

Rewterz Threat Alert – LNK files Targeting Maldives Government
January 14, 2020
Rewterz threat Advisory – CVE-2019-10940 – ICS: Siemens SINEMA Server Incorrect privilege assessment
January 15, 2020
Rewterz Threat Alert – LNK files Targeting Maldives Government
January 14, 2020
Rewterz threat Advisory – CVE-2019-10940 – ICS: Siemens SINEMA Server Incorrect privilege assessment
January 15, 2020Severity
High
Analysis Summary
RootKit module of ZxShell RAT used by Emissary Panda (APT27), of which there is a relatively recent sample.
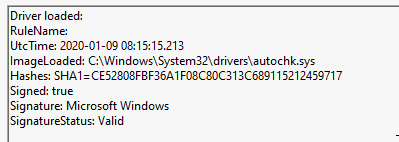
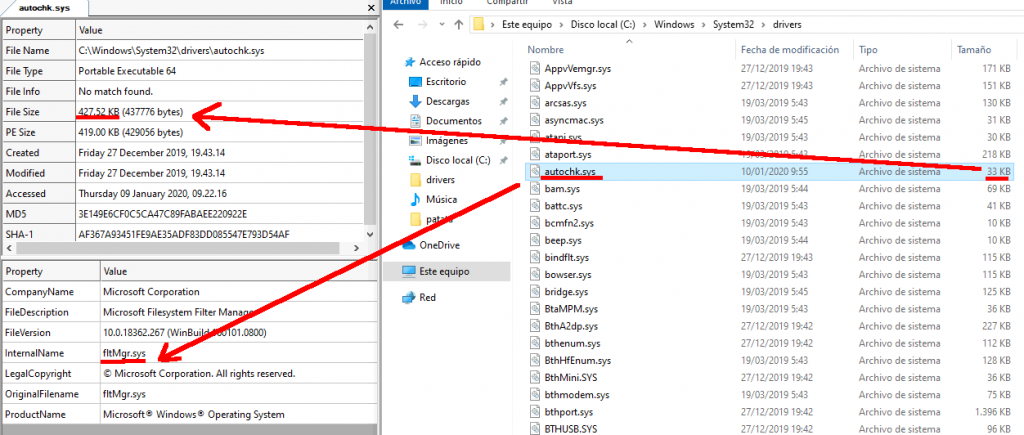
This rootkit is a very simple, it does not employ any uber fancy methods or something. The name of the driver is “autochk.sys” – that’s why we’ll call it the autochk rootkit.
The rootkit implements 2 functionalities:
- File Redirection – Redirect malicious files to benign files. If you try to call CreateFile() to open a malicious file you’ll get a handle to a benign file.
- Network Connection Hiding – Hide network connections from tools like netstat.
Impact
Access to sensitive information
Indicators of Compromise
MD5
- 96fb28626f2db5e378cf48960230f712
- 956c44a4ec1ba56c75cb4558ed3a653e
SHA-256
- 42eab05c611bf24d86bb6c985caa2ad7380ed7d98340c7f08de9361be14dc244
- 9b7c1e37d5f56cc0b5e5e22ce9805e237a189297e78405b9c392a0953b6e0321
SHA1
- c602290cb2cd1d2ca5c9c8571868495fe7518d9c
- ce52808fbf36a1f08c80c313c689115212459717
Remediation
- Block all threat indicators at your respective controls.
- Always be suspicious about emails sent by unknown senders.
- Never click on the links/attachments sent by unknown senders.








