

Rewterz Threat Alert – Qbot/Qakbot Attempts to Evade Detection By Overwriting Itself
October 2, 2019
Rewterz Threat Advisory – CVE-2019-12689 – Cisco Firepower Management Center Remote Code Execution Vulnerability
October 3, 2019
Rewterz Threat Alert – Qbot/Qakbot Attempts to Evade Detection By Overwriting Itself
October 2, 2019
Rewterz Threat Advisory – CVE-2019-12689 – Cisco Firepower Management Center Remote Code Execution Vulnerability
October 3, 2019Severity
High
Analysis Summary
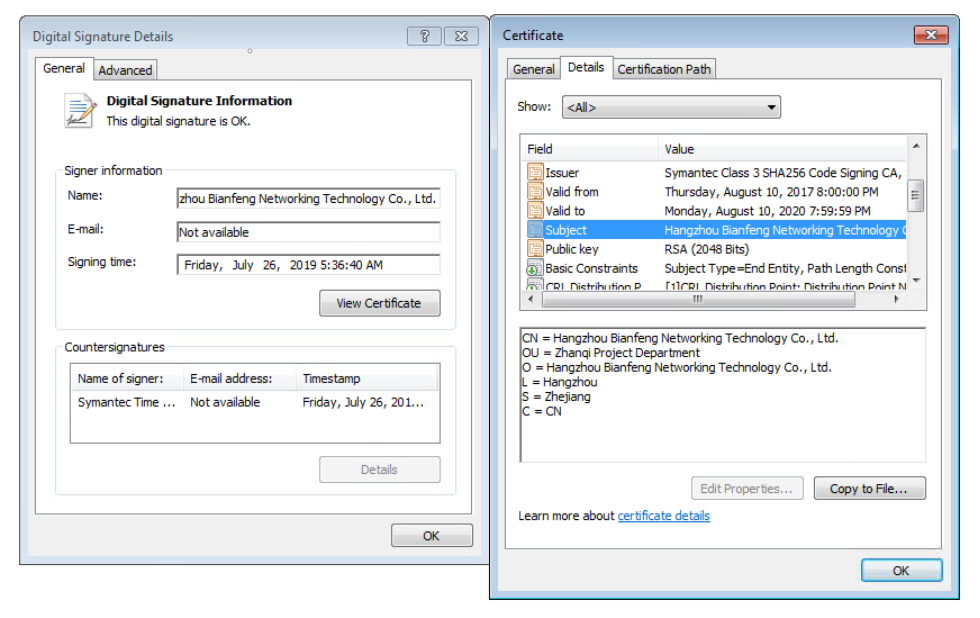
On discovery of a suspicious binary, MeltX0R researchers were able to identify malware and infrastructure being used by the Emissary Panda APT group in a recent campaign against unknown targets. Emissary Panda is also known as APT27, BRONZE UNION, Iron Tiger, LuckyMouse, TG-3390, and Threat Group-3390. The initially discovered binary was an executable file masquerading as a legitimate Microsoft utility but signed with a Chinese certificate. Execution of the binary results in privilege escalation followed by the dropping of a DLL in the System32 folder and a batch file in the victim’s temp directory. The DLL is then loaded using rundll32, at which point persistence is established via a new service. The aforementioned batch file is responsible for clearing the attacker’s tracks by deleting both the initial binary and itself. Next, the DLL is loaded a second time, this time by svchost. Running under svchost, the DLL file drops autocheck.sys, reads the hosts file, and initiates communication with its C2 over HTTP, HTTPS, and DNS. At the time of analysis, the researchers were unable to generate a response from the C2 server so the secondary payload was unable to be identified. Based on known TTPs used by Emissary Panda and similar samples to the one obtained for this researcher, MeltX0R identified that the initial payload was the ZxShell RAT installer.
Impact
- Exposure of sensitive information
- Privilege escalation
Indicators of Compromise
Malware Hash (MD5/SHA1/SH256)
- 70cff7c176c7df265a808aa52daf6f34
- 37fc73c754ef2706659a18837a90ddaa
- a9c2ff438c73e865624eeb0763235a14
- 1b2d75f9c7717f377100924cdbdb10b1
- 850df4a726a71f50d3cc7192c8cf7e6a
- b7f958f93e2f297e717cffc2fe43f2e9
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.








