

Rewterz Threat Alert – Mobile Cyberespionage Campaign Distributed Through CallerSpy
December 3, 2019
Rewterz Threat Alert – Magecart Attacks Hacking Websites to Steal Customer Payment Info
December 4, 2019
Rewterz Threat Alert – Mobile Cyberespionage Campaign Distributed Through CallerSpy
December 3, 2019
Rewterz Threat Alert – Magecart Attacks Hacking Websites to Steal Customer Payment Info
December 4, 2019Severity
Medium
Analysis Summary
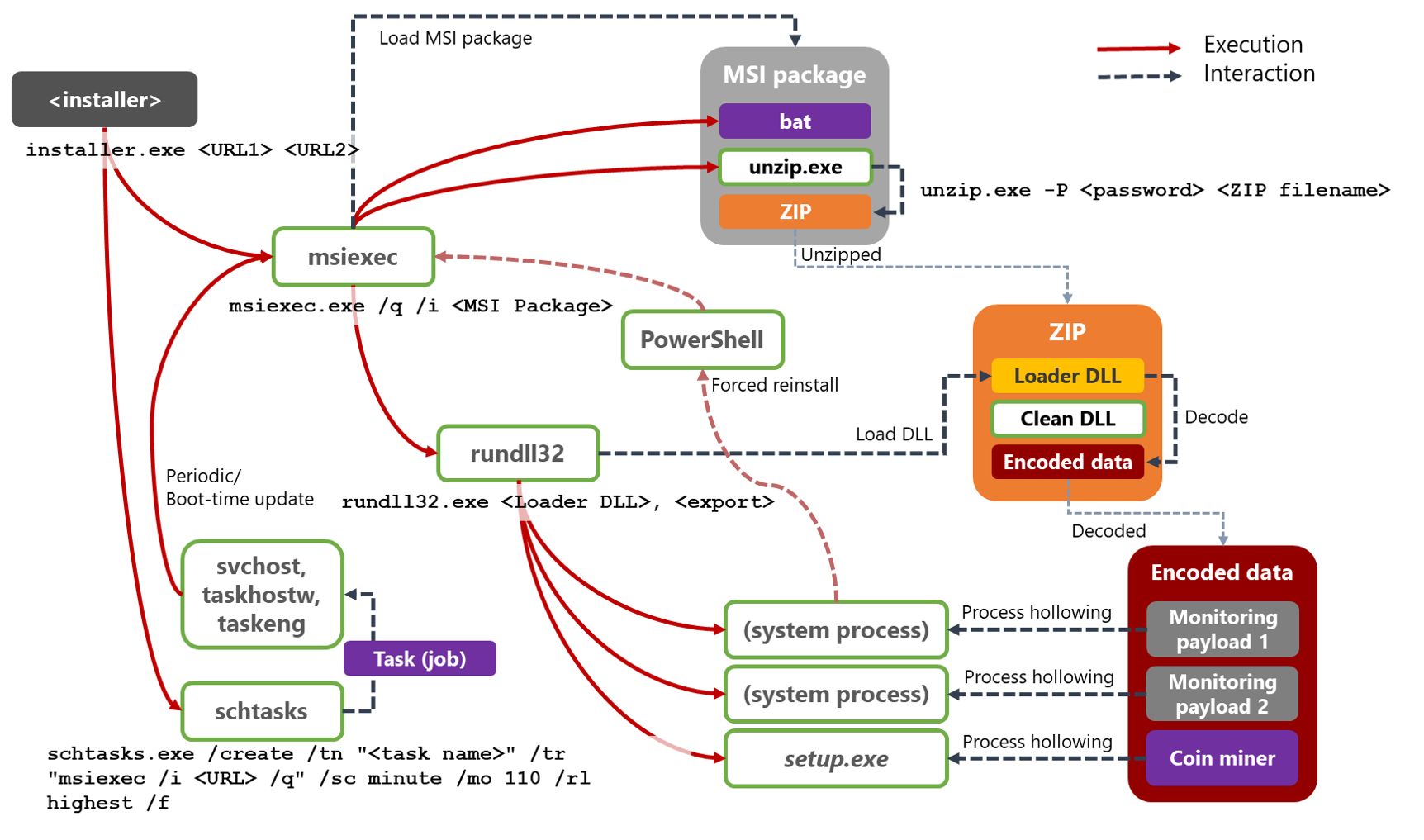
Microsoft’s Defender ATP Research team detected a campaign they labeled Dexphot. At that point, the Microsoft team began tracking this campaign which turned out to be a polymorphic attack that deployed files that changed every half hour. Dexphot used multiple levels of obfuscation, encryption, and random file names to evade detection. Once a foothold had been gained on a victim system, it then used fileless techniques to further evade detection and forensics. Legitimately running applications were injected with the malware code to disguise the malicious behavior. Services that monitored the malware’s activity and that executed scheduled tasks to re-infect a system were deployed to ensure that the final payload, a cryptominer, was allowed to continue running. As time went by, the malware was upgraded, new running processes were targeted, and efforts to work around defensive measures were added. Except for the installer portion of the infection, all other executables are legitimate applications, such as msiexec.exe, unzip.exe, rundll32.exe, schtasks.exe, and powershell.exe. Applications targeted for its process hollowing technique included svchost.exe, tracert.exe, and setup.exe.
Impact
Coin miner
Indicators of Compromise
SHA-256
- 22beffb61cbdc2e0c3eefaf068b498b63a193b239500dab25d03790c467379e3
- 504cc403e0b83233f8d20c0c86b0611facc040b868964b4afbda3214a2c8e1c5
- 537d7fe3b426827e40bbdd1d127ddb59effe1e9b3c160804df8922f92e0b366e
- 65eac7f9b67ff69cefed288f563b4d77917c94c410c6c6c4e4390db66305ca2a
- 72acaf9ff8a43c68416884a3fff3b23e749b4bb8fb39e16f9976643360ed391f
- aa5c56fe01af091f07c56ac7cbd240948ea6482b6146e0d3848d450977dff152
- ba9467e0d63ba65bf10650a3c8d36cd292b3f846983032a44a835e5966bc7e88
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.








