

Rewterz Threat Alert – Continuing Lazarus Attacks – NukeSped Sample
July 17, 2019
Rewterz Threat Alert – Critical Vulnerability affecting the Ad Inserter WordPress plugin
July 17, 2019
Rewterz Threat Alert – Continuing Lazarus Attacks – NukeSped Sample
July 17, 2019
Rewterz Threat Alert – Critical Vulnerability affecting the Ad Inserter WordPress plugin
July 17, 2019Severity
High
Analysis Summary
Smokeloader is a popular bot and a veteran in its field, this piece of malware is used mainly for loading other malicious software, usually obtained from a third party. At the same time, it has the capability of loading its own modules, allowing it to conduct a variety of actions without the usage of external components. The seller of Smokeloader (which is known by the handle SmokeLdr) is active in providing this malware as a service to this date.
New anti-hooking and anti-VM methods
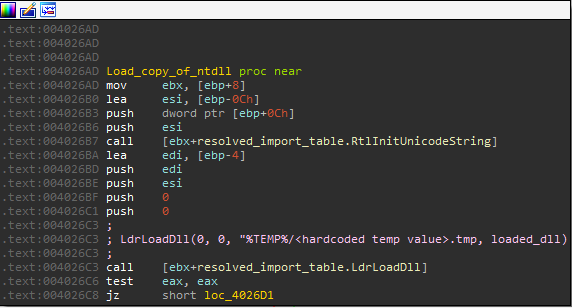
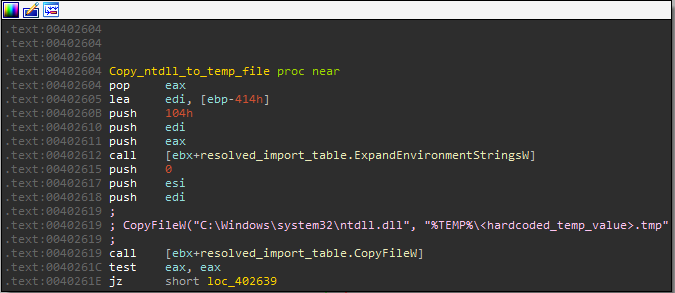
In order to avoid detection, Smokeloader first creates a new copy of ntdll.dll as a temporary file with a hardcoded name in the %APPDATA%\Local\Temp directory and then loads it using LdrLoadDll. Following this, it resolves all the functions it requires for its own usage and invokes them from the new copy of ntdll in its memory.
New Anti-Debug Method
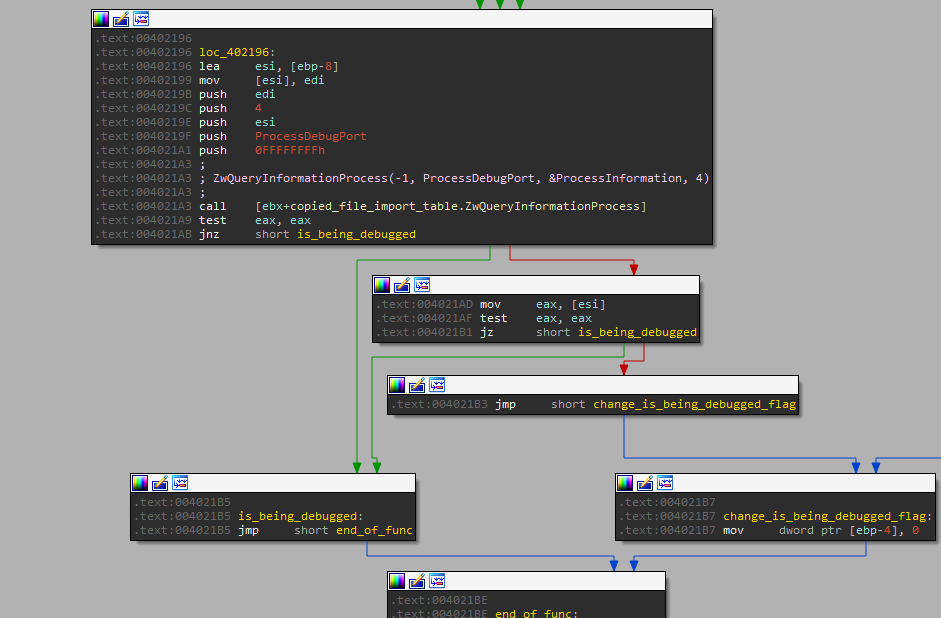
In addition to the anti-debug checks used in the older version of Smokeloader, the author added another method, which is rather well known. He made the malware call the API function NtQueryInformationProcess from the copy of ntdll, with an information class argument called ProcessDebugPort. The result provided by the function indicates if the debug port is used in the malware’s process, i.e. a debugger is attached to it. In the case that a non-null value is retrieved by this function, Smokeloader determines that it is indeed run by a debugger (and likely by a researcher), hence aborts its execution.
Impact
Exposure of sensitive information
Indicators of Compromise
Malware Hash (MD5/SHA1/SH256)
- 5FC6F24D43BC7CA45A81D159291955D1
- 20DD61FAE49972323BB9C38A46CA4C93
- E7680155F86AEAC74B65DA38143F7E9F
- AF93FD5C7810669D125EC9B0D6E28509
Remediation
- Block all threat indicators at your respective controls.
- Keep your software patches updated.
- Exercise caution caution when receiving messages from unknown third parties.








