Severity
High
Analysis Summary
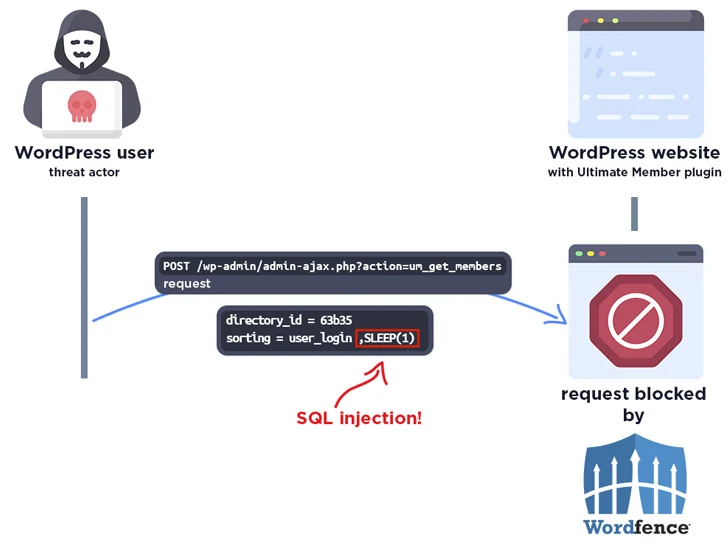
A critical security flaw tracked as CVE-2024-1071 has been identified in the Ultimate Member WordPress plugin, affecting versions 2.1.3 to 2.8.2 and potentially exposing over 200,000 installations to SQL Injection attacks. As discovered by researchers, the flaw allows unauthenticated attackers to manipulate SQL queries, leading to data extraction from the database. Notably, the vulnerability targets users who have enabled the “Enable custom table for user meta” option in plugin settings.
Wordfence, a WordPress security firm, issued an advisory urging immediate updates to version 2.8.3, released on February 19, to patch the vulnerability. The update follows responsible disclosure on January 30, 2024, with Wordfence already intercepting one exploit attempt within 24 hours of disclosure.
This incident echoes a previous security lapse, CVE-2023-3460, exploited in July 2023, which enabled threat actors to gain admin privileges on affected sites. Concurrently, WordPress sites are being hijacked for crypto drainer schemes, including the injection of Angel Drainer or redirection to Web3 phishing sites
Moreover, a new drainer-as-a-service scheme called CG (CryptoGrab) has surfaced, facilitating fraudulent operations via a Telegram bot. The bot offers tools to clone legitimate websites, set up wallet addresses for fraudulent transactions, and deploy Cloudflare protection, streamlining the exploitation process. Threat actors exploit compromised social media accounts, notably X (formerly Twitter), to disseminate cloned sites.
Overall, the WordPress community faces ongoing security challenges with vulnerabilities like CVE-2024-1071, underscoring the importance of prompt updates to mitigate risks. The emergence of sophisticated drainer schemes further exacerbates security concerns, necessitating proactive measures to safeguard website integrity and user assets.
Impact
- Unauthorized Access
- Data Manipulation
- Data Exfiltration
Indicators of Compromise
CVE
- CVE-2024-1071
Affected Vendors
WordPress
Affected Products
- Ultimate Member Plugin for WordPress 2.1.3 – 2.8.2
Remediation
- Refer to WordPress Plugins Directory for patch, upgrade, or suggested workaround information.
- Implement multi-factor authentication to add an extra layer of security to login processes.
- Regularly monitor network activity for any unusual behavior, as this may indicate that a cyberattack is underway.
- Organizations need to stay vigilant and follow best practices for cybersecurity to protect their systems and data from potential threats. This includes regularly updating software and implementing strong access controls and monitoring tools.
- Develop a comprehensive incident response plan to respond effectively in case of a security breach or data leakage.
- Maintain regular backups of critical data and systems to ensure data recovery in case of a security incident.
- Adhere to security best practices, including the principle of least privilege, and ensure that users and applications have only the necessary permissions.
- Establish a robust patch management process to ensure that security patches are evaluated, tested, and applied promptly.
- Conduct security audits and assessments to evaluate the overall security posture of your systems and networks.
- Implement network segmentation to contain and isolate potential threats to limit their impact on critical systems.

