

Rewterz Threat Alert – Bazar Backdoor IoCs
April 28, 2020
Rewterz Threat Advisory – Adobe Security Updates for Magento
April 29, 2020
Rewterz Threat Alert – Bazar Backdoor IoCs
April 28, 2020
Rewterz Threat Advisory – Adobe Security Updates for Magento
April 29, 2020Severity
Medium
Analysis Summary
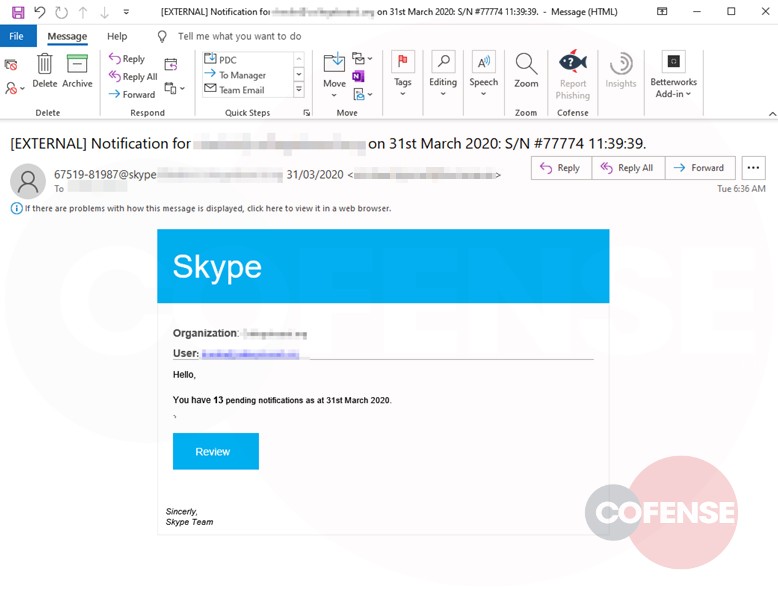
A new phishing campaign spoofing Skype, the popular video calling platform that has seen a recent spike in use amid the need to keep employees connected as they work remotely. With so many people working from home, remote work software like Skype, Slack, Zoom, and WebEx are starting to become popular themes of phishing lures.
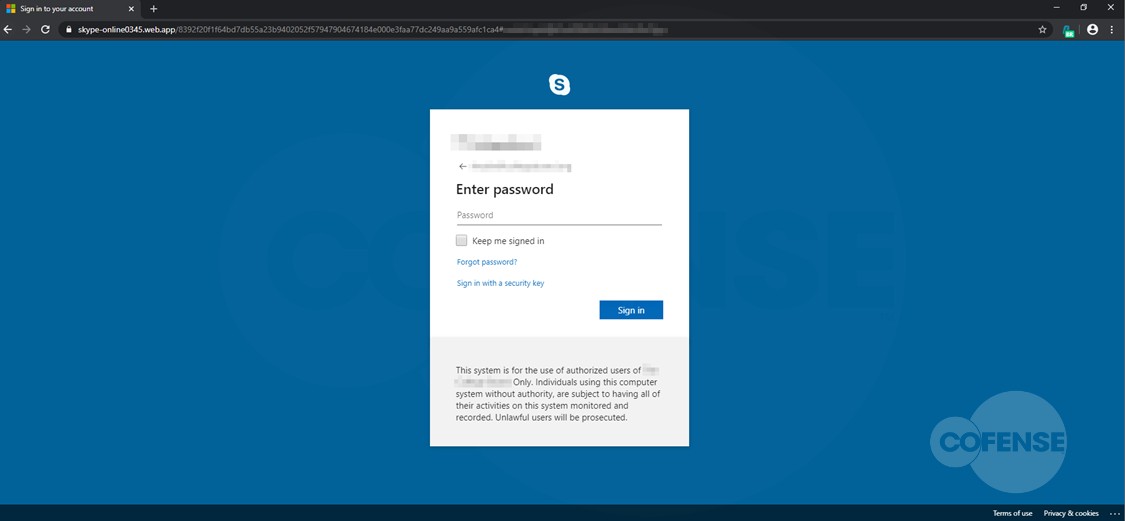
Clicking the link in the email, the user is shown an impersonation of the Skype login page. To add even further sense of authenticity, the threat actor adds the recipient’s company logo to the login box as well as a disclaimer at the bottom warning this page is for “authorized use” of that company’s users only.
Impact
- Credential theft
- Exposure of sensitive data
Indicators of Compromise
URL
- https[:]//jhqvy[.]app[.]link/VAMhgP3Mi5
- https[:]//skype-online0345[.]web[.]app
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.








