

Rewterz Threat Advisory – CVE-2020-3125 – Cisco Adaptive Security Appliance Software Kerberos Vulnerability
May 7, 2020
Rewterz Threat Alert – ProLock RansomWare – IOCs
May 7, 2020
Rewterz Threat Advisory – CVE-2020-3125 – Cisco Adaptive Security Appliance Software Kerberos Vulnerability
May 7, 2020
Rewterz Threat Alert – ProLock RansomWare – IOCs
May 7, 2020Severity
Medium
Analysis Summary
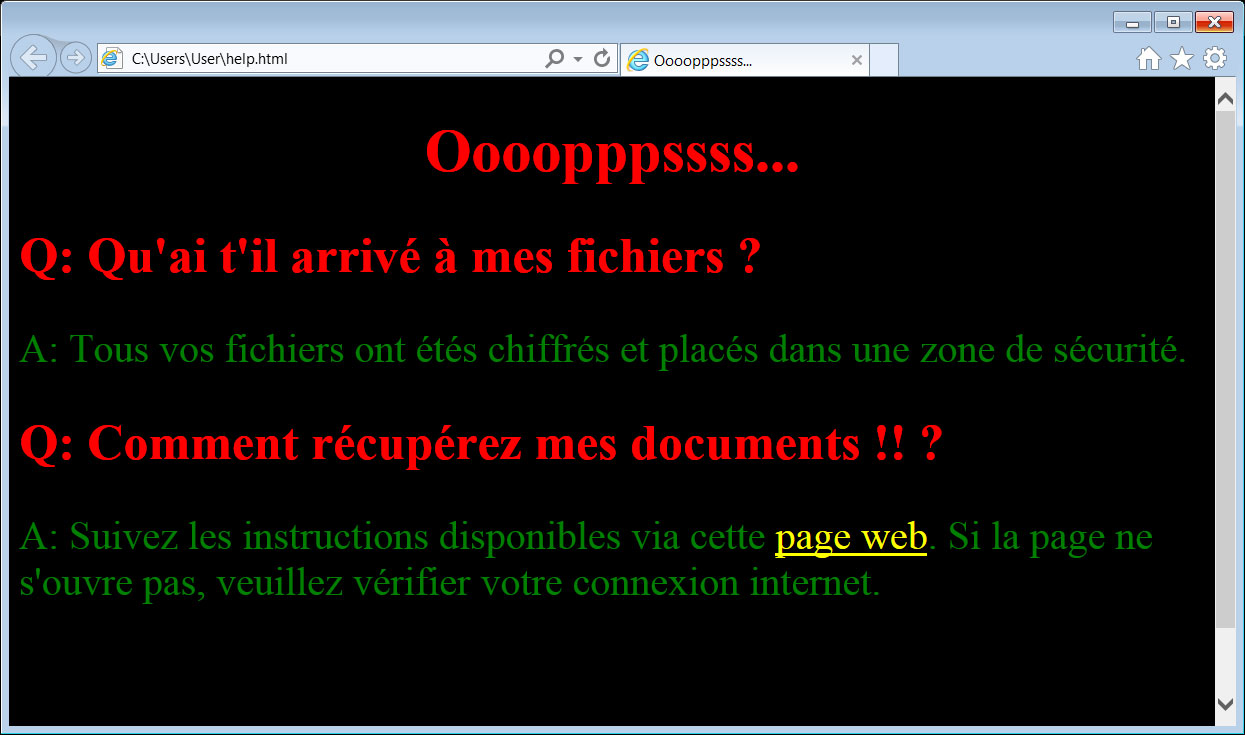
VCrypt, a new ransomware targeting French users, was analyzed by researchers and discovered to be using a unique mechanism to lock files. Upon execution, the malware drops a copy of the legitimate 7zip command line tool on the victim host. This tool is then used to archive user files with password-protection in place. After the files are archived, the originals are deleted. This process occurs only on the C: drive. On all other drives, the files are simply deleted without any archiving taking place. The ransom letter is an HTML file opened in Internet Explorer after the files have been archived. It is written in French and requests victims visit a website to receive decryption instructions.
Impact
| Create password-protected archives |
Indicators of Compromise
MD5
d32ff14c37b0b7e6c554ce3de5a85454
SHA-256
e9056b5596854e3473033e3b28577c83a70f1b5be20e4b1cf529688ad7591b70
SHA1
66667fc7c218d4d07adea4092d7b94861eaf168c
Remediation
| Block all threat indicators at your respective controls. Always be suspicious about emails sent by unknown senders. Never click on the links/attachments sent by unknown senders. |








