

Rewterz Threat Alert – Threat Group Gorgon Continues It’s Activity to Deliver Trojans, RATs
October 3, 2019
Rewterz Threat Alert – Molerats spear phishing campaign
October 3, 2019
Rewterz Threat Alert – Threat Group Gorgon Continues It’s Activity to Deliver Trojans, RATs
October 3, 2019
Rewterz Threat Alert – Molerats spear phishing campaign
October 3, 2019Severity
Medium
Analysis Summary
A ransomware from 2013 has resurfaced called FTCode and is completely PowerShell based, which means it can encrypt the computer without downloading any additional components. Possibly the ransomware wasn’t a big success in 2013 due to PowerShell not being as prevalent as it is today. This ransomware is being distributed through spam containing malicious Word docs that are targeting Italian users. The spam variants are pretending to be invoices, document scans, and resumes for applying for a job (curriculum). Below is a spam email pretending to be a Fattura, or invoice, that the victim needs to pay.
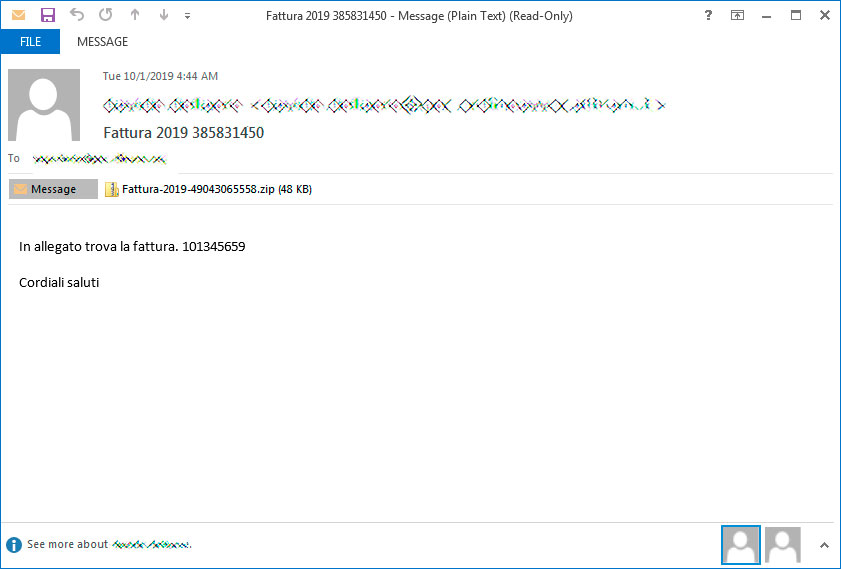
If they open the attachment, they will be shown a Word document stating that they need to Enable Content in order to continue.
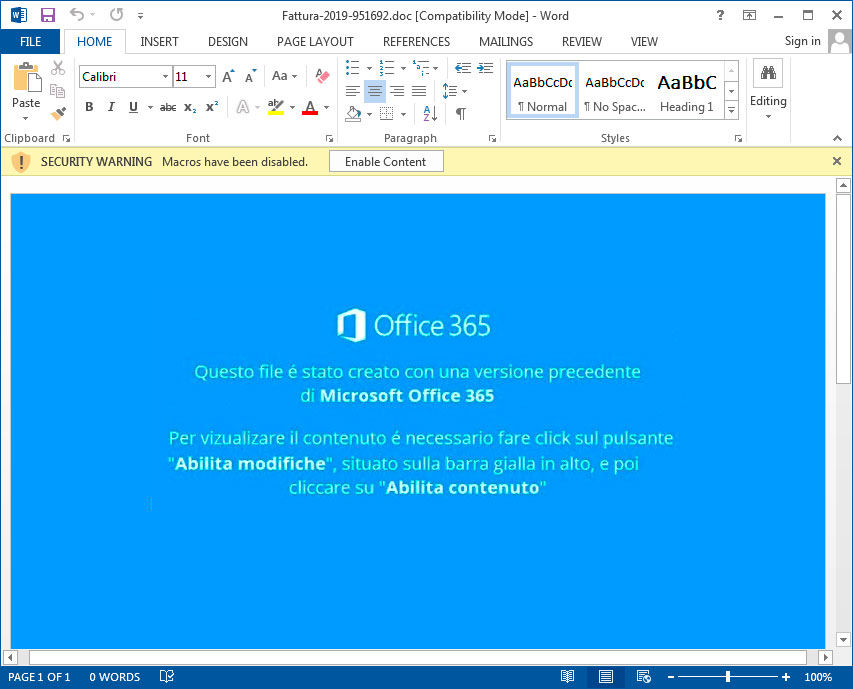
Once content is enabled, malicious macros will launch that execute a PowerShell command that downloads and installs JasperLoader malware downloader and then encrypts the computer.
After the VBS script is downloaded, it will be configured to automatically run through a scheduled task named WindowsApplicationService and via a shortcut created in the Startup folder. The PowerShell script then moves on to the ransomware portion, where it will check if the file C:\Users\Public\OracleKit\w00log03.tmp exists. This file acts as a killswitch and if it exists, the script will not encrypt the computer.
If the file does not exist, it will generate a encryption key and send it to the attacker’s command and control server. This means that if you are monitoring your traffic during the time of encryption you could recover the encryption key. After encryption, a .FTCODE extension is added to the filenames and a READ_ME_NOW.htm ransom note is created in every folder.
![ransom_note_image[1].png](https://www.bleepstatic.com/images/news/ransomware/f/FTCode/ransom_note_image%5B1%5D.png)
When victims visit the Tor payment site, they will be given a bitcoin address and ransom amount that they must send in order to purchase the decryptor.
Impact
Files Encryption
Indicators of Compromise
IP(s) / Hostname(s)
- home[.]ktxhome[.]com
- home[.]selltokengarff[.]com
- connect[.]southerntransitions[.]com
- home[.]southerntransitions[.]net
- connect[.]simplebutmatters[.]com
Malware Hash (MD5/SHA1/SH256)
- b09bc9a25090cada55938367c7f12e692632afa2ed46d5e90eba29da84befafd
- a5af9f4b875be92a79085bb03c46fe5c
Remediation
- Block the threat indicators at their respective controls.
- Do not download email attachments coming from untrusted sources.
- Do not enable content/macros for files downloaded from untrusted sources.








