

Rewterz Threat Alert – Everis Bitpaymer Ransomware – IOC’s
November 7, 2019
Rewterz Threat Alert – PKPLUG: Chinese Cyber Espionage Group Attacking Asia
November 7, 2019
Rewterz Threat Alert – Everis Bitpaymer Ransomware – IOC’s
November 7, 2019
Rewterz Threat Alert – PKPLUG: Chinese Cyber Espionage Group Attacking Asia
November 7, 2019Severity
High
Analysis Summary
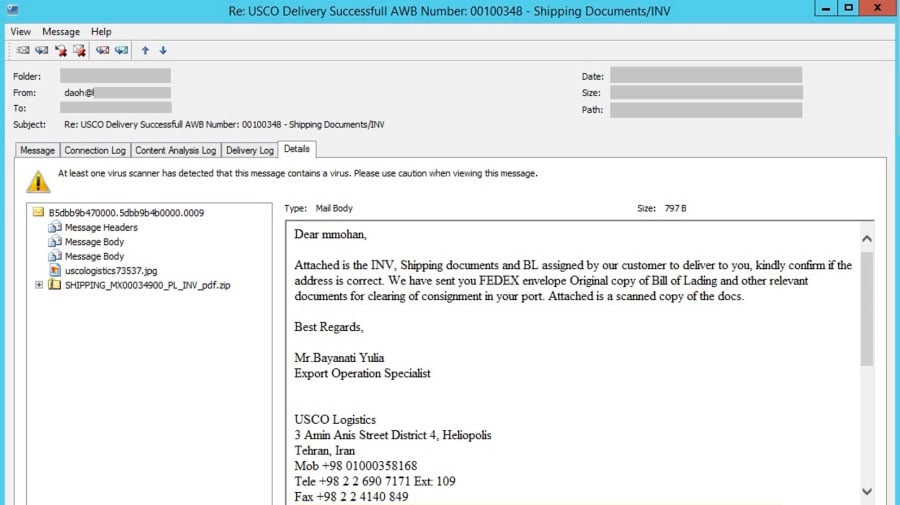
A new phishing campaign is discovered using a ZIP file that was designed to bypass secure email gateways to distribute the NanoCore RAT. It’s a spam email pretending to be shipping information from an Export Operation Specialist of USCO Logistics. It looked suspicious as the ZIP’s file size was greater than its uncompressed content. Below is the email body emphasizing on the attachment.
After the first EOCD comes some extra data – another ZIP file structure. It turns out that the first ZIP structure is for the image file “order.jpg” while the second one is for an executable file “SHIPPING_MX00034900_PL_INV_pdf.exe“. The image file is benign while the “SHIPPING_MX00034900_PL_INV_pdf.exe“ is a NanoCore RAT. This remote access trojan has the capability that allows an attacker to completely take control of the compromised machine. It connects to its command and control server at 194.5.98[.]85 on port 11903. This NanoCore RAT is version 1.2.2.0.
TrustWave determined that only certain versions of the PowerArchiver, WinRar, and older 7-Zip utilities properly extracted the NanoCore executable.
Impact
- Unauthorized Access
- Device Takeover
Indicators of Compromise
Filename
- SHIPPING_MX00034900_PL_INV_pdf.zip
- SHIPPING_MX00034900_PL_INV_pdf.exe
MD5
- 5e67dc41d0826d86ff6eb5fa03fcd836
- 7f8b1f146b1495fe8d81952b06c0b45b
SH256
- e90b970c5e5ddf821d6f9f4d7d710d6dc01d59b517e8fb39da726803dc52b5ad
- 91d539af85599fda3fb2fb023866b72d64adc2bb95f6153e655cc844564de02e
SHA1
- 9474e1517c98d4165300a49612888d16643efbf6
- 06b80f9a0fba1d830dcf2ecf225ed1d19060589a
Source IP
194.5.98[.]85
Remediation
- Block the threat indicators at their respective controls.
- Do not download/execute files attached in untrusted emails.
- Closely monitor all communication at port 11903.








