

Rewterz Threat Advisory – CVE-2020-3119 – Cisco NX-OS Software Cisco Discovery Protocol Remote Code Execution
February 13, 2020
Rewterz Threat Alert – Satan ransomware rebrands as 5ss5c ransomware
February 17, 2020
Rewterz Threat Advisory – CVE-2020-3119 – Cisco NX-OS Software Cisco Discovery Protocol Remote Code Execution
February 13, 2020
Rewterz Threat Alert – Satan ransomware rebrands as 5ss5c ransomware
February 17, 2020Severity
High
Analysis Summary
Emotet has found a new attack vector: using already infected devices to identify new victims that are connected to nearby Wi-Fi networks. Emotet sample leverages a “Wi-Fi spreader” module to scan Wi-Fi networks, and then attempts to infect devices that are connected to them. This module has been running “unnoticed” for around two years. The development marks an escalation of Emotet’s capabilities, as networks in close physical proximity to the original victim are now susceptible to infection. The updated version of the malware works by leveraging an already compromised host to list all the nearby Wi-Fi networks. To do so, it makes use of the wlanAPI interface to extract the SSID, signal strength, the authentication method (WPA, WPA2, or WEP), and mode of encryption used to secure passwords. The worm attempts to connect to the networks by performing a brute-force attack using passwords obtained from one of two internal password lists. Provided the connection fails, it moves to the next password in the list. It’s not immediately clear how this list of passwords was put together.
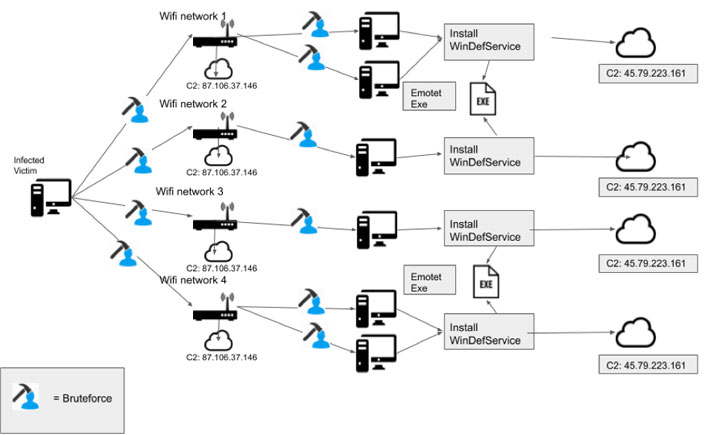
If the operation succeeds, the malware connects the compromised system on the newly-accessed network and begins enumerating all non-hidden shares. It then carries out a second round of brute-force attack to guess the usernames and passwords of all users connected to the network resource. Successful brute force then leads to next phase by installing malicious payloads — called “service.exe” — on the newly infected remote systems. To cloak its behavior, the payload is installed as a Windows Defender System Service (WinDefService). In addition to communicating with a command-and-control (C2) server, the service acts as a dropper and executes the Emotet binary on the infected host. The malware can also be detected by actively monitoring processes running from temporary folders and user profile application data folders.
Impact
- Infection of Wi-Fi networks
- Unauthorized Access
Indicators of Compromise
Source IP
- 87.106.37.146
- 45.79.223.161
Remediation
- Block the threat indicators at their respective controls.
- Implement very strong passwords for wireless networks.








