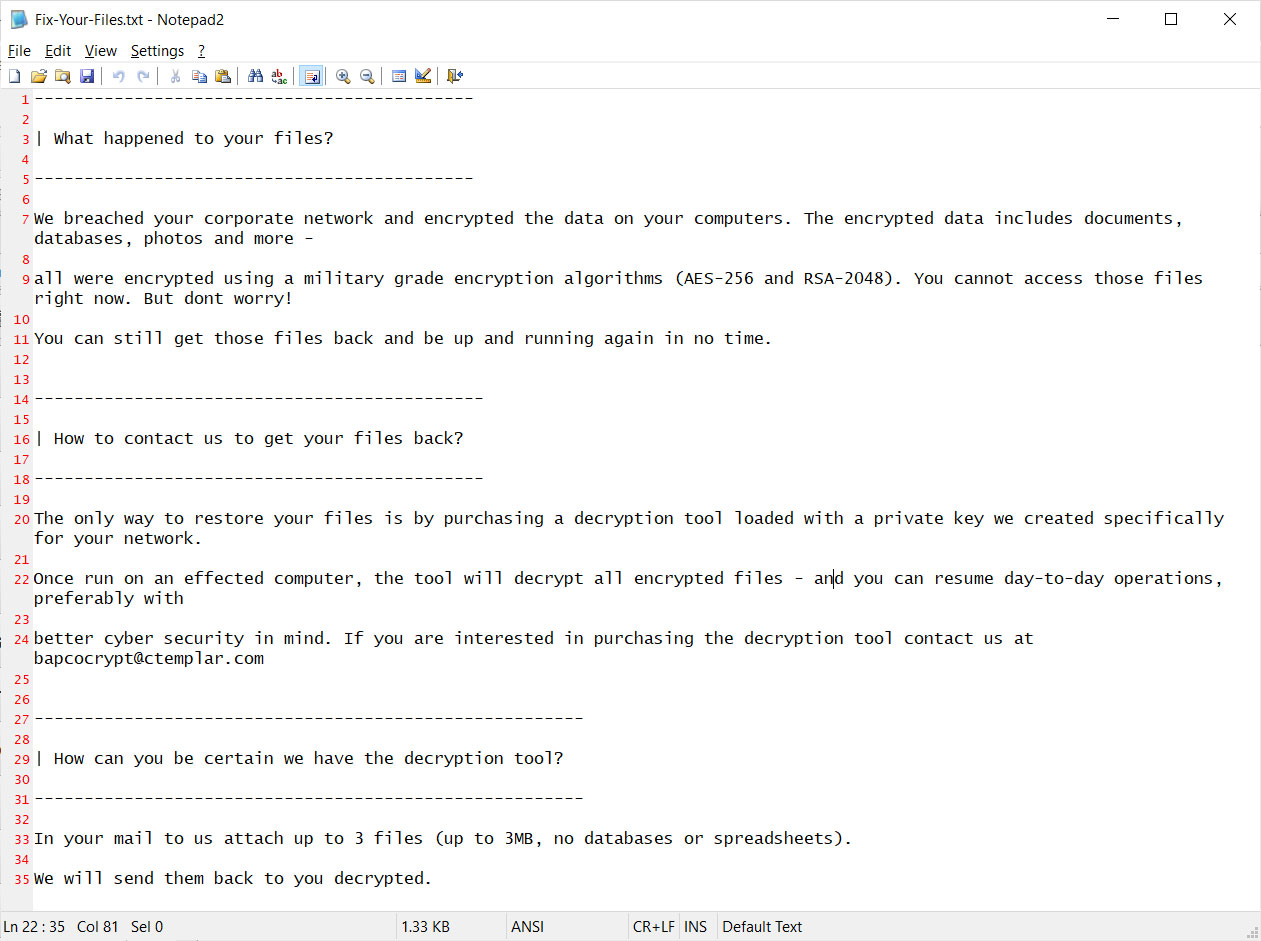
When done encrypting the computer, the ransomware will create a ransom note in the C:\Users\Public\Desktop folder named Fix-Your-Files.txt. This ransom note contains instructions to contact a listed email address for payment instructions.
Impact
File encryption
Indicators of Compromise
MD5
3d1cc4ef33bad0e39c757fce317ef82a
SHA-256
e5262db186c97bbe533f0a674b08ecdafa3798ea7bc17c705df526419c168b60
SHA1
f34e4b7080aa2ee5cfee2dac38ec0c306203b4ac
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.








