

Rewterz Threat Alert – Fake Tax Calculator Installs xRAT
August 20, 2019
Rewterz Threat Advisory – Malicious Custom 404 Pages Used in Phishing Attacks
August 20, 2019
Rewterz Threat Alert – Fake Tax Calculator Installs xRAT
August 20, 2019
Rewterz Threat Advisory – Malicious Custom 404 Pages Used in Phishing Attacks
August 20, 2019Severity
Medium
Analysis Summary
Hackers actively distributing the bank Win32.Bolik.2 banking Trojan via the nord-vpn[.]club website, an almost perfect clone of the official nordvpn[.]com site used by the popular NordVPN VPN service.
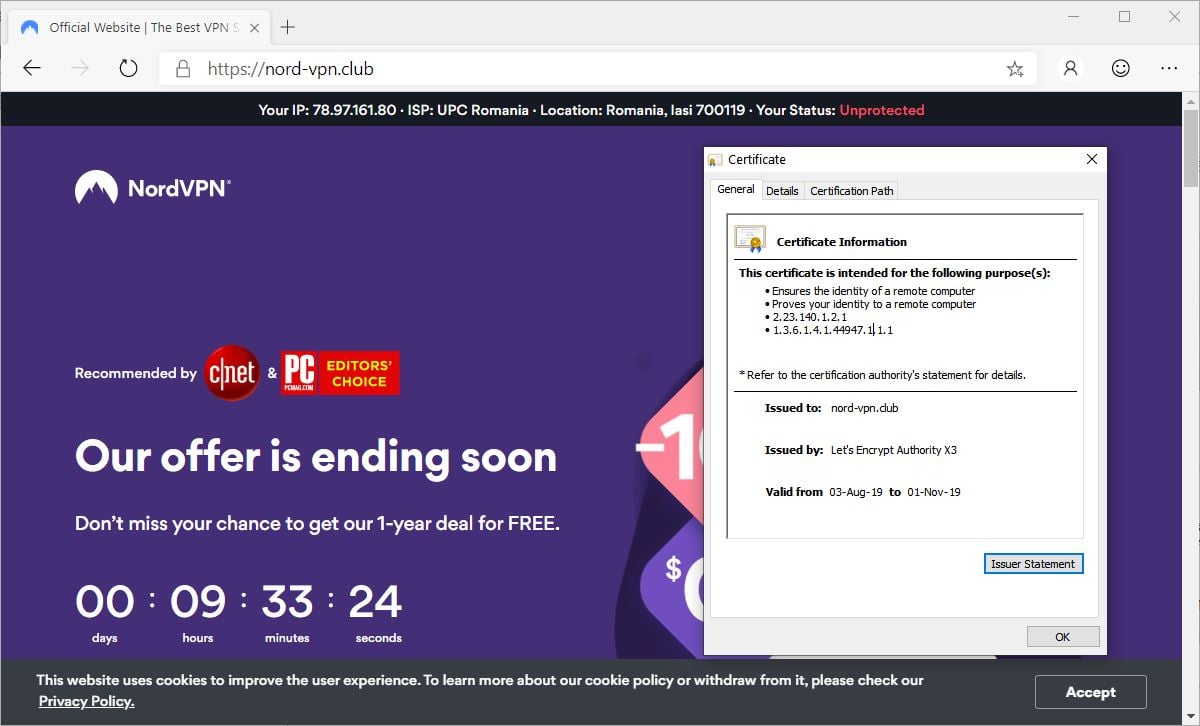
The cloned website also has a valid SSL certificate issued by open certificate authority Let’s Encrypt on August 3, with an expiration date of November 1. Win32.Bolik.2 trojan is an improved version of Win32.Bolik.1 and has qualities of a multicomponent polymorphic file virus.
Using this malware, hackers can perform web injections, traffic intercepts, keylogging and steal information from different bank-client systems.The operators behind this malicious campaign have launched their attacks on August 8, they are focusing on English-speaking targets and, according to the researchers, thousands have already visited the nord-vpn[.]club website in search of a download link for the NordVPN client.
A cocktail of banking trojans and information stealers—Win32.Bolik.2 and Trojan.PWS.Stealer.26645 (Predator The Thief)—was also delivered to their targets by the same hacker group behind this malware campaign with the help of two other cloned websites in late June 2019.
Impact
- Web injections
- Traffic intercepts
- Keylogging
- Information theft
Remediation
- Always cross check files before downloading from internet.
- Always scan your downloaded files before executing.








