

Rewterz Threat Alert – Android SLocker Variant Uses Covid 19 to Take Android Hostage
May 5, 2020
Rewterz Threat Alert – Covid-19 Malicious URLs
May 5, 2020
Rewterz Threat Alert – Android SLocker Variant Uses Covid 19 to Take Android Hostage
May 5, 2020
Rewterz Threat Alert – Covid-19 Malicious URLs
May 5, 2020Severity
Medium
Analysis Summary
A highly convincing phishing campaign is using cloned imagery from automated Microsoft Teams notifications in attacks that attempt to harvest Office 365 credentials. A recent spike since the start of this Covid-19 pandemic has caused a bit of concern for the Microsoft Office 365 users. The phishing emails that spoof Microsoft Teams file share and audio chat notifications have so far landed in the inboxes of 15,000 to 50,0000 targets based on stats from researchers.
Various online collaboration services phishing emails are being used to lure users to chat with their colleagues, friends, and family member and makes them prone from ignoring any signals that would otherwise allow them to realize they’re being attacked.
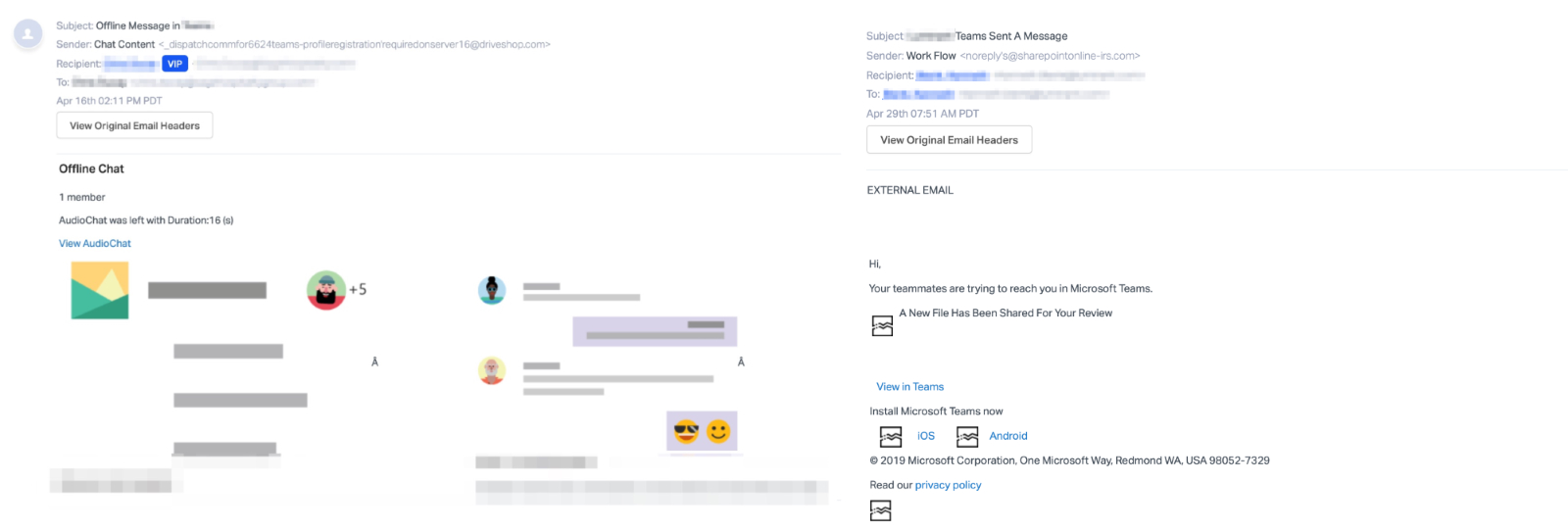
To evade email protection services, the attackers also use several URL redirects with the end goal of hiding the URL used to host the phishing campaign.
Impact
- Credential theft
- Exposure of sensitive data
Remediation
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.








