

Rewterz Threat Alert – Emotet Malware – IoCs
November 11, 2019
Rewterz Threat Alert – Titanium Malware: the Platinum group strikes again
November 11, 2019
Rewterz Threat Alert – Emotet Malware – IoCs
November 11, 2019
Rewterz Threat Alert – Titanium Malware: the Platinum group strikes again
November 11, 2019Severity
High
Analysis Summary
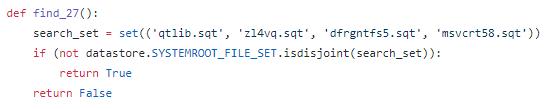
In April 2017, ShadowBrokers published their well-known ‘Lost in Translation’ leak, which, among other things, contained an interesting script that checked for traces of other APTs in the compromised system.
Spear phishing was used to spread the malware. A letter was prepared separately for each victim to grab their attention and prompt them to open an attached malicious Microsoft Office document.
Each malware sample was compiled immediately before being sent and included the latest available version of the malware executable. Since the framework evolved from 2009 to 2017, the last releases are totally different from the first ones, so the current report details only the latest available version of the malware used until 2017.
The executable file embedded in the documents extracts two malicious files from itself, updater.mod and glue30.dll, and saves them in the working directory of the malware – %USERPROFILE%\AppData\Roaming\Microsoft\Windows\Reorder.
After that, it copies the legitimate rundll32.exe executable into the same directory and uses it to run the updater.mod library.
Impact
Credentials theft
Indicators of Compromise
MD5
- 1addee050504ba999eb9f9b1ee5b9f04
- 4b71ec0b2d23204e560481f138833371
- 4e24b26d76a37e493bb35b1a8c8be0f6
- 405ef35506dc864301fada6f5f1d0711
- 764a4582a02cc54eb1d5460d723ae3a5
- c2edda7e766553a04b87f2816a83f563
- 71d36436fe26fe570b876ad3441ea73c
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.








